*Mlwq is a variant of Stop/DJVU. Source of claim SH can remove it.
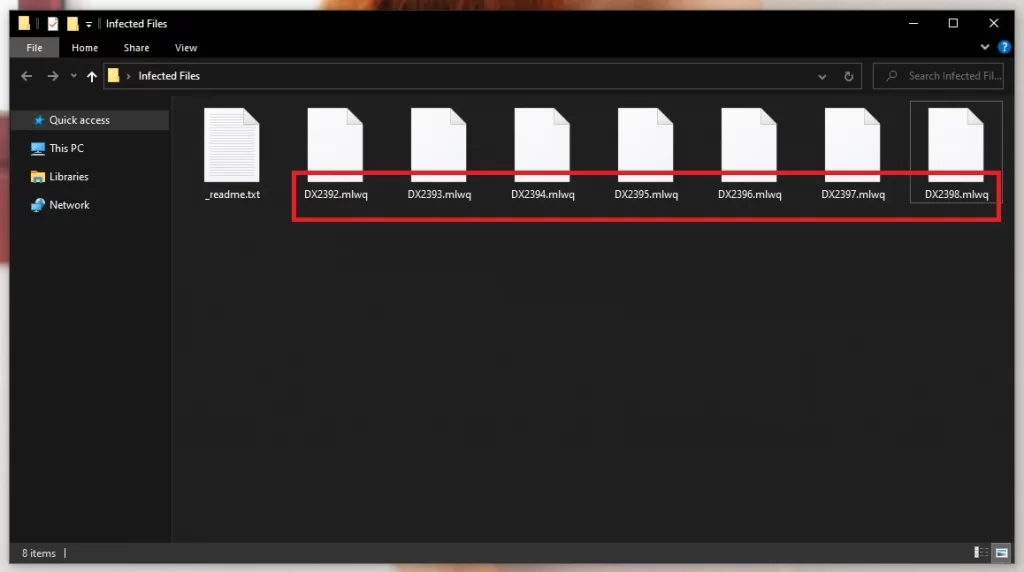
Mlwq File
Imagine a scenario where, without warning, each important file on your system has become an inaccessible Mlwq file. This is the reality for victims of this malicious ransomware designed to encrypt files, turning them into encrypted files that are virtually impossible to open without a unique key. Behind the scenes, this ransomware uses complex algorithms to alter the data, effectively holding it hostage. What is startling is the relentless evolution of this malware, adopting more robust encryption methods with each iteration. While facing such a ransomware attack and seeing that each of your files has become a Mlwq file can feel isolating, the community of cybersecurity experts is persistently working to devise solutions to these menacing encryption tactics.
How to decrypt Mlwq ransomware files?
To decrypt Mlwq ransomware files, it’s best to first try using the free recovery tool that we’ve suggested in the guide. It may help you recover some or, if you are lucky, all important files the virus has locked. The alternative option is to pay the Mlwq ransom, but we stringly advise against it, as it also doesn’t guarantee file recovery, but if you opt for it, your money will be gone either way.
How to remove the Mlwq ransomware virus and restore the files?
To remove the Mlwq ransomware and attempt to restore your files, you must first check your entire system for traces of the malware and delete everything suspicious. The guide we’ve prepared here will show you how to do that. Then you can try using the recommended free data recoovery tool too hopefully gain some of your data back.
Mlwq Virus
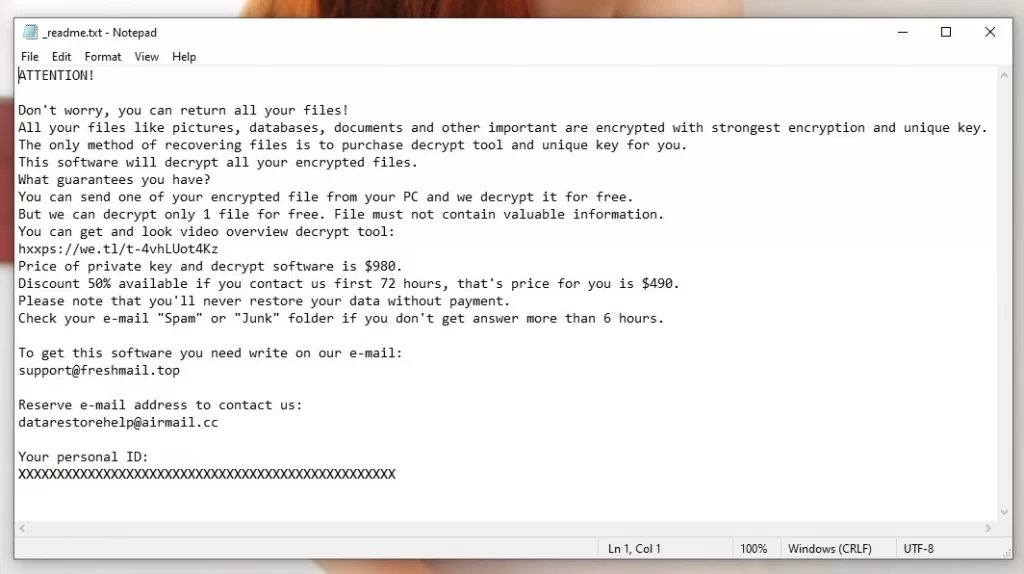
In the digital realm, the Mlwq virus stands as a formidable adversary. This ransomware operates on a straightforward yet cruel principle: encrypting files and demanding a ransom for their release. The crux of its strategy lies in exploiting the emotional turmoil and urgency spurred by losing access to crucial data. Like is the case with other similar threats, such as Ttza and Ttrd, the primary goal of the Mlwq virus remains a financial gain, driven by a merciless exploitation of individual and corporate vulnerability. It is a scheme steeped in uncertainty, as meeting the monetary demands offers no assurance of regaining the lost files, revealing a landscape fraught with deceit and manipulation.
Mlwq
The infiltration routes of the Mlwq ransomware are varied and often deceptive, including strategies such as spear phishing and exploiting software vulnerabilities. The battle against such incursions demands a multifaceted approach to prevention. It involves nurturing a culture of caution, encouraging regular software updates, avoiding sites with questionable reputation, and cultivating a discerning eye for potential phishing attempts. Another pivotal strategy to prevent Mlwq attacks rests in the deployment of robust antivirus solutions capable of detecting and neutralizing threats early on. Through collective vigilance and adherence to cybersecurity norms, the fortification against this ransomware and its ilk becomes a tangible reality.
.Mlwq
When files get branded with the .Mlwq extension, it serves as a blatant announcement of the ransomware’s ruthless encroachment. This suffix signals an encryption process that has rendered files inaccessible, yet not entirely damaged. Despite the ominous undertone of this extension, it is essential to remember that avenues for potential recovery do exist. However, navigating the recovery landscape and trying to rid your files of the .Mlwq extension comes with a fair share of uncertainty, as successful restoration is not guaranteed. In the face of such predicaments, seeking expert advice and exploring all possible avenues of file recovery emerges as a pragmatic approach, albeit with a cautious optimism.
Mlwq Extension
There’s something about the Mlwq extension that causes a lot of stress, and rightly so. This tag, appended by the ransomware of the same name, essentially holds files hostage, albeit without damaging them. These files remain in a kind of limbo, unharmed yet unreachable, like a book in a locked cabinet. Though it can be tempting to pay the ransom immediately in desperation, this approach should generally be avoided, if possible. Resorting to ransom payment as a way to deal with the Mlwq extension is a last-ditch effort, with no assurance of getting the locked data back. It’s always better to explore all the other avenues first, keeping the ransom route as a distant, final option.
Mlwq Ransomware
The tactics of Mlwq ransomware are as sneaky as they come. Its infiltration into systems can occur through deceptive emails, dubious downloads, or exploiting vulnerabilities in the existing system setup. It’s like a silent burglar, leaving signs of its presence through system sluggishness, strange file extensions, and an inability to access certain files. One urgent measure to help mitigate the harm caused by the Mlwq Ransomware is to disconnect external drives and devices to limit the damage radius. Spotting the signs early can be a real game-changer, helping to curb the encryption process before it seals away all the precious data in its unyielding grasp.
What is Mlwq file?
A “Mlwq file” isn’t something anyone wants to encounter, but understanding it is the first step to battling this ransomware. Essentially, it is a document that has come under the control of the virus, finding itself encrypted and locked away from its user. While the encryption placed on a Mlwq file does not alter the content of the file, it renders it inaccessible, forcing the victim into a game of digital ransom and negotiation. Though the situation may seem dire, it’s a call to arms to reinforce digital defenses and explore recovery strategies with a calm, focused approach. As for the possible ways to handle the current situation, be sure to check the instructions we’ve prepared next.
SUMMARY:
| Name | Mlwq |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Mlwq is a variant of Stop/DJVU. Source of claim SH can remove it.
Before you start
You should take into account the following four points before starting the removal process of Mlwq.
- First and foremost, if there are any external HDDs, phones, tablets, flash memory sticks, or other devices that can store files attached to your PC, disconnect them immediately to prevent the virus from locking up the files stored in them.
- Disconnect the infected computer from the Internet – this will ensure Mlwq is not able to receive new instructions from its server.
- Though it’s recommended to not pay the ransom, if you still decided to do it, then we advise you to postpone the Ransomware removal for after you’ve performed the payment. Otherwise, even if you pay, you may never be able to restore your data. Obviously, after the money is paid and your files (hopefully) recovered, the Ransomware should still be deleted.
- Even if it seems like Mlwq has automatically removed itself from your computer after encrypting your data, it’s still best to perform the steps from the guide in order to ensure that your PC is clean.
Mlwq Ransomware Removal
To remove Mlwq from your system and ensure that no more files get encrypted, there are four important steps that need to be performed:
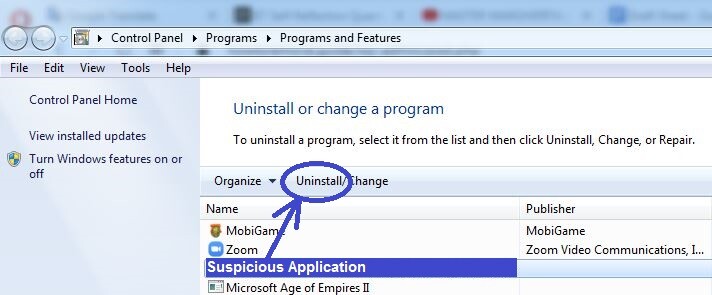
- First, you need to find out if there’s a rogue program on your computer that has initiated the infection and delete that program.
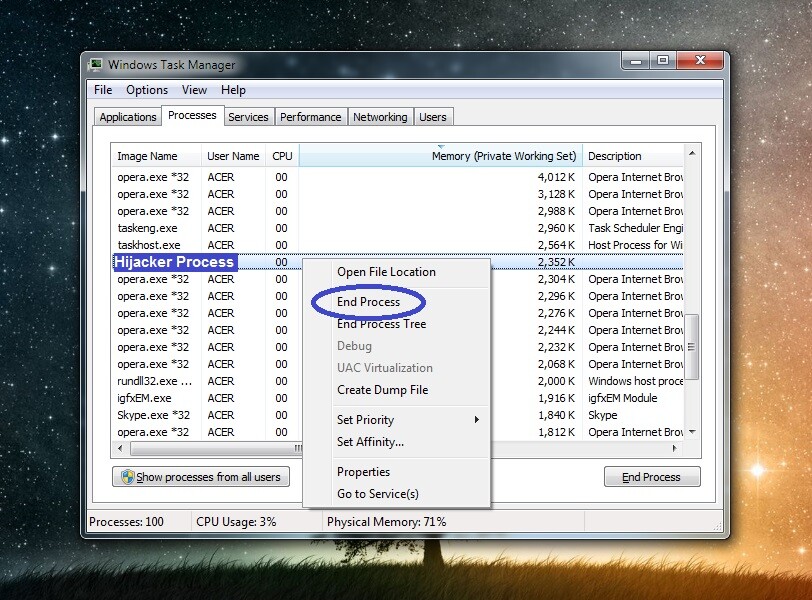
- Second, if there are any malware processes that are still active, you must find them in the Task Manager and stop them.
- Next, you must delete any malware data that may be in these folders: AppData, LocalAppData, ProgramData, WinDir, and Temp.
- The last step to remove Mlwq is to clean the system settings – this includes the Registry, the Hosts file, and the Startup items list.
To successfully complete each of the steps, we recommend checking out the detailed instructions we’ve provided within the next lines.
Detailed removal instructions
Step 1
The easiest way to see if there may be a rogue program on your computer that may have caused the Mlwq infection is to search for the Control Panel in the Start Menu, open it, and click Uninstall a Program. There you will see every program that’s currently installed in your system – if any of the entries shown in that list appear suspicious or are unknown to you, especially if they have been installed recently, you should probably uninstall them. Click such programs, then click Uninstall, and perform the on-screen steps to delete the potentially unwanted program. Bear in mind that if the uninstaller asks you if you’d like to keep anything from that program on your PC, you should deny that offer.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Mlwq is a variant of Stop/DJVU. Source of claim SH can remove it.
Now you must ensure that no rogue processes are running on your computer. To do this, open the Task Manager using the Ctrl + Shift + Esc combination from your keyboard, and look in the Processes section. If any malware processes are running at the moment, they’d probably have high CPU and memory use, as well as strange names that are unfamiliar to you. Before you quit any process, however, you need to make sure that it is indeed related to the virus. To do this, we recommend using the following two methods:
You should Google the name of each process you think is a potential threat – if it truly is malicious, there should be relevant posts that warn about it on reputable cyber-security sites and forums.
Right-click the process’ entry in the Task Manager, click the Open File Location option, and use the following free malware scanner on the files that are in the newly-opened folder. If it turns out that one or more of the scanned files are malicious, this would indicate that the process, too, is a threat and must be ended.


If it turns out that there are harmful processes in your Task Manager, you must first end them (right-click the process, and then click the End Process option) and then delete the entire folders where their files are saved.
Step 3
Since the virus may attempt to re-launch its harmful processes, you need to enter Safe Mode on your computer to prevent that from happening.
Step 4
*Mlwq is a variant of Stop/DJVU. Source of claim SH can remove it.
Click the Start Menu, then type in the search bar below it “Folder Options” and open the icon that gets found first. Then select the View tab, find in it a setting named Show Hidden files, folders, and drives, select it (check it), and click the OK button.
Next, copy this “%AppData%” (without the quotes), paste it in the Start Menu search bar, and hit Enter to access the AppData folder. In that folder, sort the files and sub-folders by order of their creation date, and then delete everything created since the virus’ arrival. You must now perform the same thing with four more folders:
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
When you get to the Temp folder, simply delete all files that are stored in it rather than only the most recent ones. Since it’s likely that there would be thousands of files there, to easily select them all, press Ctrl + A when you enter the folder and then press Del to delete the selected files.
Step 5
Now you must go to the System Configuration settings and clean the Startup items. TO do this, type msonfig in the Start Menu, hit Enter, and then click the Startup tab. Once you do this, look through the list of items that are automatically started when your computer boots up – if there are any entries among them that you don’t recognize or think are suspicious, uncheck them. Also uncheck entries that have “unknown” in the Manufacturer column and then click the OK button to save the changes.
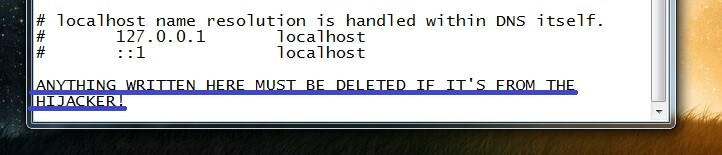
Next, navigate to the following folder: C:\Windows\System32\drivers\etc, double-click the file named Hosts, and if you are asked to select a program with which to open the file, click on Notepad. When the file opens in Notepad, have a look at what’s written at the end of the file – if there are IP addresses listed below “Localhost“, this means the file has been changed by a third-party program. Send us those IPs down in the comment, and we will soon tell you if that third-party program is the virus and if the IPs must be removed.
Step 6
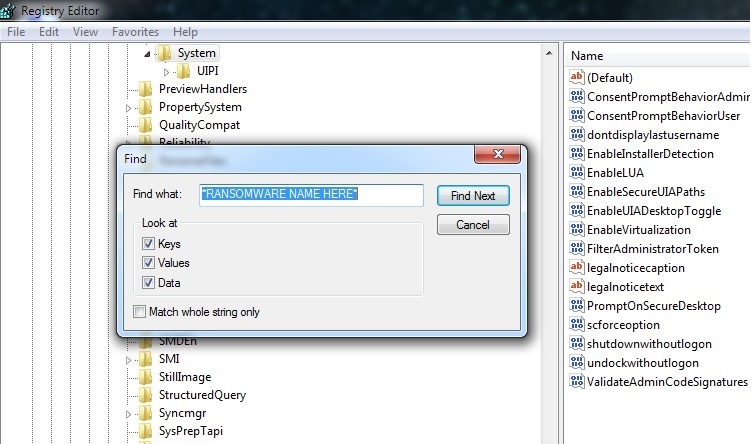
You must now search for the regedit.exe app using the Start Menu search field and open it. You will be asked to give your Admin approval in order to start the app, so do this by clicking on Yes. Then, when you see the Registry Editor window on your screen, open the menu labelled Edit, then open Find, and type Mlwq in the Find search field. Then select Find Next to start the search and delete anything that may get found. Always search again after you delete an item to ensure there aren’t more rogue items left in the Registry.
After making sure that there are no Mlwq left in the Registry Editor, take a look at the following Registry folders – you can find them in the left panel of the Editor, by expanding the folders shown there.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
In those three folders, look for strangely-named items – ones that seem to have names that have been randomly generated. For instance, a possible example of such an item name would be “2u0909u3e092ut302ekd0293it03ue290d2u3r“. If you come across anything like this, make sure to tell us about it in the comments, and we will soon get back to you, telling you if anything needs to be done about the item(s).
If Mlwq is still in the system
A common tactic use by Ransomware hackers is to employ a secondary piece of malware (typically a Trojan or a Rootkit) that helps with the distribution of the Ransomware and also makes it significantly more difficult for the victim to remove the latter. This is a possible reason why you may have not been able to manually delete Mlwq. Our suggestion if that is your current situation is to make use of the powerful malware-removal tool that you can find on this page, as it can take care of all potential malware in your system in one fell swoop.
How to Decrypt Mlwq files
To decrypt Mlwq files, it’s better to not go for the ransom payment and instead focus on finding and using alternative data-recovery methods. Before you try to use such methods to decrypt Ransomware files, however, you must be sure that the PC is perfectly clean.
If you’ve noticed any sketchy files that are still on your system, but you aren’t sure if they are malware, remember that our free malware scanner can help you determine if they need to be deleted. After you’ve made sure that no malicious data is left on your computer, we advise you to visit the How to Decrypt Ransomware article that we have on our site, where we’ve explained in detail the different alternative options that you can choose from in order to attempt to recover the data that Mlwq has encrypted.
New Djvu Ransomware
The latest ransomware variant to emerge from the Djvu family is called STOP Djvu, and it’s hitting users in various countries worldwide. Files encrypted by this variant will typically have the .Mlwq extension.
Users infected with this new variant may have a hard time dealing with the infection. However, if an offline key was used to encrypt the data, it is possible to recover the original files. This is a welcome relief, since keeping up with new ransomware threats is a very challenging task. The good news is that, there is decryption software out there that you may use to try a data recovery. Just click the link below in your browser and hit the download button to save the executable file on your computer:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
Launch the decryptor with administrative privileges and click on “Yes” when prompted. Please take the time to read the license agreement and the brief instructions for use before moving further. Use the button labeled “Decrypt” to try decrypting the encrypted information. Bear in mind that the tool may not be able to decode files that have been encrypted online or with an unknown offline key.

Leave a Comment