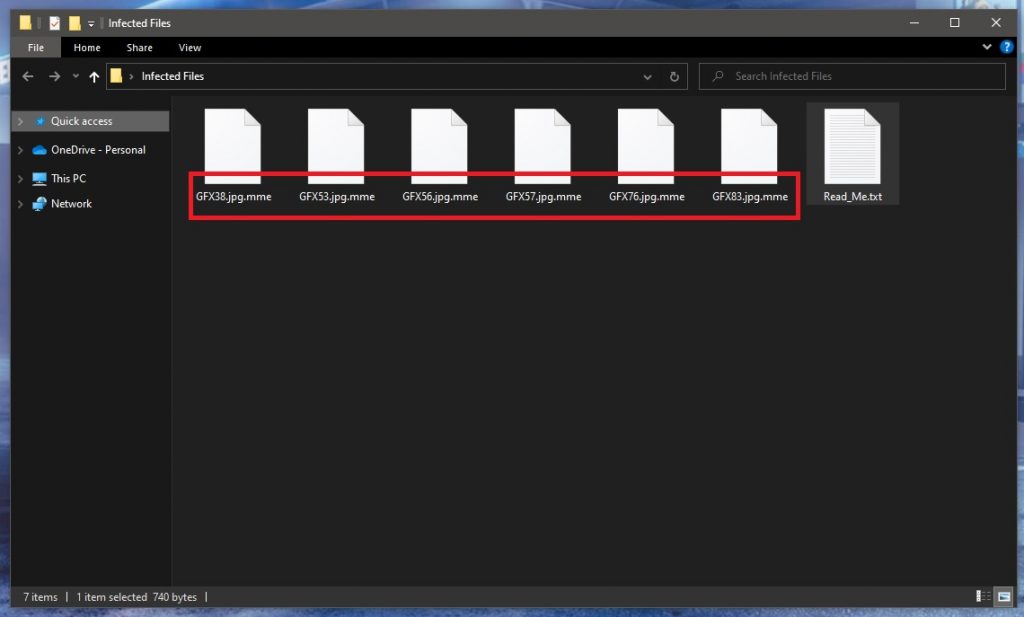
.Mme
.Mme is among the newest ransomware date-encrypting viruses. .Mme is almost undetectable, which makes stopping it a real challenge.
If you have come to this site because your files have been locked with the encryption of .Mme, our removal guide below is designed to help you locate, and remove this terrible virus. We have also included some steps to help you possibly get some of the encrypted files back. While we can’t promise that the process of restoring your data will be 100% effective, it’s still something we suggest you try before jumping to more drastic actions.
The .Mme virus
The .Mme virus is an online threat aimed at encrypting your files. The .Mme virus doesn’t show symptoms during the encryption of its victim’s data.
This type of malware is the second most common form of malware, and the exponential growth it has undergone in recent years puts it at the top of the cyber threats’ list. Today, almost anyone is at risk of becoming compromised by ransomware like .Mme, Zaqi, Yoqs if they do not follow basic security rules.
Once the infection takes place, the ransomware gets down to its dirty work right away. The probability that you will find the ransomware while it is in the process of encrypting your files is slim to none. Therefore, it is best to take all the prevention measures in order to avoid a close encounter with such an infection.
The .Mme file encryption
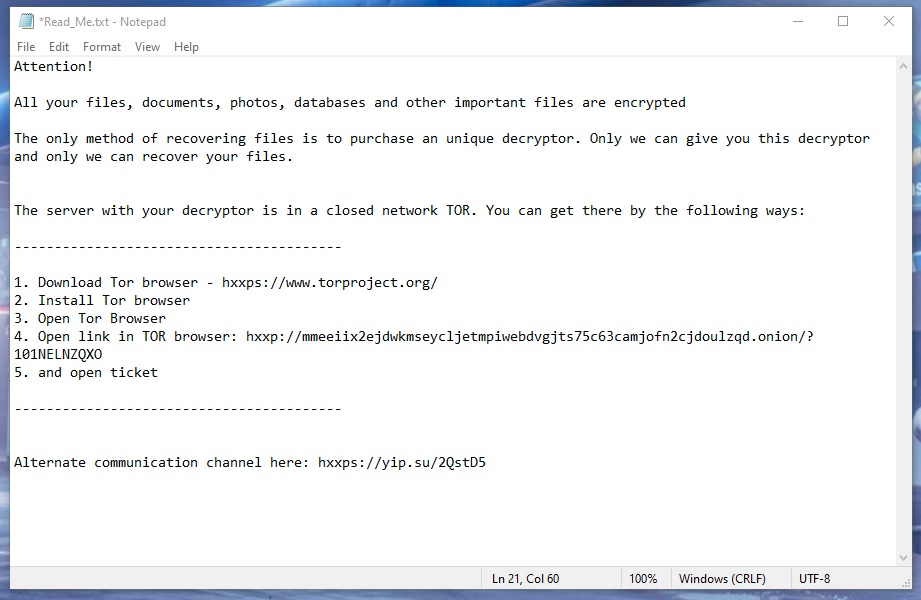
The .Mme file encryption is the result of the ransomware’s attack. The .Mme file encryption cannot be reversed unless the corresponding access key is applied.
In order to obtain that key, however, you will be requested to pay an amount of money to the hackers behind the ransomware. Unfortunately, there can be no guarantee whatsoever about whether or not the criminals would keep their promise. In fact, there have been registered cases where the victims have transferred the required amount, and have never heard from the crooks again. Of course, there have been cases where the victims have been able to obtain the key, but its effectiveness of reversing the applied encryption has not always been on point.
So, in case you are considering the ransom payment as a possible way to save your files, we suggest you first think about the risks. Moreover, it might be worth it to explore some other file-recovery options, as well as some methods to remove .Mme from your system before deciding on giving your money to the hackers. For this reason, we will point you to the removal guide below, and its instructions.
The manual instructions may work for some of you, but it’s not enough to just remove the infection once. You also need to have a robust antivirus program installed on your device, and run full system scans with it to ensure your system stays safe from now on. A good anti-malware software won’t cost you as much as a Ransomware ransom, so keep that in mind when choosing how to keep your computer protected in the future.
SUMMARY:
| Name | .Mme |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
Remove .Mme Ransomware

Several system reboots will be required during the removal of .Mme. Therefore, in order not to lose this page with removal instructions, we recommend you to bookmark it in your browser.
Next, follow the instructions from the link and reboot your computer in Safe Mode in order to block some of the ransomware-related processes from running in the background of your system.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
After you successfully reboot in Safe Mode, press the CTRL, SHIFT and ESC buttons together to start the Task Manager. In it, go to the Processes Tab and search for processes that could be dangerous and could be linked to .Mme and its malicious activity.
If a specific process looks questionable to you, right-click it and open its File Location folder.

You should see a number of files related to that process in that File Location folder. Carefully scan them all with a trusted malware scanner, or simply drag and drop them in the powerful free online virus scanner available below:

Immediately end the processes if its files turn out to be infected, and then delete them as well.
If you need more details about a particular process, it is a good idea to search some information about it online in order to decide if it represents a danger or not.

Sometimes, Ransomware-related entries may be added without the victim’s knowledge in the list of Startup processes. Therefore, to check for such entries, type msconfig in the Start menu search bar and press enter to open System Configuration:

Click on the Startup tab and disable any Startup Items that you believe could be linked to the infection. Typically, items that look suspicious may have unusual names or unknown Manufacturer. If needed, research them online to find out more about them and then simply uncheck their checkmark if you find them to be dangerous. When you are done, click OK and close the window.
Next, back to your Desktop, press the Windows and R keys from the keyboard together. You will see a Run dialog box opening on your screen. In it, copy and paste the following and then press Enter:
notepad %windir%/system32/Drivers/etc/hosts
A Notepad file named Hosts will open. Once you see it, look at the image below and check if in your Hosts file you can find any strange-looking IP addresses like those on the image under your Localhost section:

If something unusual grabs your attention and you believe it could be dangerous, please drop us a comment in the comments section below with a copy of what is disturbing you.

Malicious changes in the Registry of your system may often be a result from a ransomware infection. Therefore, your next task is to open the Registry Editor. The quickest way is to simply type Regedit in the Start menu search bar and press Enter.
Next, once it opens, press CTRL and F and carefully write the name of the ransomware in the Find box that opens on the screen. Then, start a search by clicking on the Find Next button and if anything is found with that name in the Registry, delete it.
Be careful! There is a real risk of a system damage if you delete entries not related to the ransomware. To avoid involuntary system corruption, consider scanning your infected computer with a trusted malware removal tool like the one that you can find on this page.
Close the Registry Editor when no more malicious entries are found and do the following:
Go to the Start Menu search bar and type each of the lines below in the following sequence:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Carefully check each of the locations for entries that have been added recently, as they might be linked to .Mme.
Finally, when you open the Temp folder, select all of its files and delete them to remove any potentially malicious temporary files that the ransomware might have left there.

How to Decrypt .Mme files
The decryption of the files encoded by .Mme is a challenging process that requires a different set of instructions. Therefore, once you are sure that you have successfully removed the ransomware, we recommend you to check our file-recovery guide that will give you some concrete suggestions on how to recover your data without paying a ransom to the hackers. If you are interested, please click on this link to check it out.

Leave a Comment