This page aims to help you remove .Mogera Virus Ransomware for free. Our instructions also cover how any .Mogera file can be recovered.
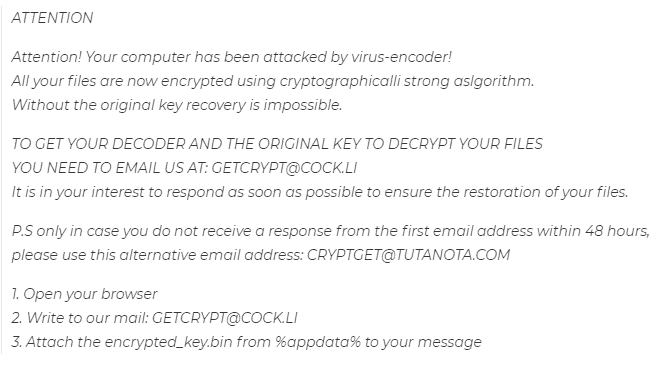
After the ransomware encrypt your files, it leaves a _readme.txt file as a message for the user with instructions to follow:
In the following article, we shall have a look at one particularly malicious piece of malware named .Mogera, providing you with all the necessary information about it. For anybody who is wondering, the harmful piece of malware that we will be focusing on is a version of the highly-dangerous Ransomware cryptovirus type.
A typical thing with regards to Ransomware is the fact most malware programs of this kind , like .Skymap, .Ferosas and .Rectot ,can prevent the user from accessing their own personal computer files by means of encryption. Once the encryption process is completed, the virus would normally create a scary ransom-demanding message in which a money payment would be requested. Additionally, inside of this ransom-demanding pop-up, certain directions could be provided, giving details regarding the way the requested money must be transacted. Additional warnings which can probably be added to the ransom note may tell the targeted individual that the refusal to pay the demanded ransom money may lead to a complete loss of the targeted data files.
To all the victims of the malicious .Mogera who’re presently reading this – we’ve worked hard so as to create the current article and the removal manual that has been added to it with the sole intention of providing you with much needed help against this virus. You are advised to read the paragraphs down below and closely follow the instructions from the guide.
Some things you ought to know about the requested payment of the ransom
Normally, the main tools which allow the cyber-terrorists to succeed in blackmailing their victim is disinformation and anxiety that they try to spread. That’s the place where our article is needed – it’s going to let you know more about the most important Ransomware specifics that you should be aware of.
We ought to also note that the preferred payment technique by most Ransomware creators are the infamous bitcoins. This payment technique (bitcoins) is preferred by the online criminals as such cryptocurrencies are next to impossible to trace. To our mutual frustration, very few of the online criminals who use Ransomware do ever get held responsible for their illegal schemes. What’s worse is the fact that there are many instances where Ransomware victims have made the requested money transfer without getting the access to their computer data back. For that reason, we constantly suggest that any users attacked by Ransomware should really look into other methods rather than pay the requested ransom. That is why we have written a guide manual that includes instructions on how it may be possible to get rid of .Mogera and potentially decrypt your documents without having to pay the requested money. Even though we simply can’t guarantee that the file recovery solutions would work for all Ransomware victims who have had their data files sealed, we continue to think that employing the manual guide is a lot safer and wiser plan of action. At the very least, you wouldn’t be putting your money on the line be sending it to the people who are responsible for your current predicament.
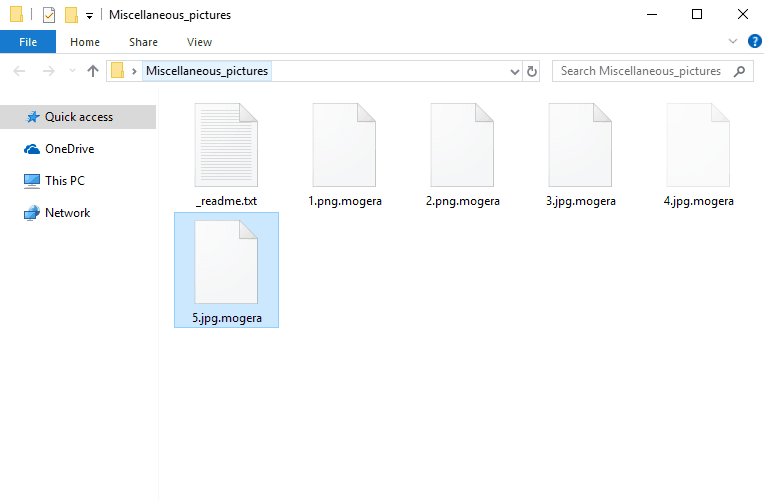
Once .Mogera ransomware has infected your computer, the virus may immediately drop the malicious files in the following directories:
%AppData%
%Local%
%LocalLow%
%Roaming%
%Temp%
SUMMARY:
Remove .Mogera Virus File Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply