.Mosk
.Mosk is a Ransomware virus that encrypts all types of files on your computer. When done with this, .Mosk blackmails you, demanding money for a decryption key.
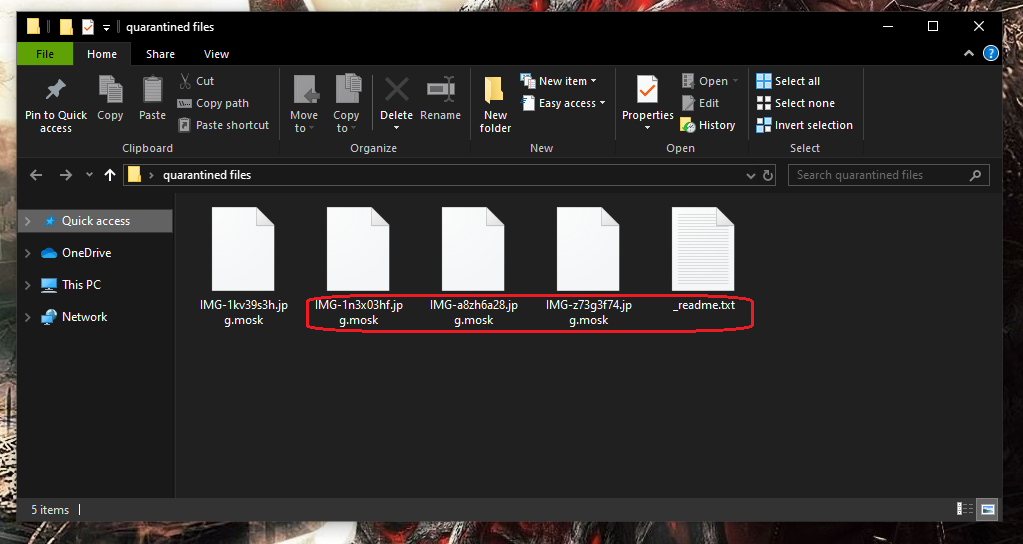
Once the .Mosk Virus has infected your system it will start encrypting your files.
Being attacked by a ransomware virus can turn into a very unpleasant and even traumatic experience. .Mosk is one of the latest viruses of this type, and like so many before it, this ransomware stealthily infiltrates the system of its victim and encrypts the files in it using a very sophisticated algorithm. This makes the files unreadable and inaccessible without a decryption key, or in other words – useless. The cybercriminals behind the infection want to make you believe that the only way to access your files again is to send them money as a ransom for the decryption key they hold. Fortunately, we have alternatives to the ransom payment that won’t cost you a penny and you will find them just below this article.
The .Mosk virus
The .Mosk virus is an infection based on Ransomware that can block access to digital information through encryption. The .Mosk virus can encrypt the files stored inside a computer without warning and demand a ransom payment to decrypt them.
The Mosk Virus is a piece of computer malware that makes the files of the users it attacks inaccessible. After the Mosk Virus locks the targeted data, it makes a ransom payment demand that the victim is supposed to fulfill to restore their files.
Threats like this one are known under the collective name of Ransomware because their goal is always the same – to extort money from the attacked users with the lockdown on their files serving as the needed blackmailing leverage.
The Mosk Virus is a Ransomware version that uses an advanced encryption process to make it impossible for its victims to open their personal files. The Mosk Virus is programmed to display a ransom message on the infected computer’s screen after the encryption.
The ransom message that gets generated after all targeted data has been sealed typically gives the victims strict payment instructions that they are supposed to follow in order to get their files recovered. The problem is that transferring such a payment guarantees nothing – your files may or may not get released by the hackers. This is the main reason we always advise against going for this course of action if you haven’t tried any of the other potential options.
The Mosk virus is a form of malware solely created to extort money from the people it attacks. The hackers behind Mosk Virus, however, don’t really care about whether you eventually manage to recover any of the files that have been locked.
The ransomware infections turn out to be a lucrative scheme for a lot of cyber criminals. Besides, these pieces of malware can prove to be extremely harmful, encrypting valuable information and keeping it locked for indefinite periods of time. So, it’s no wonder that many victims are paying the extortionists sky-high amounts of money in ransom in hopes to get back access to their valuable data.
Sadly, viruses such as .Mosk, .Toec or .Meka are able to bypass most antivirus programs on the market. That is the reason why you probably didn’t even know that a suspicious process was going on inside your system while Mosk was secretly creating encrypted copies of your files. After the encryption process completed, though, you probably received a ransom note on your screen, telling you about the effects of the attack.
The .Mosk file
The .Mosk file encryption is an advanced code that can keep files inaccessible for an indefinite period of time. Decrypting the .Mosk file encryption is only possible with a decryption key which is in the hacker’s hands.
The Mosk file is any piece of data encrypted by this Ransomware virus and cannot be unlocked without a private key. The Mosk file decryption key is offered to the user against a ransom transaction that must be carried out within a short time period.
This is a typical example of a Ransomware infection – a malware form that is specifically designed to extort money from the users of the computers it attacks. In the current case, the leverage used to blackmail you is the lockdown on your files. Unless you pay the hackers, your files would stay in their inaccessible state for an indefinite period of time.
This fact may lead some users to consider paying the ransom but this is where we must warn our readers that this really isn’t a very wise course of action. What’s important about the Mosk file is that it is very difficult to open it if you don’t have access to the private key. However, paying the ransom to receive the Mosk file decryption key may turn out to be a total money waste. The hackers don’t really care about what happens to you and your files after you complete the payment. This is why there’s a significant chance that they don’t really contact you back with details for your data’s decryption after you give them your money. The Mosk file encryption is a very advanced and complex process that will keep your data locked even after you remove the virus from the system. A Mosk file, however, may sometimes be recovered without paying the ransom if you are lucky.
The instructions in the removal guide below, however, are intended to help you remove the virus from your computer and hopefully restore your files from system backups. Of course, the effectiveness of our instructions may vary greatly from case to case, as each ransomware attack is different, but it will not cost you a thing to give them a try. Other alternatives to the ransom payment are to use a decryptor tool. A list of these can be found on our website, so please check it out.
However, while we advise users to try other ways to get their data back, there are serious reasons for not resorting to the ransom payment. The hackers, for instance, might never send you the promised code for decryption. Furthermore, since the file encryption/decryption is a very delicate process, there is a chance that the decryption key may not work properly even if the hackers send it to you. Moreover, as payments are usually requested in bitcoins, which is a cryptocurrency that is notoriously hard to trace, the police have little chance to bring these extorters to justice. You will only be financing them and ensuring that they are never caught.
SUMMARY:
| Name | .Mosk |
| Type | Ransomware |
| Detection Tool |
Remove .Mosk Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

My files have .mosk extension and cannot be read you have any idea?
Thank you a lot in advance
George
My all files have .Modi extension and cannot be opened plz help me
Where can I get the Plz Decryptor. My files have .mosk extension
Thank you
My all files have .mosk extension and cannot be opened. Plz help me
Copyright (c) 1993-2009 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a ‘#’ symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
127.0.0.1 genuine.microsoft.com
127.0.0.1 mpa.one.microsoft.com
127.0.0.1 sls.microsoft.com
The last three entries must be removed from your Hosts file:
127.0.0.1 genuine.microsoft.com
127.0.0.1 mpa.one.microsoft.com
127.0.0.1 sls.microsoft.com
Those are the ones you must delete.
Hi Sir Plz help me How to remove .masok files virus plz give
hi sir;
how to recover .mosk file
Dear sir,
I read your article but it’s not recovering my files . All my date base files are converted to .mosk files . Can u please help is this recoverable. Pls help me with solution.
Regards
Santhi
Hello there!
I found that all encrypted files contained the same clear line that leads to an algorithm; I do not know how to use it. I believe it’s the key to solving and decrypting our files.
xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx then with no species {xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx}
(X = collection of capital, small letters and numbers) {8-4-4-4-12} as shown below
xxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxxx{xxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx}
hoping to find soloution soon
Email: Adel_o85 @yahoo .com
I found these three IP’s below local..
0.0.0.0 www. mefeedia. com
0.0.0.0 www. mefeedia. com
0.0.0.0 delivery.anchorfree.us/land.php
You should remove these IPs from the Hosts file – they aren’t supposed to be in it.