This page aims to help you remove “Mr. All rights reserved”. Our removal instructions work for every version of Windows.
“Mr. All rights reserved”
Mr. All rights reserved is what is known as an email bitcoin scam. The purpose of the message is to convince the person who received it that his system has been hacked, they will demand payment in Bitcoin to stop the release of compromising personal information.
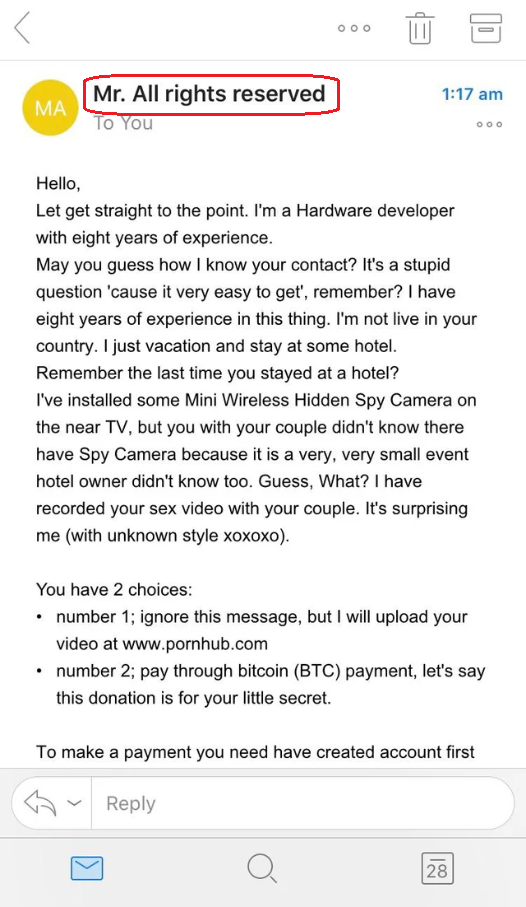
This email is a scam attempt by Mr. All rights reserved.
If you have come across the “Mr. All rights reserved” virus now your system is in serious danger because what you are dealing with is a notorious Trojan-based infection that will not spare your machine. Perhaps you know something about these malicious programs, but if you don’t, their name is actually taken from the famous myth about the Trojan War. Similarly to the wooden Trojan horse from the myth that was presented as a gift, the viruses of this kind seem to be harmless and even intriguing at first. They can reveal their true nature only after doing what they have been scheduled to do. Ultimately, you don’t have to wait for that to happen because the typical behavior of infections like “Mr. All rights reserved” is more than harmful. For this reason, we advise you to use a professional removal tool or a trusted removal guide, like those that you will find below, to remove the Trojan before it has hit you badly.
What can a Trojan do?
The hackers use Trojans to launch different malicious processes and tasks in your system without your knowledge. In some cases, the offenders may just want to corrupt some things in your machine or to crash the whole OS for whatever sick reason. However, it is much more common for the Trojans to be programmed to spy on you, to copy personal or bank credentials and to collect specific data that can be used to steal your identity, drain your bank accounts or hack into your online profiles. Another fairly common use of Trojans, especially new and sophisticated ones such as “Mr. All rights reserved”, could be for the distribution of Ransomware, Spyware and other viruses. Unfortunately, in many cases, such infections are accompanied by a variant of Ransomware or another malware designed to exploit the vulnerabilities of your system. Therefore, an infection with a single Trojan can lead to the infection with a dozen more computer threats without you doing nothing. And this is probably the worst of all malicious uses.
If your computer is protected with a reliable antivirus program, however, you have a great chance to detect and remove the Trojan before it invites its buddies for a system-wrecking party. That’s why our best suggestion is to invest in reputed security software and use it to run regular full system scans. Another key element for keeping your computer safe and sound is to know how to avoid the Trojan threats online. This has a lot to do with the so-called intelligent surfing. So, try not to visit questionable websites, keep away from random pop-ups and spam messages and don’t download cracked software or applications from non-reputed developers. Finally, in case you detect “Mr. All rights reserved” on your computer, one of the options to take care of it is to use the professional removal tool on this page or the instructions in our manual removal guide.
SUMMARY:
| Name | “Mr. All rights reserved” |
| Type | Trojan |
| Detection Tool |
Remove “Mr. All rights reserved” Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment