Msedge.exe may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
Msedge.exe
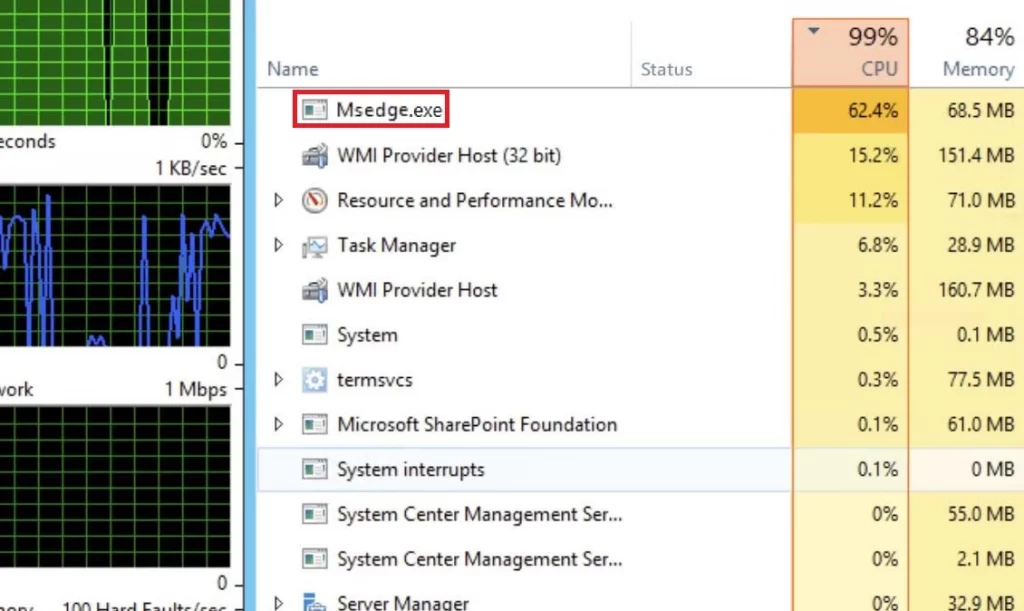
Msedge.exe is a legitimate process associated with the Microsoft Edge browser and is typically not harmful to your system. However, it’s essential to remain vigilant as some dangerous malware programs may attempt to disguise themselves as Msedge.exe (or TiWorker.exe) or use similar names to evade detection. If you notice it in your Task Manager, and there are no unusual symptoms or issues on your computer, there’s likely no need to worry. It’s common for a browser to consume significant CPU and memory resources, especially when you have multiple tabs open simultaneously. However, if you observe the process running when Microsoft Edge is not open or you are using a Windows 7 or Windows 8 PC (which do not have Microsoft Edge), it’s crucial to investigate further.
Msedge.exe what is it?
Msedge.exe is a genuine process that belongs to the Microsoft Edge browser and is generally safe for your computer. Nonetheless, it’s crucial to stay cautious because certain malicious software may try to pose as Msedge.exe or adopt similar names to avoid detection. Being aware of this potential disguise is important to ensure your system’s security.
What is Msmpeng.exe?
Msmpeng.exe is a legitimate and essential component of Windows Defender, Microsoft’s built-in antivirus and anti-malware software. It stands for Microsoft Malware Protection Engine and plays a crucial role in protecting your computer from various threats, such as viruses, spyware, and other malicious software. While Msmpeng.exe is an essential part of Windows Defender’s protection mechanism, it can sometimes consume a significant amount of CPU resources during system scans or updates, leading to temporary performance slowdowns. However, this behavior is normal and expected during intense scanning activities and usually shouldn’t cause major issues. At the same time, malicious programs, like Trojans, Spyware, and Rootkits, may attempt to masquerade as the legitimate Msmpeng.exe process to avoid detection and remain undetected on your computer for extended periods. So you should be aware of this potential threat and use reliable security software to protect your system.
What is Msedge.exe bad image?
Msedge.exe bad image is an error message that may appear when you try to launch the Microsoft Edge browser or any application associated with it. This error message typically indicates that there is a problem with the execution of the Msedge.exe file, and it could be caused by various factors, including corrupted or missing files, incompatible software, or malware infections.
When you encounter the “Msedge.exe bad image” error, it usually includes specific details about the problematic file, such as its location and the nature of the issue. For example, it might mention that the Msedge.exe file is either not designed to run on your system or that there is a corruption in the file.
What is Msedge.exe?
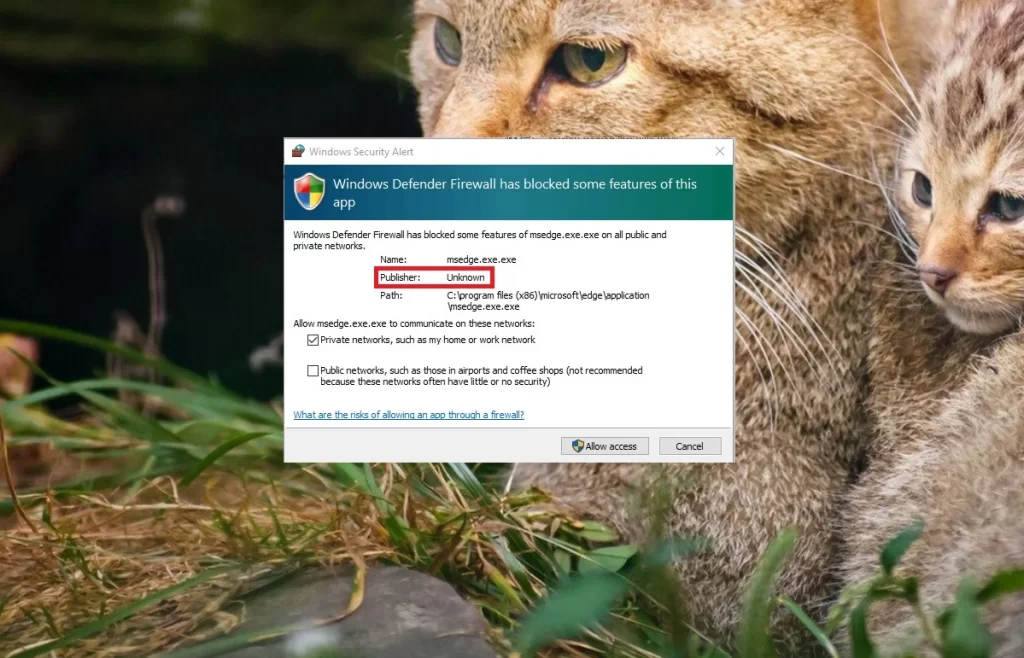
Msedge.exe is the executable file associated with the Microsoft Edge browser, usually found in C:\Program Files (x86)\Microsoft\Edge\Application. However, caution is advised if you come across this file in a different location, as it could be a disguise used by malware. To check for any potential threats, you can perform a search for Msedge.exe in the C: drive and verify the file locations. If you find it outside the expected folder (C:\Program Files (x86)\Microsoft\Edge\Application), it’s essential to check this could be a potential malware in disguise. In such cases, it’s best to take appropriate actions to remove the suspicious files from your system.
Msedge.exe error
The Msedge.exe error typically indicates that there is a problem with the Microsoft Edge browser executable file. Such errors can manifest in various ways, such as crashes, freezes, or error messages. If you come across this Msedge.exe error, there are some common causes and solutions. First, you should check if your Microsoft Edge needs a little repair or resetting and try the repair option. Also, make sure both Microsoft Edge and your Windows system are up to date, as outdated software can be a sneaky culprit. And don’t forget to double-check those browser extensions; sometimes they can cause trouble. Just disable or remove any suspicious ones. Lastly, if your computer is running too many things at once, close some unnecessary tabs and extensions to free up resources.
Msedge.exe application error
The Msedge.exe application error typically pops up when there’s a problem with the Microsoft Edge browser on your computer. It might show messages like “The application was unable to start correctly” or “msedge.exe has stopped working”. If you see this Msedge.exe application error, check if your Windows and Microsoft Edge are up-to-date; sometimes, outdated software can cause issues. If that doesn’t work, you can try repairing or resetting Microsoft Edge through Windows Settings. Also, try disabling or removing any suspicious browser extensions. Run a full system scan to make sure your computer is safe from any malware that might be causing trouble. If the error persists, you can search for more specific solutions online or reach out to Microsoft’s support for further assistance.
The Msedge.exe Virus
The Msedge.exe Virus is a term used to describe any malicious program that disguises itself as the Microsoft Edge browser’s file and process. The malware can be detected when it exhibits suspicious behavior, such as being located in unusual file locations or running as a process even when the actual browser isn’t open. The Msedge.exe Virus is commonly associated with Trojan Horses or Spyware. A red flag that can give the threat away is the size of the Msedge.exe file. The legitimate Microsoft Edge executable typically has a size of 2,964,368 bytes or close to that value so, if you encounter a file named in the same way but with a significantly different size, it is crucial to take immediate action to investigate and remove any malware.
Msedge exe
Threats like Msedge exe are notorious for their versatility, capable of causing various types of harm, including system corruption, data theft, unauthorized access, and facilitating the entry of other viruses into the targeted system. If not detected on time, they can focus on extracting sensitive information from the infected machine and sending it to their creators, who can use the acquired data for fraudulent activities like draining bank accounts or engaging in blackmail. If you are infected, conduct thorough scans with reputable antivirus or anti-malware software to detect and eliminate the malicious Msedge exe file effectively. Additionally, keep your software and operating system up-to-date, exercise caution when downloading files or visiting unfamiliar websites, and avoid clicking on suspicious links or email attachments.
What is Msedge?
If you are an Edge user, beware of Msedge as this could be a sneaky file that likes to pretend it’s associated with the Microsoft Edge browser, but in reality, could be a potential rogue software. If you come across it on your computer or spot a suspicious process with the same name in your Task Manager, it’s best to do a research. Though we’re not entirely sure about its specific intentions, having Msedge hanging around in your system could leave your computer vulnerable to security risks and open the door for Trojans and other nasty malware. So, we recommend you to find and delete it by checking your Task Scheduler, Startup Items list, Services, and Registry and remove any other questionable entries.
SUMMARY:
Remove Msedge.exe virus
To try and remove Msedge.exe quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Msedge.exe extension (as well as any other unfamiliar ones).
- Remove Msedge.exe by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Msedge.exe and any other suspicious items.
If this does not work as described please follow our more detailed Msedge.exe removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Msedge.exe app and kill its processes
Uninstall the Msedge.exe app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Msedge.exe. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Msedge.exe, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Msedge.exe.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Msedge.exe changes made to different system settings
Undo Msedge.exe changes made to different system settings
It’s possible that Msedge.exe has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window



Leave a Reply