TiWorker.exe
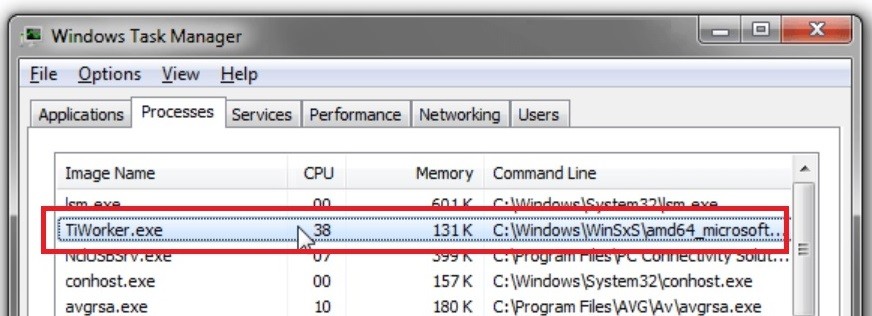
TiWorker.exe is a legitimate Windows process but, sometimes a malware or virus may enter your system and conceal itself under the same name. To be sure that Tiworker.exe is not the malicious culprit in your computer, make sure that it is located in C:\Windows\WinSxS\ .
Surely, you have already heard about this type of malware programs and their insidious and harmful capabilities and we are here to tell you that TiWorker.exe is no exception. This really is a highly dangerous virus program and dealing with it on time is a necessity of you wish to prevent the malware from messing up your PC, your personal data as well as causing a number of other problems that we will go over down below in this current article. Now, if you think you might have TiWorker.exe inside your PC at this moment, we strongly recommend you keep on reading and also take a close look at the suggested removal methods that we have prepared for you and use them in order to eradicate the threat. For anyone of you who might have this Trojan inside their computers, we have posted on this page a removal guide with manual instructions that you can follow in order to locate the malware data in your system and eliminate it so as to make your PC safe once again. Also, within the guide, you can find a suggested professional program for malware detection and removal that can also help you get rid of the threat. What we’d advise you to do is use both options together so that your chances of successfully removing the Trojan would be maximal.
The TiWorker.exe virus
If TiWorker.exe Virus has infiltrated your computer, then you need to make sure to take proper precautions in order to deal with this before it has managed to cause any serious damage to your machine. The TiWorker.exe Virus is a recently detected malicious program that security experts categorize as a Trojan Horse.
Trojans such as Xxwxx.dll, Wup.exe are notorious for their stealth abilities and their tendency to show no symptoms and indications of their presence on the infected machine. This is an aspect that heavily contributes to their effectiveness and success rate that needs to be factored in if you want to stand any chance of managing to deal with such a threat. First of all, know that most Trojan Horse victims do not initially realize that something has happened to their machine. Trojan Horse creators are very creative and ingenious when it comes to finding ways to distribute their malware programs in stealthy ways that would enable the virus to silently sneak inside the targeted machine without anyone noticing it. For instance, a spam e-mail attachment or a pirated software download might be used as carriers of the virus. The same applies to online ads, torrents, sketchy links, different unsafe files you might download form the Internet, etc. Normally, such content can be found on sites with low-reputation but it’s still within the realm of possibility that you might land some nasty Trojan like TiWorker.exe by exploring the pages of or downloading something from a reputed website. This is because some web-criminals might go as far as to hack some famous and popular site and then use it as a “hub” for distributing their virus.
Once the infection has occurred, it is highly likely that there won’t be any visible symptoms yet you still need to be vigilant in case something gives away the virus. Such something could be spikes in your RAM, CPU and GPU use, unusual errors and freezes or system crashes that seem to have occurred for no apparent reason. Other similar irregularities might also get caused by a Trojan infection. However, it’s essential that you also have a good antivirus program as in many cases this might be your last defense against a Trojan virus as well as your best shot at detecting the infection.
Potential damage caused by Trojan infections
There are all kinds of issues and forms of damage that a threat the likes of TiWorker.exe might be capable of causing once it has managed to infect a targeted machine. Most Trojan have destructive capabilities and can be used to corrupt the infected system, format the hard-drives of the PC and delete important data. However, there are other uses for Trojan malware such as espionage, distribution of other viruses (Ransomware, Worms, Spyware, etc.), establishing remote control over the attacked computer and so on. There are many other possible ways in which a malware program of the category of Trojans could be used making it rather difficult to accurately predict the nature of the damage that such a virus might inflict in each separate instance. However, one thing is for sure and that is you need to eradicate TiWorker.exe if it’s on your machine and do it quickly before any of those dreadful consequences have occurred and made things for you much more difficult.
SUMMARY:
| Name | TiWorker.exe |
| Type | Trojan |
| Detection Tool |
Remove TiWorker.exe Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment