This page aims to help you remove the Mtogas Virus for free. Our instructions also cover how any .Mtogas file can be recovered.
In this article, we are going to talk about the cyber attack caused by a new Ransomware called Mtogas. This infection is a nasty file-encrypting virus that exploits system vulnerabilities, and which silently sneaks inside the computer without the victims’ knowledge. The moment Mtogas nests inside the user’s machine, it immediately scans the computer for files which are considered important and valuable for the victim and secretly encrypts them with the help of a complex algorithm. Then, the Ransomware generates a ransom-demanding notification on the screen and asks for a ransom (typically in bitcoins) payment in exchange for receiving a special file-decryption key. The idea of the hackers who stand behind the malware is to blackmail the web users and force them to pay a certain amount of money if they want to obtain the key needed for unlocking their data.
What is the Mtogas virus and how does it work?
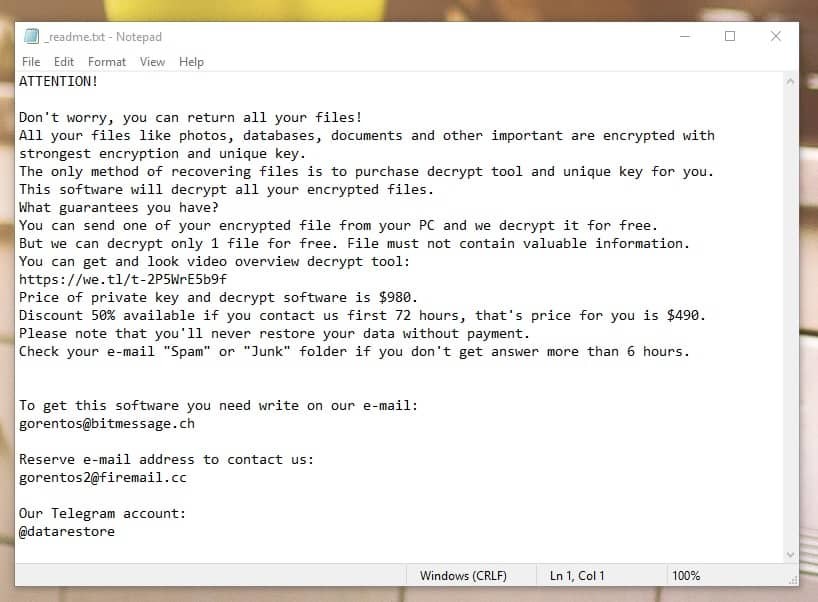
The Mtogas Virus will drop a _readme.txt file with instructions for you to follow
The Mtogas Virus is a sophisticated Ransomware infection that gets in the computer without the knowledge of the user. Like most cryptoviruses (Krusop, Masok), this one is created for blackmailing purposes and when the attacker puts it into operation, what the malware does is, it starts to encrypt all the information stored in the infected system. In order to access this data, you must enter a special decryption key code that is not found locally on the affected computer, but is kept in secret on the attacker’s computer.
As per the information available, this Ransomware is infecting computers through various transmitters including spam emails containing infected attachments, false security warnings, torrents, fake ads, misleading links and messages, fake undelivered email notices or job offers and other attractive and harmless-looking types of web content. Typically, the harmful payload is sent to the user and when they interacts with it, this causes the infection process to begin. Unfortunately, there usually are no visible symptoms which can give the malware away, which is why most of the victims come to know about the contamination only after the scary ransom-demanding notification gets displayed on their screen.
The attackers behind the Ransomware typically ask for a certain amount in bitcoins and threaten that if they are not paid in a certain period of time, the encrypted files will remain inaccessible forever.
If I pay, will the .Mtogas file encryption be removed?
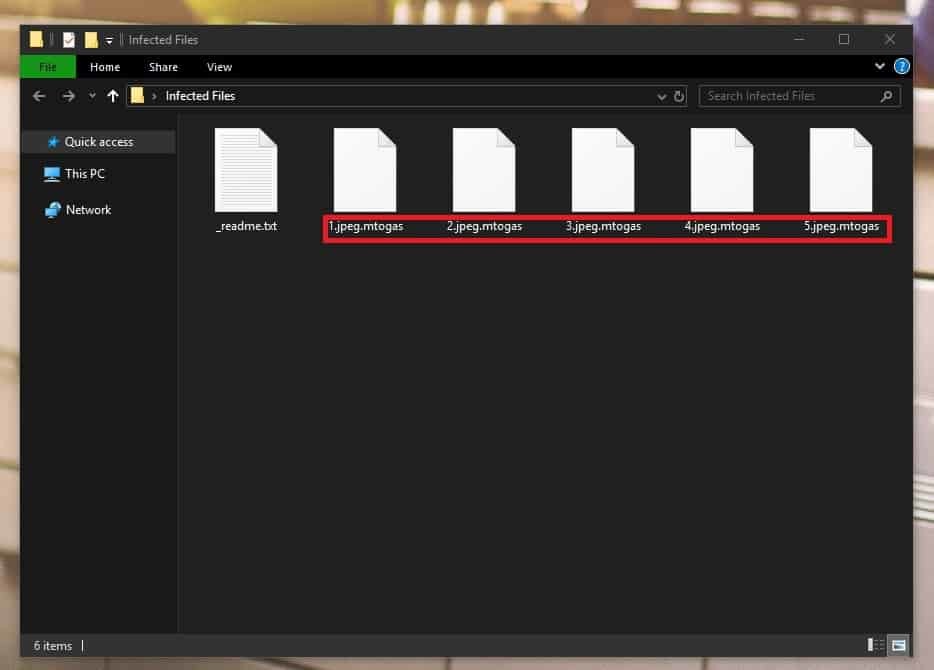
Encrypted .mtogas files
Now, the problem does not end here because, even if the victims pay and carefully follow all the ransom demands, there is no guarantee that they will receive the decryption key from the hackers. And if, by any chance, they do, nobody can say how effectively that key will reverse the applied encryption. What is more, usually, unless the Ransomware is removed, the infected computer cannot be used safely and any new files that the victims create may fall into the grasp of its encryption.
Therefore, security experts, including our “How to remove” team, typically advise the people attacked by Ransomware to not give their money to the hackers. Instead, they suggest that the victims explore some the alternatives, which may help them remove the infection from the system and restore some of their files by other means. The removal guide below, for instance, contains detailed Mtogas removal steps and some file-recovery suggestions that do not involve paying the ransom to the hackers.
SUMMARY:
| Name | Mtogas |
| Type | Ransomware |
| Detection Tool |
Remove Mtogas Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

hello, im having tha same issue on my home pc i also get that readme file plss help what should i do