Nbes
Nbes is a malicious computer program that results in mass file-encryption once it infects a given computer. Nbes is aimed at locking-up the important user data found in the targeted machine so that it could later blackmail the victim for a ransom payment.
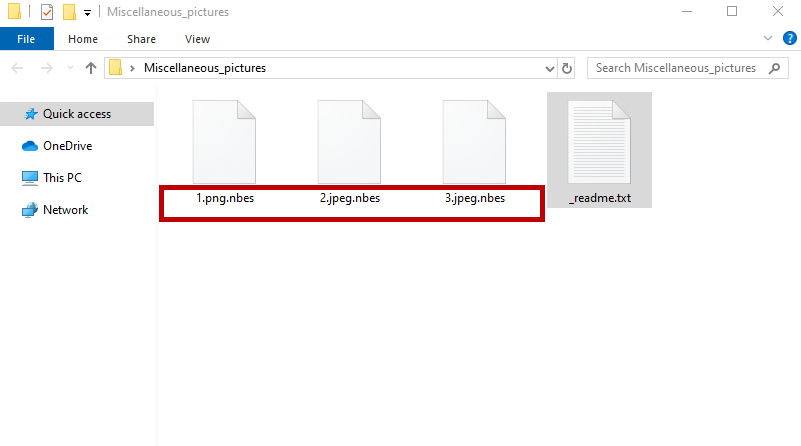
The Nbes Virus will encrypt your files and leave a _readme.txt file behind.
Nbes is a threat that can be categorized as a type of Ransomware – a malware program used for money extortion. Nbes seals the user’s data through its high-level encryption and doesn’t provide the private key until a ransom is paid. Currently, this type of malware is one of the biggest software security issues on a worldwide scale and being well informed concerning the specifics of these viruses is very important. You must know what the Ransomware viruses are capable of and what you can do to protect your data from them. Also, you must have an idea of what you could potentially do to minimize the damage done by the Ransomware in case you’ve gotten attacked by such a threat.
Nbes is a specific form of Ransomware that utilizes the data-encryption method in order to seal your most valuable data. The encryption employed by Nbes is nearly unbreakable and there may be no way to unlock it other than using the corresponding decryption key. This is what leads many users to simply pay the requested ransom sum and hope that the criminals behind this Ransomware would keep their promises. However, this is typically not a very wise decision. Nbes is a virus program that is solely created to extort money from you through keeping your data hostage. The hackers that use Nbes don’t care about the future of your data – they only care about obtaining your money. Because of this, it is perfectly possible that they refuse to supply you with the recovery key for your files and simply take your money and vanish with it.
The Nbes virus
The Nbes virus is a highly-dangerous form of Windows malware known as Ransomware. The Nbes virus is designed as a money-extortion tool, as it aims to take your personal data hostage and only release it once a ransom is paid to the hackers.
If you are a victim of this malware piece, you must know that the files that it has locked-up may or may not get released. There can be no guarantees here with regard to the future of your data. The Ransomware encryption is very advanced and, in most cases, it cannot be unlocked if you don’t have the unique decryption key that corresponds to it. And, as we said above, paying the ransom for that key is also not a guaranteed way to restore your files. The only thing that’s certain if you make the payment is that you will never get your money back from the hackers. But if the decryption key is typically the only thing that can unlock your files and if paying for it is a bad idea, then what can you do to fix things? Well, there may still be certain alternatives that can be tried in order to circumvent the encryption placed by the Ransomware, but we cannot give you any promises that those alternatives will work. You have to try them and see for yourself. All we can do is show them to you and explain exactly what you must do.
The Nbes file encryption
The Nbes file encryption is an elaborate data-locking process that makes the targeted files inaccessible by applying a nearly unbreakable encryption algorithm. The private key for the Nbes file encryption may not be available to you but there may be ways to circumvent the encryption.
One such way is to use a backup of your own on which you’ve previously stored your important data. However, in order to use such a backup, you will first need to remove the virus from the computer. Otherwise, if you connect a backup device to your machine while the Ransomware is still there, the backup copies on the external device may get encrypted by the virus. In fact, removing the Ransomware is always a good idea because it will negate the risk of getting any of the new files you create or download encrypted by the threat.
Two other possible recovery methods can be found in the data-restoration section of our next guide. However, before you try them out, don’t forget to remove the infection by following the steps you will see right below:
SUMMARY:
| Name | Nbes |
| Type | Ransomware |
| Detection Tool |
Remove Nbes Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment