Npsg
Npsg is a virus program of the Ransomware cryptovirus subtype. Npsg uses encryption to restrict access to the files of its victims and make the latter pay a ransom for unlocking the “kidnapped” data.
The Npsg Virus will encrypt your files
Ransomware is a specific form of malware which is currently one of the most troubling computer threats due to its stealthy infection tactics, its ability to silently do its malicious job inside the attacked machine, and also because of the oftentimes irreversible consequences of its attack. Since you are here, you are probably wondering if and how you could deal with the Npsg virus. Before we get into more specific explanations, we must make one thing clear first – full recovery from this virus attack might not be possible at the current moment. Ransomware viruses like this one use military-grade encryption to render the files of their victims inaccessible, and breaking through this encryption is extremely difficult if you don’t have the corresponding key. This same key is actually what you’d be asked to pay a ransom for. The Ransomware virus has probably already showed a message on your screen within which you are told your only hope for restoring your data is through the decryption key, and the way to get that key is by paying a certain amount of money. There are likely instructions in the ransom message, which show you the exact way to make the payment so that it reaches the blackmailers.
The Npsg virus
The Npsg virus is a type of PC malware that makes the data in the infected system inaccessible. The victims of the Npsg virus are told to “purchase” a special key from the hackers to unlock their data.
If you are a victim of Npsg, then you might be wondering whether paying the ransom wouldn’t help you solve this problem, and restore your files. Here is the place to mention that this course of action is rather inadvisable. At best, it should be regarded as a last resort option, and not as your first choice course of action. The reason for this is the payment hides the risk of wasting your money without really getting the locked data recovered. Many hackers simply lie to their victims about sending them the key after the payment is made. Therefore, you might make the transaction without being sent anything in return to help you recover your files. Also, even if you do receive a key, the latter may not always work, and it might not fully restore the files in your system
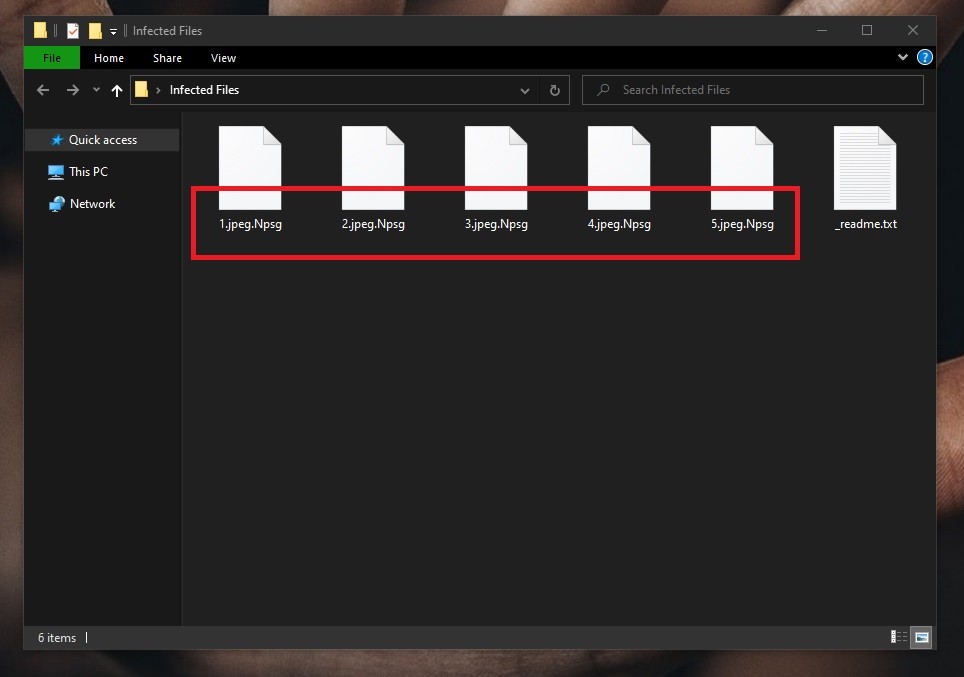
The Npsg file extension
The Npsg file extension is a unique suffix that replaces the normal extension of your files. The Npsg file extension can’t be recognized by conventional programs, making the affected files inaccessible.
Now that we have explained why the payment isn’t a very good option, we should tell you about the possible alternatives. To be frank with you, they aren’t that many, and might not always work perfectly. However, if you try the suggestions from our guide, you should be able to minimize the consequences of the cryptovirus attack without paying the ransom.
The guide you will find on the current page offers instructions that will help you remove the virus, and while this won’t directly release your data, it will help make your system safer, and will open some data-recovery options, such as using external backup devices that won’t work if the Ransomware is still in the computer.
If you don’t have any backups, we advise you to try some of the suggested methods from the second part of the guide. The problem with them is the fact that they aren’t universal, and their effectiveness varies. Still, it’s preferable to try them before you actually consider paying the ransom as you might still be able to recover some of your data without putting your money on the line.
SUMMARY:
| Name | Npsg |
| Type | Ransomware |
| Detection Tool |
Remove Npsg Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

please help me restore my file that was hit by npsg
Hi Rholin, look for a decryptor in our page, if you cannot find one sadly it does not exist yet and your files cannot be recovered at this point.