.Pandemic
.Pandemic is a harmful computer program created by cybercriminals for the purpose of blackmailing users by “kidnapping” their files. .Pandemic belongs to the Ransomware category and it employs an advanced encryption algorithm to make its victims’ data unavailable.
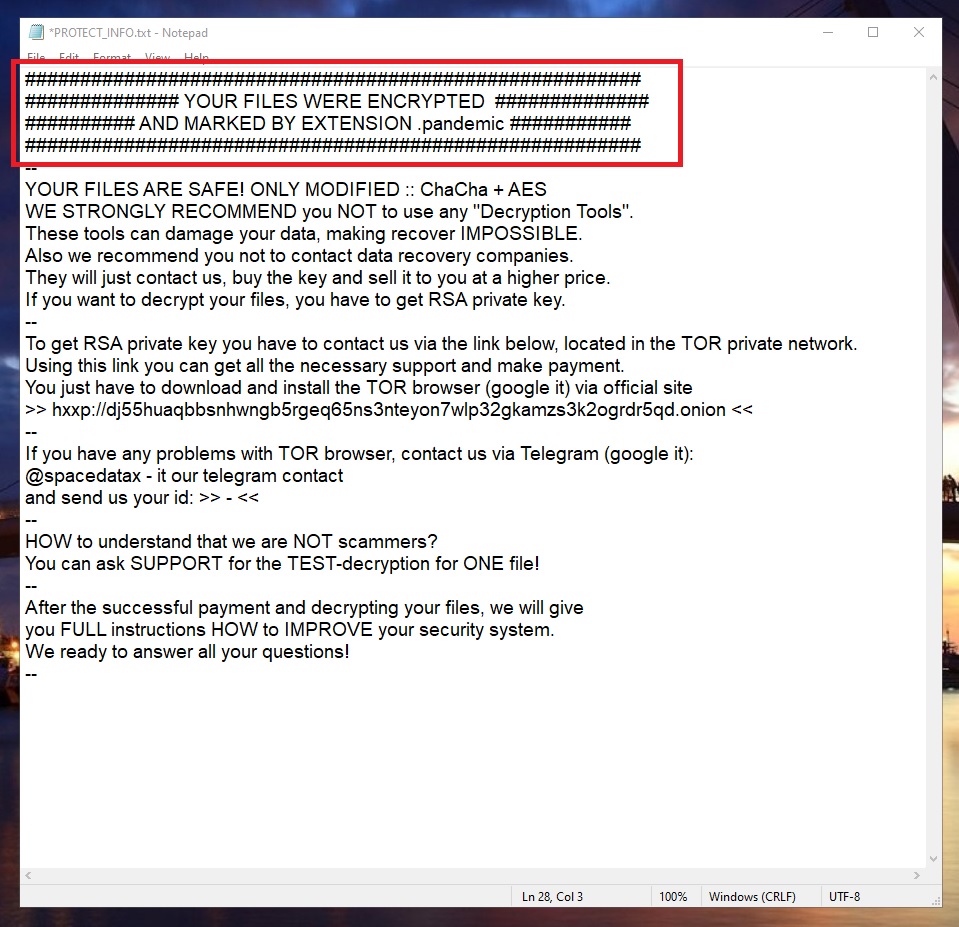
The .Pandemic Virus ransom note
The threats of the Ransomware category have been a very widespread type of malware threat for quite a few years now and they don’t seem to be going away anytime soon. Therefore, it pays to be well informed about the main characteristics of viruses such as .Pandemic, Oonn, Roger.
The first thing we need to tell you about this new virus and the malware category it belongs to is that infections like it tend to have a very high success rate. By that we mean that it is very unlikely to spot the virus before it manages to encrypt your files. More than likely, the majority of this article’s readers are people who have already gotten hit by this Ransomware and have had their files locked by its encryption. The good news is that .Pandemic will probably not harm anything in your system, including the encrypted files (the hackers need for your files to stay intact so that they’d have blackmailing leverage). However, if the locked data is important to you and you don’t have any backups of it, the fact that .Pandemic has encrypted it and is now waiting for you to pay a ransom for its liberation is already bad enough. Still, it is crucial that you keep calm and asses the situation in order to minimize the damage caused by the virus and not make matters worse.
The .Pandemic virus
The .Pandemic virus is an advanced form of malware that uses a sophisticated encryption algorithm to make the data of its victims totally inaccessible. The .Pandemic virus generates a special key unique for every computer it infects that can restore access to the locked files.
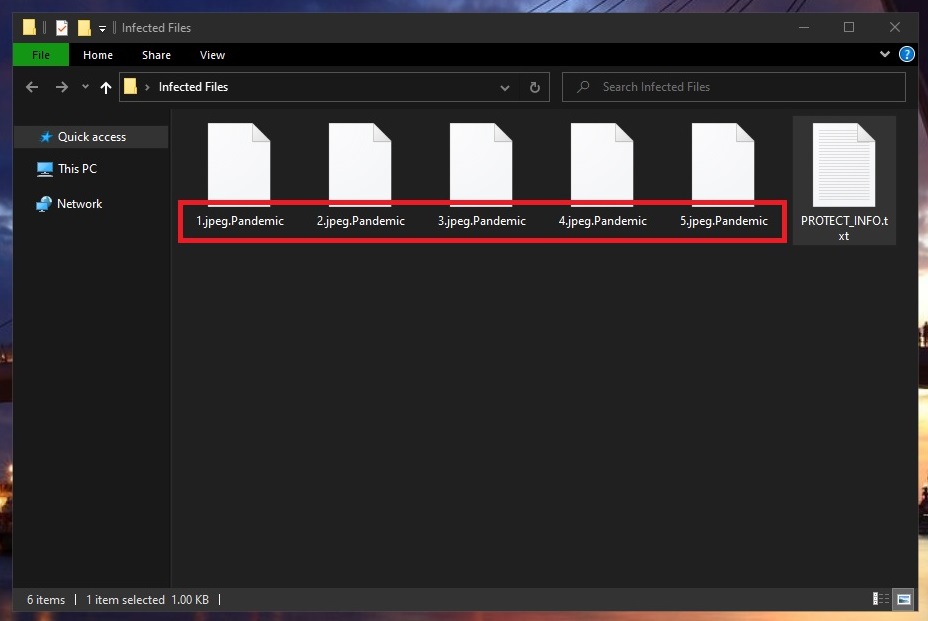
The .Pandemic virus will encrypt your files
This key is the object of the blackmailing that is to follow immediately after the targeted files have been locked up. The ransom message note is shown to the user via a pop-up or a notepad file that the virus creates on the infected machine’s Desktop. If you are thinking about paying the ransom, take the time to try some possible alternatives instead of directly putting your money on the line. You don’t know if the hackers are really going to give you the decryption key so it’s best not to rely on their promises.
The .Pandemic file extension
The .Pandemic file is a filename extension unique for this virus that replaces the normal extensions of the encrypted files. The .Pandemic file extension cannot be removed without decrypting the files and, until then, no program will be able to recognize the encrypted data.
If you are lucky, however, you may be able to bypass the need of acquiring the decryption key from the hackers. We cannot promise you anything, but we strongly recommend you try the instructions in the removal guide below. The guide will help you remove the virus and then, in its second part, you will see some file-recovery suggestions that may allow you to restore some of your most valuable files.
SUMMARY:
| Name | .Pandemic |
| Type | Ransomware |
| Detection Tool |
Remove .Pandemic Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment