Roger
Roger is a Ransomware virus that is programmed to encrypt its victim’s files, thus rendering the affected data inaccessible. Roger doesn’t show symptoms during the encryption but it reveals its presence through a ransom note once the files have been locked.
The Roger Virus will encrypt your files
If all the files present in the hard drives of your computer cannot be accessed because Roger has locked them up, then you need to learn about the options that are in front of you right now so that you can choose the best and most optimal one for your situation. Here, we will try to offer you as much help as possible against this malicious virus and provide you with guidance that should allow you to remove the threat and may even enable you to restore some of the locked files without having to opt for the ransom payment. Therefore, we strongly advise you to read the following lines and then try out our guide so that you can manage to minimize the unpleasant consequences of the attack from this piece of malware.
The Roger virus
The Roger virus is a harmful virus for Windows PC that doesn’t allow its victims to access their private files unless they pay for a private key. The Roger virus informs the targeted users about the demanded payment through a notepad note.
Ransomware threats like this one are aimed at making you release a payment in exchange for which you would supposedly receive a private key that will release your files. A ransom note generated on the infected computer’s desktop is what notifies the user about the demanded payment and about the way they it is supposed to be transferred. Many ransomware victims may actually see this and think to themselves that paying could be a needed compromise that would allow them to restore the locked files. The problem here is that there really isn’t any guarantee that paying would automatically result in receiving the private key for the data’s decryption. For all you know, there may be no such key on the hackers’ computers, or if there is, the hackers may simply refuse to give it to you even after the money has been transferred.
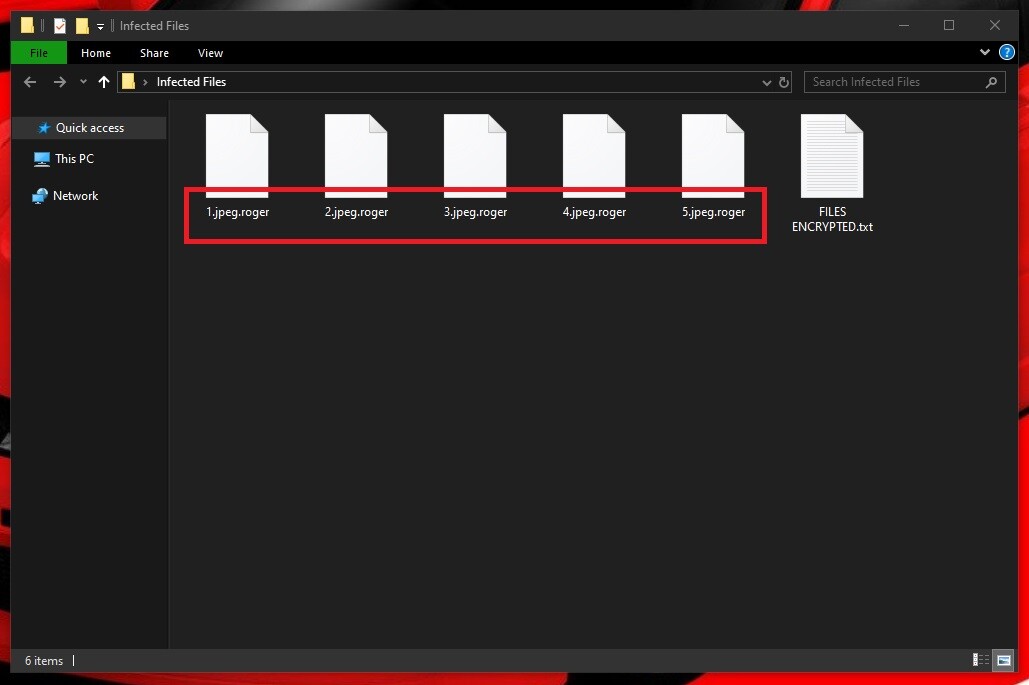
The Roger file extension
The Roger file extension is a string of characters that is added to the name of each encrypted file. The Roger file extension isn’t recognizable by any program and further ensures that the user cannot open their files without the private key.
The guide you will see below offers instructions on how to clean your computer from the Ransomware and we urge you to follow those instructions. While removing Roger won’t immediately set your files free, it will give you the freedom to try some alternative recovery methods that may get you some of your data back. Some of these methods are provided in the next part of the guide that focuses on file recovery, so after you remove the virus you are advised to go there and try out our file-restoration suggestions.
SUMMARY:
| Name | Roger |
| Type | Ransomware |
| Detection Tool |
Remove Roger Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

my system is affected by this please help me in this
Hi Bharat,
What help do you need? Did you go through the removal guide provided in this article? It’s step by step and very easy to follow.
My computer got affected by this virus this morning and I couldn’t open all my important files. Could you help ?
Hi Crystal,
you just have to follow this guide to remove the virus and to decrypt your files.
My computer got affected by this virus this morning and I couldn’t open all my important files. I have tried this guide but this couldn’t help me out. Could you help ?
Hi Zohain, for now, the only other alternative to paying the ransom, is to backup/save your encrypted data as is and wait for a possible solution, until a decrypter becomes available.