*Ppvs is a variant of Stop/DJVU. Source of claim SH can remove it.
Ppvs File
The core of any ransomware lies in its encryption process, and the situation is no different with the Ppvs file encryption. At its essence, encryption is about converting readable data into a garbled format. This ransomware uses a complex algorithm, ensuring the data is transformed in such a way that only a specific decryption key can revert it. Think of it like a fiendishly complex puzzle. Without the exact pieces (or the key), the picture (or your file) remains incomplete. The process through which this ransomware turns each file into a Ppvs file is meticulous, targeting individual files and locking them away from user access, effectively holding them hostage until a ransom is paid.
The recommended method you can try in order to decrypt your Ppvs files is through a free data recovery tool that may help get back some of your data. No guarantees can be give if or how much of the data willl be restored, but this is certainly a better option than the ransom payment, which always carries the risk of paying the money and getting nothing in return.
To remove the Ppvs ransomware, start by deleting any suspicious data and programs from your system and then check system settings such as the Registry and Services, cleaning them from anything questionable as shown in our guide. After the malware is gone, you can move on to the file restoration process, detailed further down the guide.
Ppvs Virus
Ransomware, like the Ppvs virus, or other versions like Ppvw and Ppvt, stands out as particularly pernicious among malware variants. Its potency lies not in damage, but in denial. By encrypting user data, it denies access, often to critical information. While some malware might steal or corrupt your data, ransomware holds it hostage. What makes the Ppvs virus so formidable? Its adaptability. It’s not picky; from individual users to massive corporations, anyone can be a target. Crafty hackers wielding Ppvs implement a cocktail of techniques, ensuring their malevolent software ensnares as many victims as possible. And as long as the malware has managed to lock anything important, the victim will often have no choice but to give in to the ransom demands.
Ppvs
Ppvs is a ransomware threat that can enter your system in a ton of stealthy ways, avoiding any sort of detection. When picturing ransomware distribution, most imagine dubious emails or deceitful phishing links. But Ppvs, and its ilk, have a wider net. Exploit kits, lurking on compromised websites, can invisibly probe your system for vulnerabilities and sneak ransomware in. Then there’s “drive-by downloading,” where merely visiting a tainted site can trigger a silent download. Malvertising, a neologism you wish you didn’t need to know, involves injecting malicious ads into legitimate advertising networks. Clicking on one such ad might grant Ppvs the ingress it seeks.
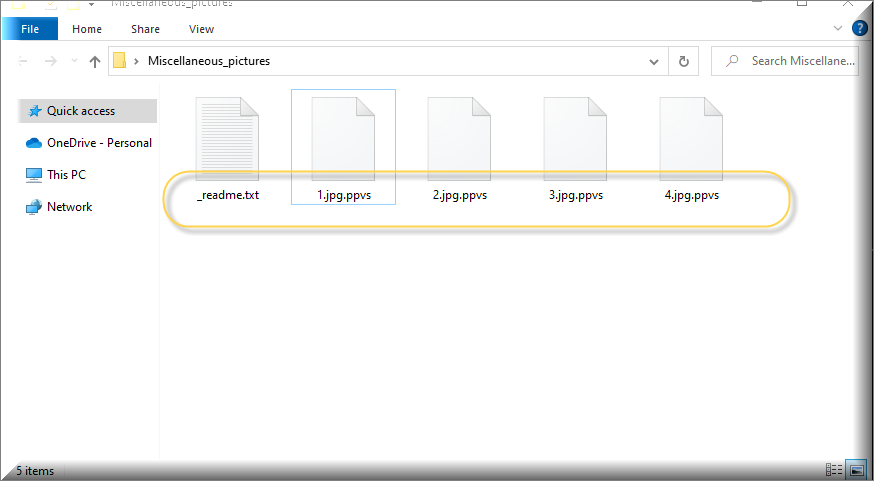
.Ppvs
Spot a .Ppvs suffix on your file? That’s this malware’s calling card, signifying the encryption of your files. However, merely deleting this extension won’t unlock the file. It’s akin to removing a padlock’s outer casing while the bolt remains fastened. There are potential decryption methods, from official tools to third-party software. Some have a dash of success; others might lead to further data corruption. Always remember: every decryption attempt is a gamble. The lack of guaranteed success paired with the potential risk means you’re playing high-stakes poker with your precious data. That said, it’s generally much safer to try free decryption tools available online, as opposed to paying the ransom, because, at least, you won’t be risking your money.
Ppvs Extension
The .Ppvs extension applied by this particular ransomware isn’t file damage; it’s a more type of attack insidious. While the content of the file remains unaltered, the encryption renders it inaccessible, essentially holding it hostage. This encryption process preserves the file’s core data, meaning the information isn’t lost—just locked away. If the affected files are not of prime importance, a pragmatic option might be to simply remove the ransomware and its encrypted files. For a more radical solution, one could consider wiping the entire drive and reinstalling the operating system. This will get rid of the virus entirely but will also delete any files that have the Ppvs extension. If there are files that are important to you, we recommend trying the free data-recovery tool at the end of this post.
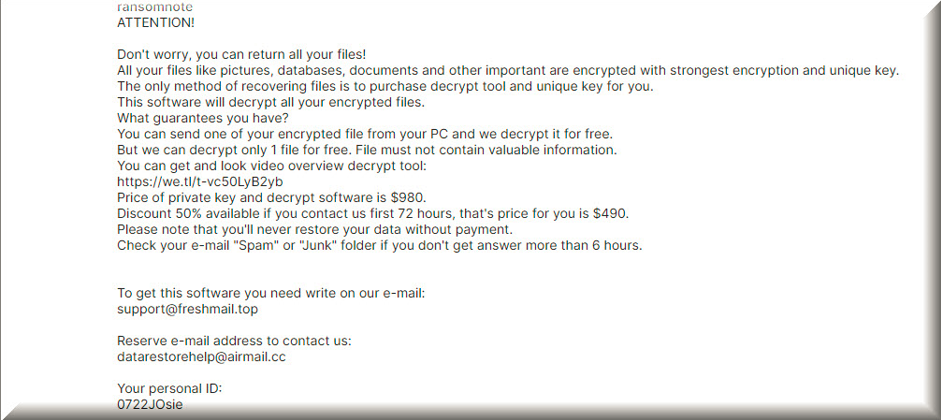
Ppvs Ransomware
An attack from the Ppvs Ransomware can induce anxiety, yet immediate action, especially paying the ransom, may not be wise. The urgency conveyed in the ransom note is manipulative. Trusting cybercriminals is a gamble. Their provided cryptowallet for payments might be inactive, translating your payment into a fruitless endeavor. It’s essential to assess the situation calmly. Deliberate on all available options. Understand that hackers aren’t trustworthy. Payments might go unnoticed, with files remaining encrypted. Instead of impulsively adhering to the ransom note displayed by the Ppvs ransomware, consider researching alternative recovery strategies. Accidental backups, older version of some of the files, or some free data restoration tools are all methods you should try first, before even thinking about the ransom.
What is Ppvs file?
A “Ppvs file” refers to a document encrypted by this particular piece of malware. Despite the daunting encryption, the file’s core data remains intact, but the issue is that it is inaccessible to anyone who doesn’t have the special key that can unlock the file. Before entertaining the idea of ransom payment, explore other avenues. Often, we forget about potential backups – drive storages, past emails, or even external drives may contain unencrypted versions. A “Ppvs file”, while encrypted, isn’t necessarily lost forever. Paying should be the absolute last option. Only consider this if the files hold unparalleled significance. Even then, there’s no guarantee hackers will uphold their decryption promise.
SUMMARY:
| Name | Ppvs |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Detection Tool |
*Ppvs is a variant of Stop/DJVU. Source of claim SH can remove it.
Before you begin this guide
There are several important things you ought to consider before you begin the removal of Ppvs:
- Smartphones, tablets, external HDDs, flash drives, or other devices that have files stored on them, that are connected to your computer at the moment must be unplugged ASAP!
- It’s recommended that you do not pay the ransom, but if you have no other option, then our advice is to proceed with the removal process after you’ve sent the money, and after you have hopefully received a working decryption key.
- Even if it seems like Ppvs has automatically erased itself from your system, you still need to make sure that the computer is malware-free by performing the steps we’ve shown below.
Remove Ppvs Ransomware
To remove Ppvs, you can perform the next manual removal steps, or you can delete the virus with the help of a specialized anti-malware tool:
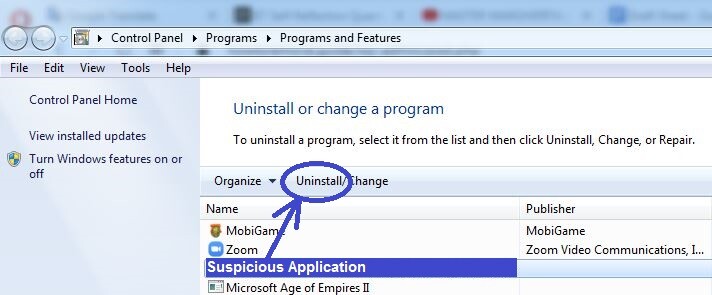
- Find and delete any program in the Programs and Features list that you suspect of being related to the Ransomware attack.
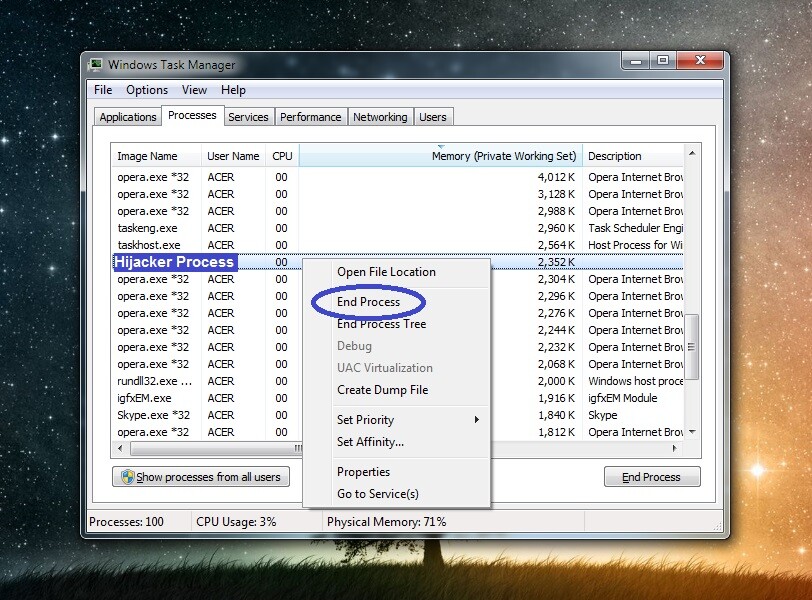
- End any malware processes you may notice in the Task Manager.
- Erase any malicious files that may be found in the WinDir, LocalAppData, ProgramData, AppData, and Temp folders.
- Check and restore the settings of your computer, including the Registry, the Startup items list, the Hosts file, and the Task Scheduler.
The way each of those steps needs to be performed is explained within the next lines. There, you will also find a powerful anti-malware tool that can help you delete the virus automatically and ensure your system doesn’t get infected again.
Detailed removal instructions
Step 1
Click the Start Menu, type appwiz.cpl, press the Enter key, and explore the newly-opened list of programs. Search for anything that has been installed recently and that looks untrusted. If there’s a program in that list that you suspect of being linked to the malware, right-click on it, and click Uninstall. Then perform whatever removal steps appear on your screen. If there’s a detailed uninstaller with different settings, use the settings that would ensure that all data and settings for the questionable program get deleted.
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ppvs is a variant of Stop/DJVU. Source of claim SH can remove it.
Start the Task Manager tool (press Ctrl + Shift + Esc to open it), then click its Processes section, and there look for questionable processes that:
- Use suspiciously-high amounts of memory and CPU
- Have suspicious and unfamiliar names
- Don’t appear to have any relation to any of the regular programs that are on your computer and/or seem to be connected to any programs you may have tried to uninstall in Step 1
Look up the names of any such processes you may come across in the Task Manager, and also check the files in their location folders for malware code. To do the latter, right-click the suspected process, select open File Location, and then, with the help of the following free online malware scanner, test each file in the newly-opened folder for malware.


If you have enough reason to believe one or more of the processes that are currently running on your PC are malicious, be sure to first quit them (right-click the process and select End Process) and then to delete their entire location folders (and not only the files that the scanner may have detected as malware).
Step 3
Even if you have stopped the Ppvs processes, the virus may try to re-launch them. For this reason, you must now boot your PC in Safe Mode in order to prevent this from happening.
Step 4
*Gayn is a variant of Stop/DJVU. Source of claim SH can remove it.
Go to the Start Menu, search in it for Folder Options, and click on the Folder Options icon. Then open the View tab, enable Show hidden files, folders, and drives, and select OK.
After that, open the Start Menu again, type %Temp%, and press Enter. When the Temp folder opens, press Ctrl + A, then press Del, and click Yes to confirm that you want to delete the selected items (all items in Temp must be deleted).
Next, in the same way, visit the next four folders, but in them only delete the most recently-created items – everything that has been created since the Ransomware infected your PC:
- %AppData%
- %WinDir%
- %LocalAppData%
- %ProgramData%
Step 5
If your computer is running on Windows 10, you must once again open the Task Manager and this time go to the Startup section. If you have Windows 7 on your computer, then you must type msconfig in the search bar of the Start Menu, hit Enter, and then click on the Startup tab when the System Configuration window shows up. When you have the list of startup items shown on your screen, look through them carefully, and if you notice once that seem unfamiliar, suspicious, or related to Ppvs, disable them, and then click OK.
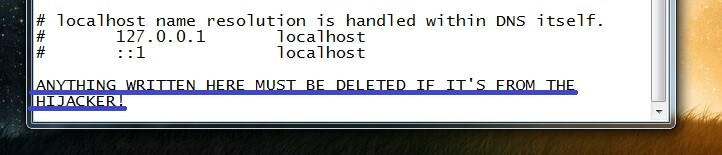
After this, you must open your C: drive, find the Windows\Syste32\drivers\etc folder, and double-click on the Hosts file that’s located in that folder. Select Notepad when you must choose what program to use to open the file with, and when the file opens, copy any text that may be written in it under the “Localhost” lines (at the bottom). Send us the copied text (likely some strange IP addresses) down in the comments and wait for us to reply to your comment, telling you if that text must be erased from the Hosts file on your PC.
Use the Start Menu search to find the Task Scheduler tool, open that tool, and click on Task Scheduler Library in the top-left. Now see what tasks get listed and if there are ones that seem questionable or malicious, right-click them, select Delete, and confirm the deletion of the task.

Step 6
Open the Registry Editor by searching for regedit.exe in the Start Menu, pressing Enter, and then clicking Yes to provide your Admin permission. When the Registry Editor window appears on your screen, click the Edit menu from the top, select Find, type the name of the virus in the search box, and search related items. If a search result shows up, delete it, and search for more malware entries in order to delete them as well. Once no more results are getting found, search for the name of the program from Step 1 and delete anything related to it that may get found.
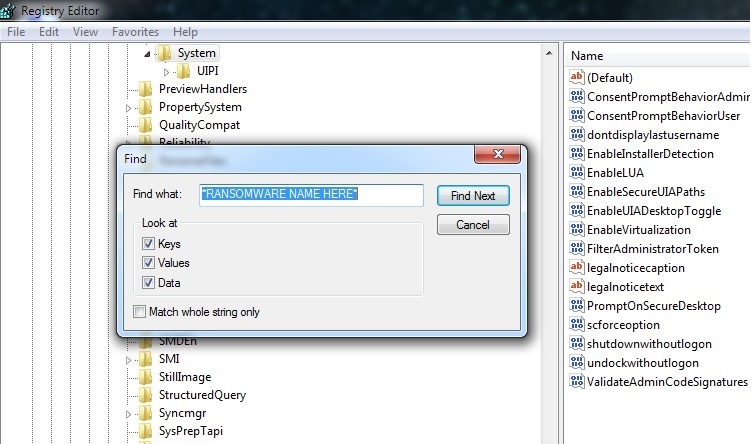
Lastly, open the Registry locations shown below in the left panel of the Editor, search them for items with strange names that look like this “3209ru8943ur390yt3490gyu53t0jf094ut90j“, and let us know in the comments if you see any such items – we will soon reply to your comment, informing you if the item/s in question must be erased.
- HKEY_CURRENT_USER > Software
- HKEY_CURRENT_USER > Software > Microsoft > Windows > CurrentVersion > Run
- HKEY_CURRENT_USER > Software > Microsoft > Internet Explorer > Main
If Ppvs is still in the system
In some instances, manually deleting a virus like Ppvs may not be a viable option due to different reasons – the virus may have nested itself too deep inside the system, other malware may be helping it stay on the computer, and so on. It’s, therefore, advised that, if the steps you’ve completed thus far didn’t allow you to fully delete Ppvs, you use a specialized removal tool to clean your system. The anti-malware program linked in the guide is what we’d recommend you use to get rid of Ppvs – it is a powerful removal software that will not only allow you to maker your PC malware-free again, but will also ensure that the system stays that way in the future.
How to Decrypt Ppvs files
To decrypt Ppvs files, the recommended course of action is to use a free decryptor tool created specifically for this virus. There aren’t such tools for each Ransomware virus, but there’s one that may help you decrypt Ppvs files, so we advise you to give it a try.
There are two conditions that must be met before using the decryptor tool that we will tell you about shortly:
First, the computer must no longer have Ppvs or any other malware in it, so you must have completed the guide and/or used the removal tool linked in it to ensure that Ppvs is removed. If there’s any data left on your PC that may be linked to the virus, use the free malware scanner we have on our site to test those files for malicious code, so that you’d know to delete them if they get flagged as malware.
The second condition is that you need to have a couple of file pairs, where one of the files is encrypted by Ppvs and the other one is the accessible, original version of that file. Search through your other devices, email accounts, or cloud storages to find some original and still accessible file versions of their encrypted counterparts. The condition concerning the files is that they should to be bigger than 150 KB.
If your PC is malware-free and you have the needed file pairs, here is how to decrypt Ppvs files on your PC:
- First, visit this link, select the first of the two Choose File options, navigate to the encrypted file version from one of the file pairs, and open it.
- Next, click the other Choose File option, find the original version of the encrypted Ppvs file from the previous step, and open it too.
- Select Submit and wait for the needed Ppvs decryption key to get extracted. If the process fails, try it again using another Ppvs file pair.
- Once a decryption key has been found, open this link and download the tool available there.
- Go to the downloaded tool, right-click it, select Open as Administrator, and select Yes.
- Agree to the Terms and Conditions of the program, and then click OK, after reading the instructions.
- Select a drive or browser to a specific location where there are encrypted Ppvs files, and then click on Decrypt. This process should now unlock the encrypted files in the selected drive/location. If any of the files get skipped and don’t get unlocked, this means that a different Ppvs key is needed to decrypt them. You can try to extract a different key using another file pair, but know that it’s possible that the needed Ppvs decryption key may be absent from the decryptor’s database.

0.0.0.0 www(.)bandicam(.)com
0.0.0.0 bandicam(.)com
0.0.0.0 www(.)bandisoft(.)com
0.0.0.0 bandisoft(.)com
0.0.0.0 cert(.)bandicam(.)com
0.0.0.0 ssl(.)bandisoft(.)com
Hi Sina,
you can safely remove these entries.