*Ppvt is a variant of Stop/DJVU. Source of claim SH can remove it.
Ppvt File
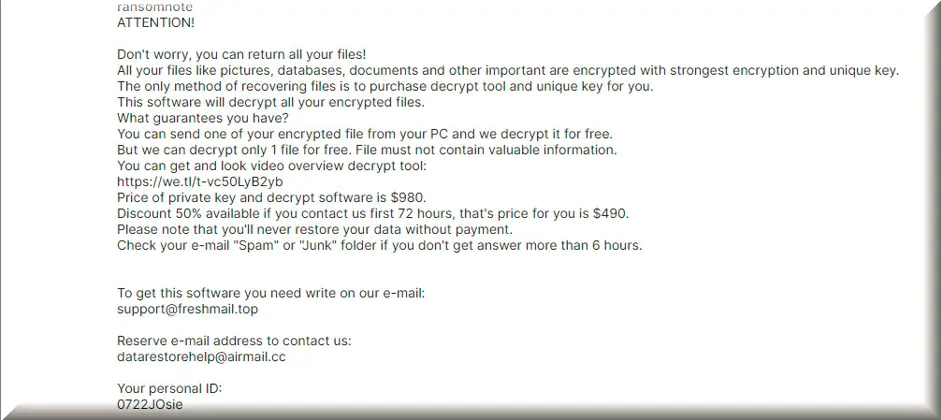
The Ppvt file is a ransomware threat that is related to a technique that cybercriminals use to lock up your data and hold it hostage. When this ransomware infiltrates your computer, it carefully selects certain files to target, often those with sentimental or business value. It then employs a complex encryption algorithm, a bit like turning your data into a secret code that only the attackers can understand. The result is that your files become unreadable gibberish, much like turning your carefully crafted essay into a jumble of letters. To make matters worse, the Ppvt file attackers leave you a ransom note on your screen, demanding payment in cryptocurrency for the decryption key. Until you pay that ransom or explore alternative recovery methods, your files remain inaccessible, leaving you with a challenging dilemma to resolve.
Decrypting files that have been encrypted by the Ppvt ransomware should be approached with caution. It’s advisable to seek professional help from cybersecurity experts and trusted manual solutions that offer access to decryption tools because attempting to decrypt the files without the necessary expertise can lead to further data loss. While there is no guaranteed method, in some cases, security researchers may have developed decryption tools for specific ransomware strains like Ppvt. To check for potential solutions, refer to credible sources like cybersecurity blogs or official law enforcement websites. Remember, paying the ransom is discouraged, as it’s risky and supports criminal activities.
How to remove Ppvt ransomware virus and restore the files?
Removing the Ppvt ransomware virus and restoring your files is a challenging process. Therefore, seeking assistance from cybersecurity experts or researching the web for manual decryption tools or methods specific to Ppvt ransomware is the best thing you could do. Attempting manual removal without proper guidance can be risky, so it’s best left to the professionals or to powerful software solutions. When it comes to file restoration, use clean and unaffected backups of your data if you have them and ensure these backups are free from malware. It’s crucial to refrain from paying the ransom, as it supports criminal activities and doesn’t guarantee file recovery.
Ppvt Virus
When the Ppvt virus encrypts your files, it acts as a virtual vault that has been sealed around your valuable data. The encryption process takes your files, such as personal photos, work documents, or financial records, and transforms them into an unintelligible state, much like turning your cherished memories into a series of random characters. You won’t be able to open or use these files because they’re locked behind a digital wall. Typically, the Ppvt virus attackers leave a ransom note on your computer screen and demand payment for the decryption key. Until you agree to their demands and pay the ransom, your files remain trapped, and the clock ticks, creating a sense of urgency and anxiety.
Ppvt
In the event of your files being encrypted by Ppvt, it’s essential to resist the temptation to pay the ransom, as it gives you no guarantee about the recovery of your data and financially supports criminals. Instead, what we suggest is to promptly report the incident to law enforcement agencies, which may help in tracing the cybercriminals involved and seek expert guidance from cybersecurity professionals or specialized manual removal tools. If you have clean, unaffected backups, you can use them to restore your system. However, don’t forget to minimize future risks by keeping your software up-to-date, implementing robust password practices, installing reliable antivirus software, and educating yourself about effective ransomware prevention measures.
.Ppvt
Even tough it may look like everything is lost, there are methods to decrypt .Ppvt-encrypted files without giving in to the ransom demands, although success is not guaranteed. Occasionally, cybersecurity experts manage to crack the encryption employed by certain ransomware variants, resulting in the release of free decryption tools that can help victims recover their files. Alternatively, if you have secure and up-to-date backups of your .Ppvt data, you can restore your files without paying the ransom. However, it’s imperative to approach online decryption tools with caution, as some can be malicious. Stick to trusted sources, such as reputable cybersecurity professionals and their resources to ensure the safety and efficacy of the decryption tools you use.
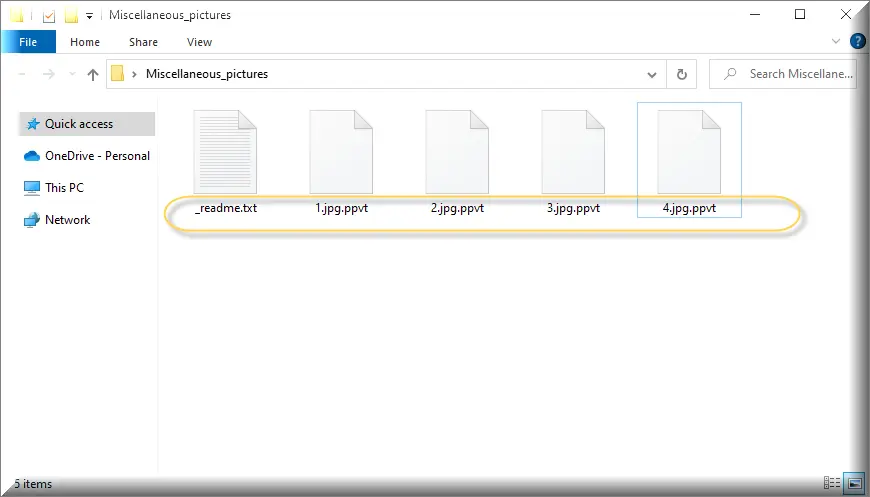
Ppvt Extension
Ransomware tends to be stealthy, but there are some potential signs that can give it away. For instance, before it encrypts your files, you can keep an eye out for sudden computer sluggishness or crashes, which can be indicators of ransomware activity in the background. Also, you can be cautious of suspicious emails, especially those with unexpected attachments or links, as they can serve as the initial infection vector. Once the ransomware encrypts your files, you’ll notice that their file extensions change, often to something like the Ppvt extension. These Ppvt, Zpww or Zpas extension files become inaccessible, and the attackers typically make their presence known by displaying a ransom note on your screen. This note serves as a clear indicator that your files have fallen victim to ransomware encryption.
Ppvt Ransomware
The Ppvt Ransomware attackers typically demand payment for decryption keys in cryptocurrency, like Bitcoin, because it gives them a level of anonymity that makes it difficult to trace the transactions back to them. However, paying the ransom is strongly discouraged for several reasons: it’s a risky endeavor with no guarantee of receiving the Ppvt ransomware decryption key, it financially supports criminal activities, and it perpetuates the ransomware cycle. Instead, a safer and more reliable option is to recover your files from clean and unaffected backups, assuming you have them available. This approach not only avoids contributing to criminal activity but also ensures the security and integrity of your data.
What is Ppvt File?
A ransomware threat is like a digital locksmith with a master key that can potentially encrypt all types of files on your computer. It doesn’t care whether it’s a Word document, a family photo, a financial spreadsheet, or a specialized database file—if it’s accessible, it can immediately turn it into an encrypted Ppvt file. The ransomware attackers want to maximize their impact and the likelihood that you’ll pay the ransom, so they target a wide range of file types that are valuable to both individuals and organizations. This all-encompassing approach underscores the importance of proactive cybersecurity measures and regular data backups to mitigate the risks associated with Ppvt file encryption and ransomware attacks.
SUMMARY:
| Name | Ppvt |
| Type | Ransomware |
| Detection Tool |
*Ppvt is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Ppvt Ransomware

During the removal of Ppvt, your computer may need to be restarted numerous times. Therefore, you should bookmark this page with instructions in your browser, or just open it on another device so that you may refer back and forth as many times as necessary.
Afterwards, restart the computer in Safe Mode (click on this link for instructions), and then, once the computer restarts, follow the rest of the instructions from this step.
Use the Windows search bar (in the Start menu or at the bottom left for Windows 10) type msconfig and press Enter. You will open System Configuration in a second.

Choose Startup from the tabs at the top, and uncheck any items that you suspect are not authentic and might be related to the ransomware.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Ppvt is a variant of Stop/DJVU. Source of claim SH can remove it.
After eliminating the suspicious-looking items from the startup list, close the System Configuration window and press CTRL + SHIFT + ESC from the keyboard.
The next step is to check the Task Manager for suspicious processes, such as those with weird names, high CPU and memory use, and so on, and see if you can identify anything harmful.
If you locate a questionable process in the Processes tab of the Task Manager, right-click on it and select Open File Location from the pop-up list of options.

To be sure that the files of that process are legitimate, you can run them through the powerful free virus scanner below.

If they contain malware, stop the process that uses them and remove the files from their directories.
![]()
Next, you need to access your computer’s Hosts file and check it for any malicious IP addresses. This file may be opened by pressing Windows and R keys together and typing the following into the Run command box:
notepad %windir%/system32/Drivers/etc/hosts
Find Localhost in the text and see if any suspicious IPs have been added below, just like on the example image:

Don’t delete anything until you confirm that it is problematic. If you find something unusual in your Hosts file, let us know in the comments, and we’ll respond with recommendations on how to proceed.
![]()
*Ppvt is a variant of Stop/DJVU. Source of claim SH can remove it.
The next step is to check your system’s registry for malicious entries linked to Ppvt and remove any that you find. To do so, type Regedit into the Windows search bar, and then click on the Registry Editor from the results.
After pressing CTRL and F together, type the ransomware infection’s exact name into the search box that opens in the Registry Editor and hit Enter. Then, press the Find Next button. It’s quite likely that anything that shows in the search results could be linked to the ransomware and should be removed.
Important! Do not remove anything if you are unsure whether it is part of the infection or not, since this might cause damage to your operating system. Instead, scan your system and registry using a professional removal program.
Once you’ve closed the editor, go to the Windows search bar, type each of the following search terms one by one and open them.
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Look for any newly added files and folders in the locations above, and if you find something that you are sure belongs to the ransomware, remove it.
Remove everything from the Temp folder at the end. The malware may have created temporary files that you don’t need to keep.
![]()
How to Decrypt Ppvt files
If you want to have a greater chance to recover your encrypted data, make sure that you first get rid of Ppvt and other viruses that might be hiding inside your system. If you are not a professional, it’s recommended to use professional anti-virus software like the one on this page.
Once you are sure that Ppvt has been entirely deleted from your computer, you can safely proceed to the following file-recovery steps:
Depending on the ransomware type that has attacked you, the procedure for decrypting encrypted data may be different. Therefore, it is important to determine the ransomware’s version by checking the file extension that has been added to the encrypted files.
New Djvu Ransomware
STOP Djvu is the latest Djvu ransomware version that is actively targeting users online. You can easily recognize that you have been attacked with this version because the encrypted files of this ransomware contain the .Ppvt extension.
Currently, the only chance for decrypting data encoded by STOP Djvu is if those files have been encrypted with an offline key. If this is your situation, you may want to try to decrypt your data using this decryptor:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
On the linked page, the STOPDjvu.exe file may be downloaded by clicking the blue Download button upper right.
When you save the file on the computer, choose “Run as Administrator” and then press the Yes button to run the software. The decryption process will begin when you’ve read the agreement and the short instructions and clicked the Decrypt button. Keep in mind that this decryptor is unable to decode data encrypted using unknown offline or online keys.
We would love to know if the instructions above work for you, or if you have any troubles with our Ppvt removal guide. Also, please note that you may save time and remove the ransomware quickly with the help of the anti-virus software on this page. If there are any suspicious-looking files that you want to check, you can use the free online virus scanner from this site.

Leave a Comment