Privatemsg.site
Privatemsg.site is what is known as a browser-hijacker extension popular browsers and its main job is to flood your screen with ads and redirect you to its partnering sites. Privatemsg.site does this by hijacking your browser’s settings and introducing unwanted changes to them.
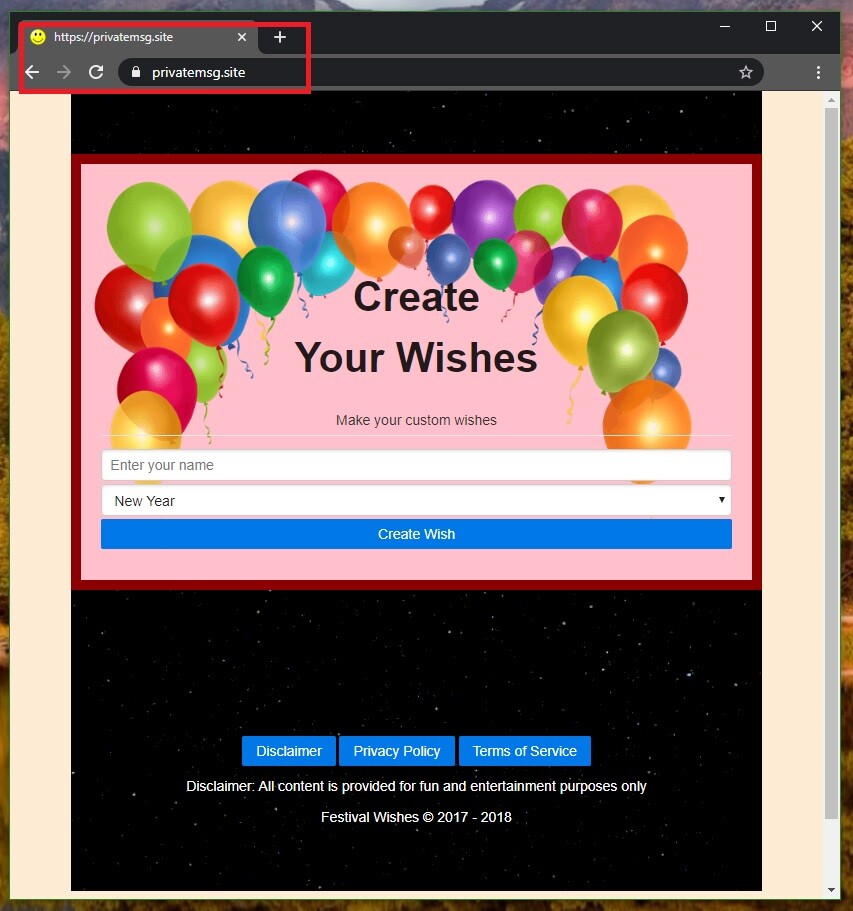
The Privatemsg.site Virus will display pop up ads and messages
If you are struggling to find a way to remove this unwanted from your system, know that we can help you with its uninstallation in the current article. If you really cannot wait to rid your browser of the endless page-redirecting and ad-spamming activities, you could directly scroll down to the removal guide at the bottom of this page and follow the instructions to remove Privatemsg.site. However, we advise you to first read the paragraphs that lead up to the guide in order to learn what type of software Privatemsg.site is and how dangerous it could be to your system.
As we already said, this piece of unwanted software is a browser hijacker and it can take over any browser (Chrome, Firefox, Opera, and so on) and force it to aggressively spam you with ads and page-redirect your searches to unknown pages and sites.
Privatemsg
To achieve its goals, Privatemsg may alter the homepage and the search engine of the browser, as well as add new toolbar buttons or install other unwelcome components in the browser. The end-goal of Privatemsg is to get you to visit the sites of people who have paid to the hijacker’s creators for providing their sites with more exposure.
This is why the homepage of your browser has likely been changed and why the new search engine that the hijacker has forcefully installed in the browser seems to favour sites that have paid for advertisement instead of showing you the most relevant results.
All of this could certainly make it more difficult for you to use your browser normally. However, what’s even worse is that the hijacker’s activities may expose the system to more hazardous pieces of software. What you must realize about apps like Privatemsg.site is that their main goal is to advertise and because of this there’s little to no quality control over the ads you are getting spammed with. The hijacker may show you relevant adverts of legitimate offers but it may also show you fake clickbait ads that could be linked to harmful sites and phishing pages. It is no secret that the use of deceitful malicious ads is one of the main methods for spreading threats like Trojans and Ransomware, which is why you must be careful every time you see questionable adverts in your browser. Generally, it is best to remove the hijacker from your computer as this will put an end to its ad-generating and page-redirecting activities. To uninstall Privatemsg.site and decrease the chances of getting exposed to Trojans, Ransomware, Spyware, and other threats, however, you may need our help as removing a browser hijacker is typically not easy if you’ve never dealt with similar software in the past. That is why we advise you to check out the next guide and try to complete all of its steps exactly as instructed.
SUMMARY:
| Name | Privatemsg.site |
| Type | Browser Hijacker |
Remove Privatemsg.site Virus
If you have an Android virus, continue with the guide below.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have a Windows virus, please use our Windows Virus Removal guide.
![]()
Whether you use the default “Internet” App for browsing or a different browser like Chrome you need to go to:
Settings/More/Application Manager/All
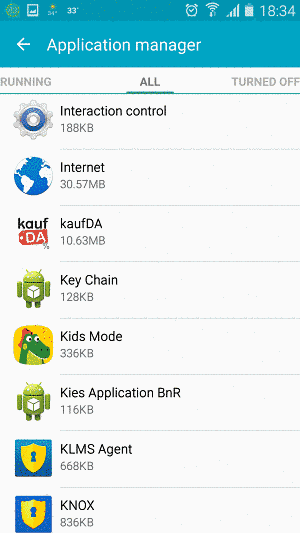
Locate the Browser/App in question and tap on it.
![]()
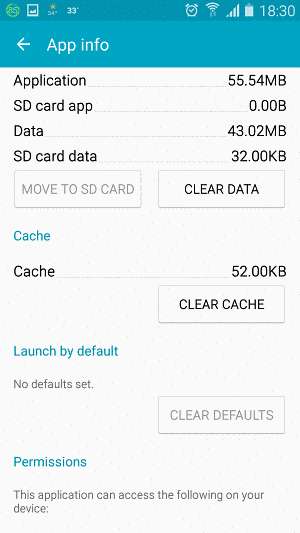
Now the method is effectively the same for users using both “Internet” and Chrome/Other Browsers, yet for more clarity we have provided instructions for both:
For “Internet” Browser Users:
Tap the Force Stop button.
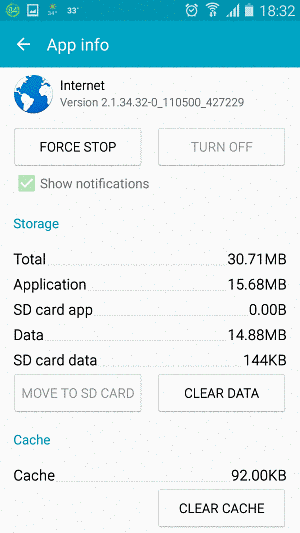
Now tap the Clear Data and Clear Cache Buttons.
For Google Chrome Users:
Click on Force Stop.
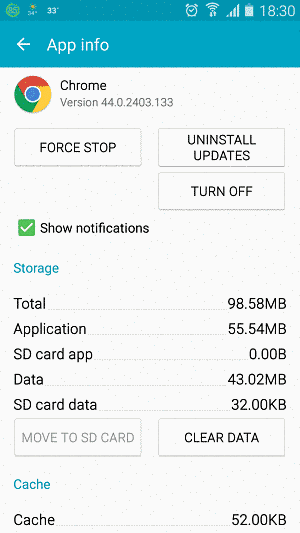
Then click on Clear Data and Clear Cache.
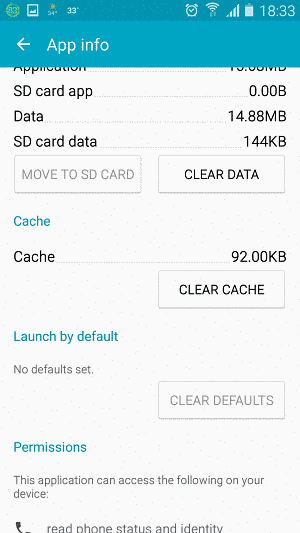
![]()
Restart your Browser. It might be a good idea to Reboot your Android device, just in case.
- Important!
If you are still seeing Ads in your browser, it is likely they are generated by the websites you visit and there is nothing you can do about it.
However, if you are seeing Adverts outside of your internet browser, then one of your installed Apps contains the problematic Adware. In this case you need to take a look at this guide.
Did we help you? Please, consider helping us by spreading the word!

Leave a Comment