PUAbundler
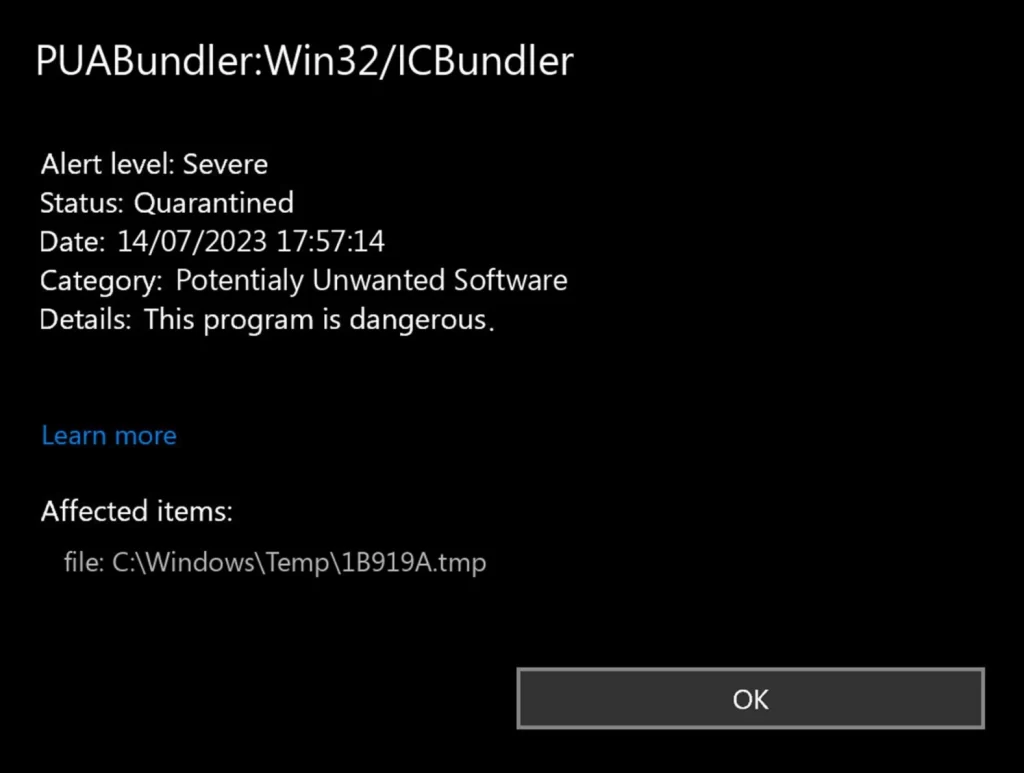
The PUABundler is a harmful detection by Windows Defender, possibly indicating a Trojan Horse infection. This infection can be triggered by a variety of sources, such as unverified downloads or compromised software, and can be linked to other similar detections, including puabundler:win32/rostpay, puabundler:win32/yandexbundled, and puabundler:win32/utorrent_bundleinstaller. Users have reported difficulty in removing it, as it cleverly hides in the system and can even resist standard remediation efforts. Even deleting associated files or programs may not entirely eradicate the threat. It’s crucial not to ignore any alerts related to PUAbundler, as neglecting it can cause significant damage. If manual removal proves unsuccessful, deploying a robust anti-malware tool, like the one liked on this page, can be effective in thoroughly purging the system of this persistent threat.
What is PUAbundler win32
PUAbundler win32 is a Windows Defender detection alert that warns you about the presence of a potential threat, such as a Trojan Horse virus, on your computer. It’s crucial that you do not ignore any such threats and do everything you can to identify their source and eliminate it. Oftentimes, PUAbundler Win32 is delivered via installation bundles, questionable downloads, and pirate sites, so be sure to avoid those in the future to keep your system safe.
The PUAbundler Win32 Virus
The PUAbundler Win32 virus detection is often indicative of a Trojan Horse infection, a form of malware known for stealthy infiltration. Trojan Horses typically hitch a ride with other software, often disguising themselves as legitimate programs or hiding within complex software bundles. In this case, the PUAbundler Win32 virus has been observed within downloads such as ‘uTorrent.exe’. This suggests it’s often distributed through downloads from unverified sources or packaged within pirated software. Furthermore, this threat is linked to other similar detections, such as puabundler:win32/mediaget, puabundler:win32/msetup, puabundler win32/ytdvideodownload, puabundler, and win32/photoscapebundler. Therefore, to stay safe, it’s critical to download software only from trusted sources and regularly scan your system with a reliable antivirus. Exercising caution with downloads can greatly decrease the risk of unintentionally installing such harmful threats.

PUAbundler:Win32
The PUABundler:Win32 detection is associated with a Trojan Horse virus, a type of malware notorious for their harmful potential. Such threats (PUADIManager Win32 OfferCore, PUADIManager Win32/InstallCore) may perform a variety of destructive actions like data theft, file corruption, and even total system compromise. Moreover, they may open backdoors for other malware like ransomware, amplifying the damage inflicted. One user noted a significant system slowdown, with the CPU overrun and the cooling fan in overdrive. Despite the inconspicuous nature of PUAbundler:Win32, it’s crucial to act promptly. Delaying removal may lead to irreversible system damage, data loss, or privacy breaches. Therefore, it’s essential to regularly scan your system with a trusted antivirus and remove detected threats immediately to ensure your digital safety.
SUMMARY:
How to Remove PUAbundler
To try and remove PUAbundler Win32 quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the PUAbundler Win32 extension (as well as any other unfamiliar ones).
- Remove PUAbundler Win32 by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of PUAbundler Win32 and any other suspicious items.
If this does not work as described please follow our more detailed PUAbundler Win32 removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the PUAbundler Win32 app and kill its processes
Uninstall the PUAbundler Win32 app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from PUAbundler Win32. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one like PUAbundler Win32, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything related to PUAbundler Win32 is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to PUAbundler Win32, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to PUAbundler Win32.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo PUAbundler Win32 changes made to different system settings
Undo PUAbundler Win32 changes made to different system settings
It’s possible that PUAbundler Win32 has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings by PUAbundler Win32 in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window


Leave a Reply