*Qore is a variant of Stop/DJVU. Source of claim SH can remove it.
Qore
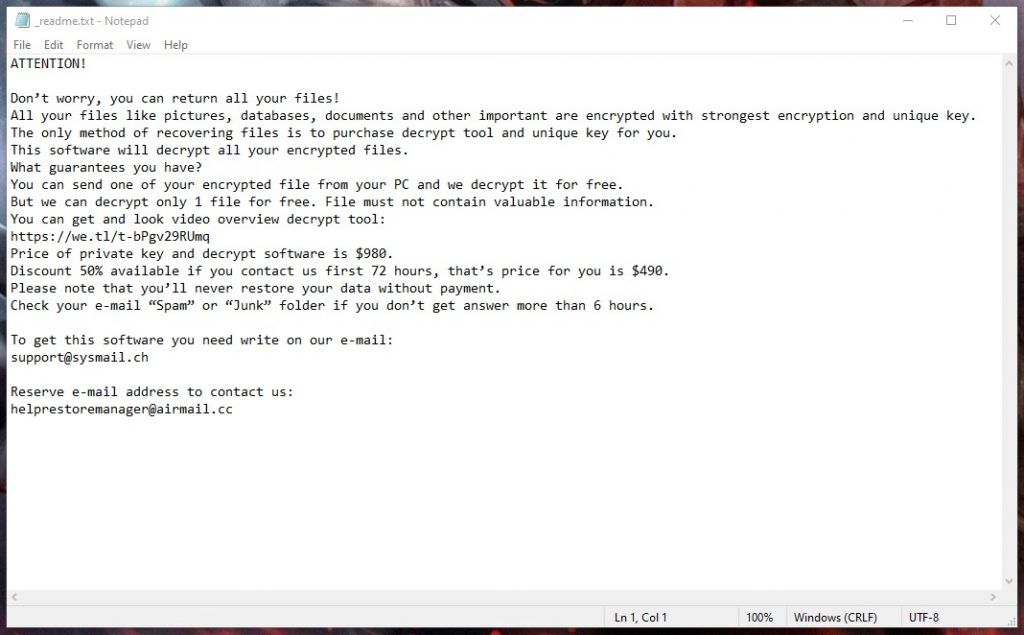
Qore is a ransomware virus created for the purpose of extorting money. The aim of Qore is to secretly invade a computer, encrypt its files and then ask for a ransom payment in order to decrypt them.
Unfortunately, this malware seems to spread very quickly, and we have received requests from many infected victims to help them remove Qore and restore some of their encrypted data. That’s why here we have prepared a useful guide on how to detect and manually delete the Ransomware files from your computer. Below, we will also share some information on how this dangerous threat spreads, how it encrypts digital data, and how you can take possible security measures against it. This information will certainly be helpful if you are interested in minimizing the negative effects of Qore and preventing future Ransomware infections.
The Qore virus
The Qore virus is a program with malicious intentions, developed for the purpose of money extortion. The Qore virus typically infects computers without the users’ knowledge, takes data stored there hostage through encryption and then demands a ransom payment in order to liberate it.

Ransomware is one of the most popular types of online threats you can be faced with nowadays. Each new variant is more advanced than the previous versions and thus, more complex to remove and deal with. The same is the case with Qore and Qopz which are cryptoviruses that holds the data on the infected computer hostage by encrypting it with a powerful and complex algorithm. When encrypted, the data will be inaccessible without a uniquely generated decryption key that is in the hands of the criminals who control the Ransomware. They usually require a certain amount of money from their victims (usually in Bitcoins) to be paid in exchange for receiving that key. The ability of the hackers to remain unknown and the huge profit they can make from the victims who pay them is what makes this nasty criminal “business model” even more appealing and common among cyber criminals.
The Qore file encryption
The Qore file encryption is a method that the hackers behind the Qore ransomware use to restrict access to a list of digital files. The Qore file encryption is a secret process that runs in the background of the system and rarely shows visible symptoms.
No doubt it is an extremely bad feeling to lose access to your important data. But being impulsive and in panic will certainly not help you to deal with the situation. As a ransomware victim, don’t forget that you are dealing with unscrupulous cyber criminals, who would do everything in their power to extort money from you. They can threaten you, send you a short payment deadline, pretend to be some authorities, create stories, or even take over your infected computer and inject other viruses into it.
Therefore, every online safety expert would tell you that paying the ransom that the criminals require is the worst thing that you could do. For one, you cannot trust the offenders to give you the decryption key even if you pay, and for second, there is no assurance that this mysterious key will work and will really make your files accessible again. Thankfully, you have a choice – remove Qore with the help of the instructions below and try some alternative file-recovery options like those mentioned in the removal guide below.
SUMMARY:
| Name | Qore |
| Type | Ransomware |
| Detection Tool |
*Qore is a variant of Stop/DJVU. Source of claim SH can remove it.
Remove Qore Ransomware

Restarting the computer multiple times may be required during some of the steps below if you want to remove all ransomware-related records from the system. For this reason, we recommend bookmarking this page with Qore removal instructions on your browser before proceeding further. In this way, you’ll be able to pick up just where you left off when you reboot.
And speaking about system reboots, we recommend rebooting your PC in Safe Mode (please check this link for detailed instructions on that) so that only the most essential system processes and apps can run on your system, and you can easily spot any potential danger.
As soon as your computer has restarted in Safe Mode, refer back to this article and follow the rest of the steps below.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Qore is a variant of Stop/DJVU. Source of claim SH can remove it.
Many malicious processes may be secretly running in the Processes tab of Task Manager after a ransomware virus like Qore has infected your machine. To detect and stop these processes, you need to press CTRL, SHIFT, and ESC simultaneously, click on the Processes Tab and look for processes with strange names or unusually high CPU and Memory usage.
If you come across something that looks problematic, right-click on it and select Open File Location from the list of options.

Next, run the files connected to that process through a scan by using the free online virus scanning tool below to check if they contain dangerous code:

Scanning the files may take some time because each of them is being checked thoroughly for maximum accuracy. If any malicious files are identified in the scan results, right-click on the process and select End Process to stop it from running. Then delete the infected files from the File Location folder.
To be absolutely sure that nothing harmful is operating in the background, we recommend that you repeat the instructions above for every process that looks questionable and run it through the scanner.
![]()
Ransomware infections commonly have the ability to change important system files and folders without displaying any symptoms. Malicious code often finds a home in the computer’s Hosts file. That’s why in the third step of this guide, we will show you how to check your Hosts file to see if anything has been added or changed there without your permission.
Simply press and hold the WinKey and R key simultaneously, then paste the following text in the Run box that will pop up on the screen:
notepad %windir%/system32/Drivers/etc/hosts
In the text of the file, find Localhost and see if anything unusual has been added below. Let us know in the comments if you come across strange-looking IPs like the ones shown in the following image:

We’ll look into these IP addresses and let you know if you need to take any action.
Once infected with Qore, the Startup tab in System Configuration is the next location to look for modifications. To access it, type msconfig in the Windows Search box and press the Enter key on your keyboard. After that, navigate to the Startup tab:

Look at the list and try to isolate startup items that don’t appear to be associated with any of your computer’s legitimate apps. You can disable a suspicious item by unchecking its checkbox, and then click the OK button at the bottom to save your changes.
![]()
If you want to get rid of any traces of Qore on your affected PC, the next step is to search the Registry for dangerous entries and carefully delete them. To do this, type “Regedit” into the Start menu search field and hit Enter.
After that, open a Find box inside the Registry Editor by pressing CTRL and F simultaneously. Start a search in the Registry by typing the name of the Ransomware that has infected you and then click the Find Next button. It’s best to remove any entries with that name if they show up in the results.
Attention! Entries that are associated with essential programs or OS functions should not be removed, otherwise, this may damage the OS in a very serious way. To avoid that risk, use a professional removal program that can scan your computer for hazardous registry entries and remove any danger that might be hiding inside.
Next, once the Registry is clean, you need to close the Registry Editor window and use the Start menu search bar to find and open each of the five locations listed below:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
When you open each of the folders, look for files and subfolders that have been added recently or around the time of the ransomware attack has hit you.
Qore may have left behind temporary files, so be sure to delete everything that is stored in Temp. In the rest of the places, just look for anything unusual that might be related to Qore.
![]()
How to Decrypt Qore files
Please ensure that your PC is free of any Qore-related traces before accessing the file recovery guide on this link.
New Djvu Ransomware
STOP Djvu is a ransomware variant that many online users have lately encountered. In most cases, files with the .Qore file suffix indicate that they’ve been infected with this specific variant of ransomware. If you’ve made sure your computer is free of viruses, you may be able to retrieve some of your data by using a decryption program like the one available at the following website:
https://www.emsisoft.com/ransomware-decryption-tools/stop-djvu
The license agreement and any other instructions that come with the decryptor program should always be carefully reviewed before decrypting a file. Remember that this tool may not be able to decrypt your files if they were encrypted with an unknown offline key or online encryption.
A comprehensive system scan with professional malware removal software or a free online virus scanner is the best way to check for hidden traces of the infection. Once your machine has been checked, and if nothing disturbing is found, you can safely proceed to the file recovery steps from the link.

Leave a Comment