What is Re-captha-version-3-275.buzz and what objectives does it serve?
Re-captha-version-3-275.buzz is a browser hijacker that affects the standard way a user’s browser operates. It alters the homepage, and the default search engine, and redirects web searches to pages with advertisements. It may also insert ads directly into your browsing sessions depending on which browser you are using (confirmed for Chrome).
The general objective of this software is to increase its advertising revenue from sponsored clicks by forcing users to view and interact with sponsored content. Re-captha-version-3-275.buzz may also gather user data from their browsing activities, and sell it to outside parties, or use it for more aggressive advertising.
Is Re-captha-version-3-275.buzz a trusted site?
We did a research and found that Re-captha-version-3-275.buzz has a very low trust score. The site has been registered just recently and the identity of its owner is hidden on the WHOIS platform. This alone is enough to serve as a red flag, but if we add it to the browsing disturbance from above, it is clear that you should be very careful if you come across this page. In fact, we strongly advise you to confirm that anything you come across is not an online scam before you interact with its content.
What we discovered about Re-captha-version-3-275.buzz?
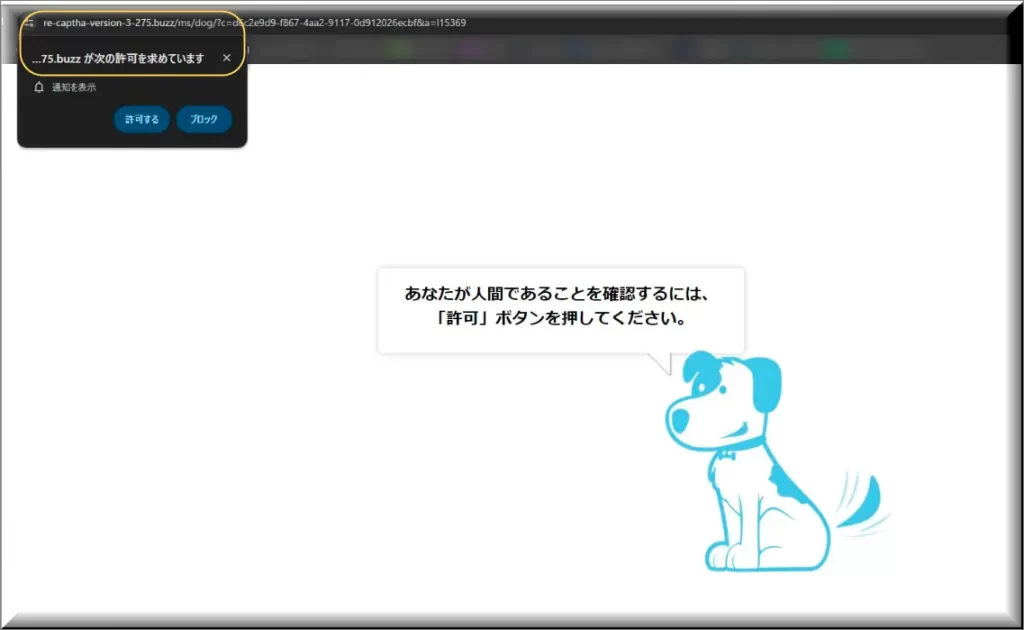
Our more detailed analysis uncovered a concerning issue related to the “Re-captha-version-3-275.buzz” threat. We noted that this browser hijackers exhibits irregular and deceptive behavior on certain websites. Twitter users have reported that, upon initial access to a URL from a Google search, a suspicious verification screen prompts them to “Confirm that you are a human”.
This screen only appears during the first visit, via a particular IP address. Subsequent visits display the normal website content. However, this pattern changes if the IP address is altered, such as when switching to a different network.
Such behavior suggests a targeted mechanism that could be employing IP tracking to selectively display content, which hints at potential underlying malicious activities.
Our further investigation showed that the questioned URL employs redirection – a trick frequently employed to hide the genuine purpose of a compromised website. We assume that the reason for this redirection may be that it is meant to be subtle, so that users and security systems cannot easily notice it when they make repeated visits.
The fact that the malicious redirection has not yet been flagged by search engine crawlers in Google search results implies that it is a relatively new development. Such deceptive practices would usually result in the site being removed entirely or penalized in search rankings if confirmed by subsequent crawling.
By what means does Re-captha-version-3-275.buzz infiltrate computer systems?
Re-captha-version-3-275.buzz typically infiltrates computer systems through bundled software installations, where it conceals itself within the setup processes of applications. Users often inadvertently agree to install the hijacker by not deselecting offers during installation. It can also spread via links, email attachments or compromised advertisements that trigger downloads when interacted with. Most commonly, however, users “Allow” this software to display notifications and make changes to their web browser by clicking on pop-up windows that appear on questionable sites.
What are the potential consequences of neglectic Re-captha-version-3-275.buzz?
Neglecting or underestimating Re-captha-version-3-275.buzz can lead to some negative consequences. Apart from the nuisance of ads and redirects, such hijackers can diminish system performance and stability. They can also create security vulnerabilities that malware infections can exploit or expose users to phishing sites where they personal data could be stolen.
How does Re-captha-version-3-275.buzz compare to viruses in terms of danger level?
Re-captha-version-3-275.buzz and other browser hijackers are generally regarded as less dangerous than viruses. They do, however, pose a security risk. In contrast to viruses, which have the ability to spread quickly and cause harm, hijackers usually concentrate on changing browser settings, and collecting user data. They may, however, serve as malware entry points and expose users to a range of cybersecurity risks. Compared to conventional viruses, this gives them a significant, though indirect, potential for harm.
What role do browser security features play in mitigating the risks posed by Re-captha-version-3-275.buzz?
Browser security features play a major factor in reducing the risks, associated with hijackers, such as Re-captha-version-3-275.buzz. Popular web browsers like Chrome, Edge and Firefox have pop-up blockers, and other features, that keep aggressive advertisements from messing with your online experiences.
They also have an anti-phishing technology that recognizes and blocks phishing websites. The majority of browsers also offer the ability to return any settings to their default state. This enables users to swiftly reverse modifications made by hijackers. If you regularly update your browsers, you will enhance these defenses, and fix vulnerabilities that could be exploited by malware.
SUMMARY:
| Name | Re-captha-version-3-275.buzz |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Re-captha-version-3-275.buzz Virus
To try and remove Re-captha-version-3-275.buzz quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Re-captha-version-3-275.buzz extension (as well as any other unfamiliar ones).
- Remove Re-captha-version-3-275.buzz by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Re-captha-version-3-275.buzz and any other suspicious items.
If this does not work as described please follow our more detailed Re-captha-version-3-275.buzz removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Re-captha-version-3-275.buzz app and kill its processes
Uninstall the Re-captha-version-3-275.buzz app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Re-captha-version-3-275.buzz. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Re-captha-version-3-275.buzz, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Re-captha-version-3-275.buzz.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Re-captha-version-3-275.buzz changes made to different system settings
Undo Re-captha-version-3-275.buzz changes made to different system settings
It’s possible that Re-captha-version-3-275.buzz has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Re-captha-version-3-275.buzz from your browsers
Remove Re-captha-version-3-275.buzz from your browsers
- Delete Re-captha-version-3-275.buzz from Chrome
- Delete Re-captha-version-3-275.buzz from Firefox
- Delete Re-captha-version-3-275.buzz from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.
What proactive measures can users adapt to stay away from Re-captha-version-3-275.buzz?
There are some steps and security practices that you can use to greatly reduce the risk of becoming victims of browser hijackers like Re-captha-version-3-275.buzz.
We have said this hundreds of times, but updating your web browser, operating system, and security software is essential. Patches and fixes for known vulnerabilities that hackers exploit are frequently included in these updates. Moreover, you can invest some money on antivirus or antimalware software, which provides an additional line of defense against browser hijackers and some more dangerous threats. The purpose of these security tools is to find and remove software before it has a chance to harm your system. To prevent hijacking attempts, however, make sure your security program is configured for online protection, real-time scanning, and automatic updates.
Don’t click on arbitrary pop-up advertisements or download software from dubious websites, as well. Software bundles, free program bundles, and misleading advertisements are common ways for programs like Re-captha-version-3-275.buzz and Timotech.co.in to propagate. Thus, always make sure that the downloads and their settings are legitimate. Lastly, avoid clicking on alerts that request that you permit pop-ups or browser modifications.

Leave a Reply