The subject of this article is the removal of Timotech.co.in. In the event you know about this website, your computer is likely overloaded with notifications continuously popping from this site. You will likely be unable to remove Timotech.co.in with the normal removal option in your browser – this is why here you will find a step-by-step guide with all the information that you need.
What is Timotech.co.in, and what do we know about it?
In the cyberseuciry circles, Timotech.co.in is noted as a potentially unwanted software that modifies browser settings without the user’s knowledge or consent. What it does is to redirect all of your searches to the Timotech.co.in domain and fill in your browser with sponsored pop-ups. This can also lead to slow-downs during keyboard typing and performance degradation on websites like YouTube. These can generally be signs of browser hijacking, or of a background activity that is using system resources. Which in turn could be an entirely different kind of malware installed with the hijacker.
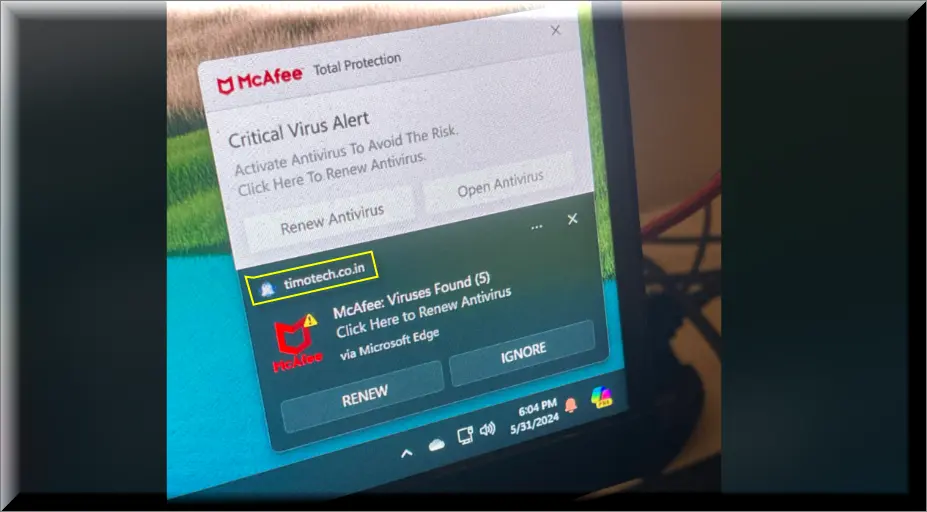
Our research suggests that victims experience persistent aggressive notifications from “timotech co inc.” People’s complaints point to the installation of this undesirable software being linked streaming sites, misleading advertisements or compromised pages.
The website is currently flagged by only two vendors on Total Virus. The inability of security programs to identify the threat usually mean that this is either a new strain, highly sophisticated, or effectively disguised. By our experience, it’s the first of these.
Is Timotech.co.in a threat to your PC?
To put it simply, Timotech.co.in is a website built by people who create questionable software in order to promote and display advertisements. This is the most frequently discovered type of rogue threat in the cybersecurity industry. When visited, the page will look and function normally for the majority of time. But at other times, without notice, and ad can lead to a malicious actor that stands behind genuinely frightening malware, such as Trojans or Ransomware.
This is the main issue with such sites. People who are not tech-savvy may click on these aggressive ads and end up purchasing or installing something questionable. You can never be certain that what you are viewing is the authentic and true version of the ad you would have normally seen.
Because Timotech.co.in and similar websites are set up to maximize profits as quickly as possible, they use aggressive promotional tactics without any considerations. After some time, the owners of the domain will give up on it and move on to the next one in case this one develops a bad reputation, or becomes detected by security software.
How does Timotech.co.in trick users to click the ads?
While doing our research on Timotech.co.in, we experienced the following. We clicked on a promoted link on our Chrome browser, and it led us to a pretty run-down streaming page. Since we did this in a safe virtual machine environment, we decided to click “Allow”. From that moment on we were bombarded with a stream of unwanted messages which not only covered our screen, but also redirected us to questionable webpages. These notification persisted automatically every couple of seconds.
How to identify Timotech.co.in?
The most popular method for identifying Timotech.co.in is to check if Google is the source of your search results. Another simple way to spot it is if your search queries are overrun with advertisements, that go beyond what is typical for Google sponsored links. This includes ads that look different from the norm or appear on pages which are not heavily ad-sponsored.
How is Timotech.co.in being distributed?
Aside from being found on streaming sites, Timotech.co.in may also be found in a bundle with other types of software, such as browser extensions or add-ons. In these situations, users inadvertently let the hijacker in when they rush through the installation process, and neglect to reject optional offers. We have frequently received a few requests to install unfamiliar extensions using this method. But, there are many other channels for hijackers, like Maxask and Boyu.com.tr, to get installed. For this reason, it is wise to be careful when interacting with browser notifications, different pop-ups or new software installation packages.
How to remove Timotech.co.in once and for all?
The first place to go to if you want to remove Timotech.co.in is in your browser’s settings. See if any strange or suspicious plugins or extensions are installed by looking for the “Extensions” menu, selecting it, and checking again. Uninstall any that are discovered. After that, set your browser back to its original factory settings. The majority of the adjustments should be gone once you do this.
You should also go into the control panel of your computer, and uninstall any apps related toTimotech.co.in. It is a good idea to use a security tool to perform an antivirus or anti-malware scan. Doing this will guarantee that your system is virus-free. Lastly, use the browser’s settings to return the homepage and search engine to the configurations you prefer.
SUMMARY:
| Name | Timotech.co.in |
| Type | Adware/Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Timotech.co.in Virus
To try and remove Timotech.co.in quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Timotech.co.in extension (as well as any other unfamiliar ones).
- Remove Timotech.co.in by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Timotech.co.in and any other suspicious items.
If this does not work as described please follow our more detailed Timotech.co.in removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Timotech.co.in app and kill its processes
Uninstall the Timotech.co.in app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Timotech.co.in. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Timotech.co.in, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Timotech.co.in.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Timotech.co.in changes made to different system settings
Undo Timotech.co.in changes made to different system settings
It’s possible that Timotech.co.in has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Timotech.co.in from your browsers
Remove Timotech.co.in from your browsers
- Delete Timotech.co.in from Chrome
- Delete Timotech.co.in from Firefox
- Delete Timotech.co.in from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Reply