Reackened.com may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
Reackened.com
When a user’s browser falls victim to a browser hijacker like Reackened.com, several noticeable changes occur that can disrupt their online routine. The homepage might transform into an unfamiliar website, and the default search engine could be replaced without their consent. Additionally, an influx of intrusive pop-up ads and banners may inundate their browsing sessions, causing annoyance and hindering smooth navigation. Unwanted Reackened.com browser extensions or toolbars may appear, altering the browser’s interface. Furthermore, attempts to access familiar websites could lead to unexpected redirections to unfamiliar or suspicious domains. These cumulative alterations collectively signal a browser hijacking, prompting users to recognize the intrusion and take prompt action to restore their browsing environment.
Is Reackened.com safe?
Reackened.com Virus
Reackened.com can often be called a Reackened.com virus due to its disruptive and invasive behavior that mirrors certain traits of real virus infections. For instance, this browser hijacker can modify browser settings without user consent, leading to sudden changes in the homepage, the search engine, and other configurations. This can prompt users to associate the unwanted alterations with the more commonly recognized concept of a virus. However, a virus aims to damage files and compromise system integrity, while a browser hijacker like the Reackened.com virus primarily focuses on redirecting users to specific sites, and generating revenue through advertising tactics. This resemblance in disruptive actions, coupled with the unfamiliarity of browser hijackers, contributes to the confusion between the two and the consequent misconception.
What is Reackened.com?
Reackened.com is a browser hijacker that stealthily alters a user’s web browser settings without their consent and starts redirecting them to unwanted websites, modifying the homepage and the search engine, or introducing unfamiliar toolbars and extensions. This intrusive software aims to manipulate the user’s online experience for the benefit of its creators, often by generating revenue through pay-per-click advertising or other intrusive activities. While not as destructive as viruses or malware, Reackened.com can significantly disrupt browsing activities, compromise privacy, and diminish overall user satisfaction, making its prompt identification and removal crucial for maintaining a secure and seamless online environment.
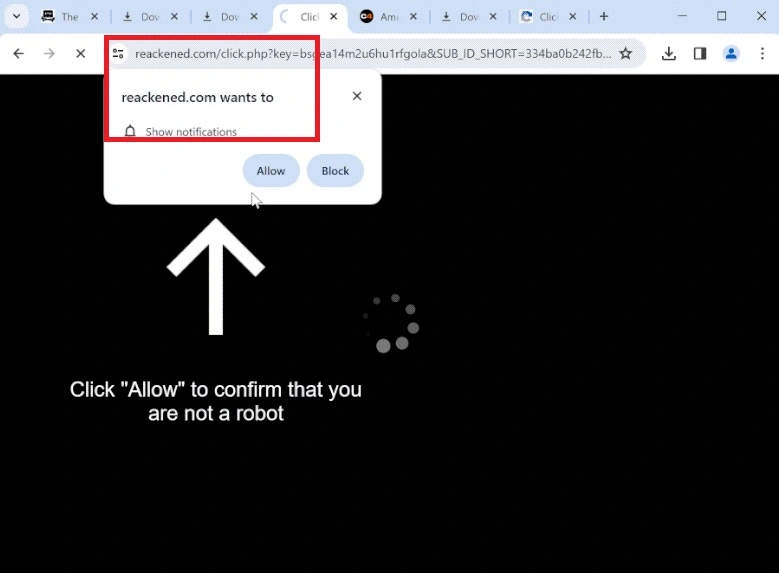
Reackened.com Pop-ups
One of the most noticeable indicators of browser hijacking is the sudden appearance of uninvited Reackened.com pop-ups that litter the screen, provoking rightful concerns. This visual disturbance holds a deeper significance. While not directly perilous, these Reackened.com pop-ups can inadvertently expose users to risks by enticing them to click on deceptive or malicious content. Despite their innocuous facade, these pop-ups might serve as conduits for malware downloads, phishing schemes, and data theft. Engaging with such pop-ups could reroute users to fraudulent websites, coax them into sharing sensitive details, or even trigger the installation of unwelcome and potentially harmful software. This dynamic interaction could compromise both online security and privacy, imperiling users with financial loss, identity compromise, and unauthorized access to personal data.
Reackened.com on Chrome
If you have found Reackened.com on Chrome (or another popular web browser) and are struggling to remove it, what you can do is check for any recently added software or browser extensions, as these may be the root cause of the unwelcome changes. Do not hesitate to remove any suspicious-looking applications that you cannot recall installing and uninstall any new extensions which you have not approved. After that, access your browser’s settings to manually restore your preferred homepage and default search engine settings. That should remove Reackened.com on Chrome, but if you want to check your system once again, you can run a thorough scan using reputable antivirus software that can detect and eliminate potential Reackened.com-related threats.
Reackened
One of the telltale signs of browser hijacking is the automatic redirection to specific websites like Reackened, Securitypatch.life or Ook.gg where your browser unexpectedly steers you towards these destinations against your wishes. This behavior arises due to the manipulation of your browser settings by the hijacker. The motive behind the auto-redirects primarily revolves around financial gain for the hijacker’s operators. By coercing you to visit certain sites like Reackened, they aim to increase website traffic and, subsequently, generate revenue through ads you may encounter. Essentially, it’s a strategy that capitalizes on your browsing activity, benefiting them financially, while you inadvertently find yourself navigating sites you never intended to explore.
SUMMARY:
| Name | Reackened.com |
| Type | Browser Hijacker |
| Detection Tool |
We tested that SpyHunter successfully removes Reackened.com* and we recommend downloading it. Manual removal may take hours, it can harm your system if you re not careful, and Reackened.com may reinstall itself at the end if you don't delete its core files. |
*Source of claim SH can remove it.
How to Remove Reackened.com
To try and remove Reackened.com quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Reackened.com extension (as well as any other unfamiliar ones).
- Remove Reackened.com by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Reackened.com and any other suspicious items.
If this does not work as described please follow our more detailed Reackened.com removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Reackened.com app and kill its processes
Uninstall the Reackened.com app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Reackened.com. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Reackened.com, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Reackened.com.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Reackened.com changes made to different system settings
Undo Reackened.com changes made to different system settings
It’s possible that Reackened.com has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for specific system elements that may have been affected, and pressing Enter to open them and see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Reackened.com from your browsers
Remove Reackened.com from your browsers
- Delete Reackened.com from Chrome
- Delete Reackened.com from Firefox
- Delete Reackened.com from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.


Leave a Reply