*Source of claim SH can remove it.
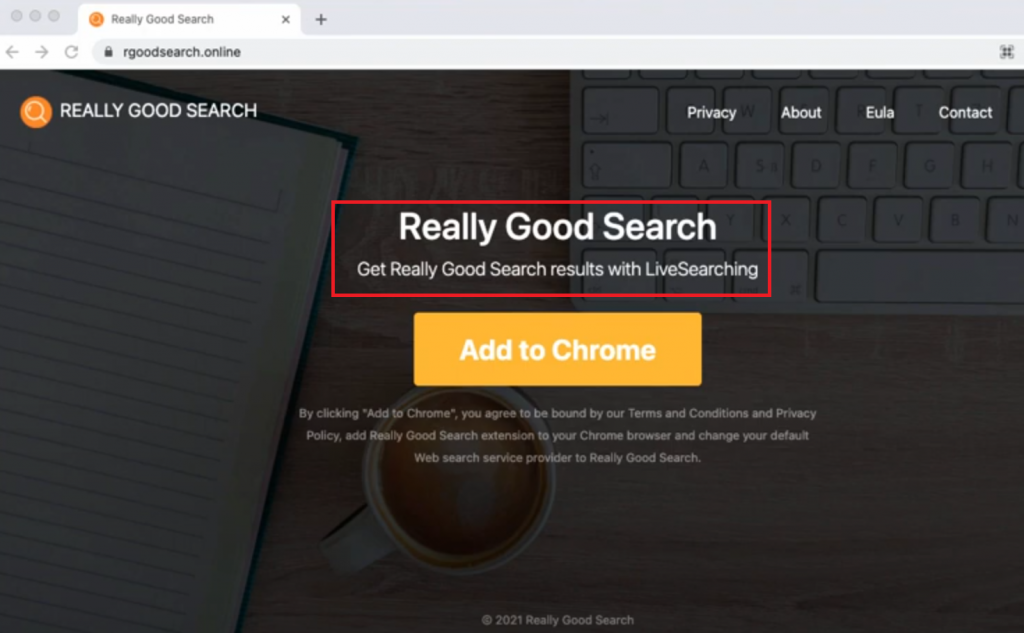
Really Good Search
If you have come across a program called Really Good Search on your computer, you have been infected with a browser hijacker. Hijackers like Really Good Search aren’t generally seen as harmful, but there are a number of reasons why it’s a good idea to remove them.
Browsers have always been a target for all kinds of cyber criminal schemes, which is why a vulnerable browser means you are more likely to get your computer infected with Trojans, viruses, spyware, ransomware and all other sorts of dangerous programs. Modern browsers tend to have high levels of security, but there are certain apps on the Internet that function similarly to browser extensions, and which, if installed in your browser, may make it less safe and more prone to malware attacks.
One such type of undesirable browser-related applications are the infamous page-redirecting browser hijackers. Such applications are Wave browser, Omnatuor, Best Clever Captcha and many more. These are small software elements that are able to add themselves to your browser without any initial symptoms and make certain changes to it. Today, we will tell you about a hijacker element that has been reported to change the browser’s homepage and to replace its default search engine.
Firefox, Chrome, Opera, Safari, Edge, and pretty much all other popular browsers are all susceptible to the effects of this annoyance. The browser hijacker responsible for these changes, Really Good Search, is not a virus, a Ransomware infection or some kind of Trojan. And because of that, your security program or the built-in safety tools of the browser may not be able to recognize the hijacker as unwanted and to prevent it from getting installed. Another thing worth mentioning here is that hijackers such as Really Good Search have their sneaky methods of gaining the user’s permission to get installed inside the browser, without the user actually realizing that they have given their permission.
A very popular method that allows this to happen is the file-bundling technique. This is actually a very common way of spreading different types of software. You have more than likely noticed that many of the programs that you have installed on your computer have had some additional components put inside their installers. In most cases, those components are unneeded at the worst, but are not invasive. However, if a hijacker is included in the installer of some program and you go for the Quick/ Default installation of that program, you will more than certainly get the hijacker as well. And that is when the page redirects, the changes in the browser and the display of ads would commence.
The irritation induced by all the activities of the hijacker, however, are nothing in comparison to the hazards to which your system may get exposed to if you keep the invasive app for too long in your browser. We already mentioned that the hijackers are not inherently harmful or malicious but their unwelcome changes in the browser and their sudden page-redirects may easily land you on some shady web page full of malware.
To help you remove the Really Good Search page from your browser and to bring back your preferred search engine, we have prepared a guide that will help you uninstall Really Good Search, the browser hijacker, and will allow you to restore the normal state of your browser. All the instructions that you may need are available down below.
SUMMARY:
| Name | Really Good Search |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Detection Tool |
*Source of claim SH can remove it.
Remove Really Good Search Malware
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab (the “Details” Tab on Win 8 and 10). Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold together the Start Key and R. Type appwiz.cpl –> OK.

You are now in the Control Panel. Look for suspicious entries. Uninstall it/them.
Type msconfig in the search field and hit enter. A window will pop-up:

Startup —> Uncheck entries that have “Unknown” as Manufacturer or otherwise look suspicious.

*Source of claim SH can remove it.
Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Open the start menu and search for Network Connections (On Windows 10 you just write it after clicking the Windows button), press enter.
- Right-click on the Network Adapter you are using —> Properties —> Internet Protocol Version 4 (ICP/IP), click Properties.
- The DNS line should be set to Obtain DNS server automatically. If it is not, set it yourself.
- Click on Advanced —> the DNS tab. Remove everything here (if there is something) —> OK.


- After you complete this step, the threat will be gone from your browsers. Finish the next step as well or it may reappear on a system reboot.
Right click on the browser’s shortcut —> Properties.
NOTE: We are showing Google Chrome, but you can do this for Firefox and IE (or Edge).

Properties —–> Shortcut. In Target, remove everything after .exe.

![]() Remove Really Good Search from Internet Explorer:
Remove Really Good Search from Internet Explorer:
Open IE, click ![]() —–> Manage Add-ons.
—–> Manage Add-ons.
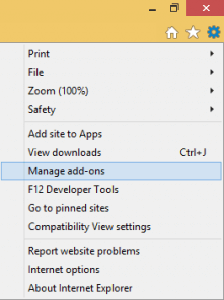
Find the threat —> Disable. Go to ![]() —–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
—–> Internet Options —> change the URL to whatever you use (if hijacked) —> Apply.
![]() Remove Really Good Search from Firefox:
Remove Really Good Search from Firefox:
Open Firefox, click ![]() ——-> Add-ons —-> Extensions.
——-> Add-ons —-> Extensions.

![]() Remove Really Good Search from Chrome:
Remove Really Good Search from Chrome:
Close Chrome. Navigate to:
C:/Users/!!!!USER NAME!!!!/AppData/Local/Google/Chrome/User Data. There is a Folder called “Default” inside:
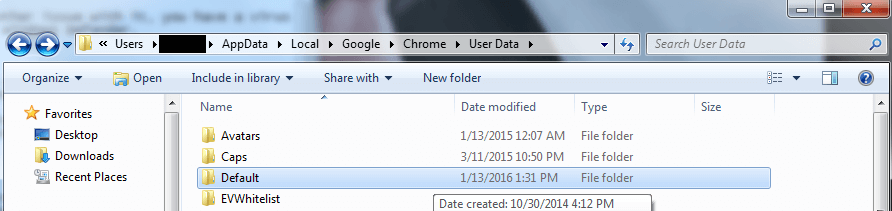
Rename it to Backup Default. Restart Chrome.

Type Regedit in the windows search field and press Enter.
Inside, press CTRL and F together and type the threat’s Name. Right click and delete any entries you find with a similar name. If they don’t show up this way, go manually to these directories and delete/uninstall them:
- HKEY_CURRENT_USER—-Software—–Random Directory. It could be any one of them – ask us if you can’t discern which ones are malicious.
HKEY_CURRENT_USER—-Software—Microsoft—-Windows—CurrentVersion—Run– Random
HKEY_CURRENT_USER—-Software—Microsoft—Internet Explorer—-Main—- Random
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment