*Source of claim SH can remove it.
Redeemer
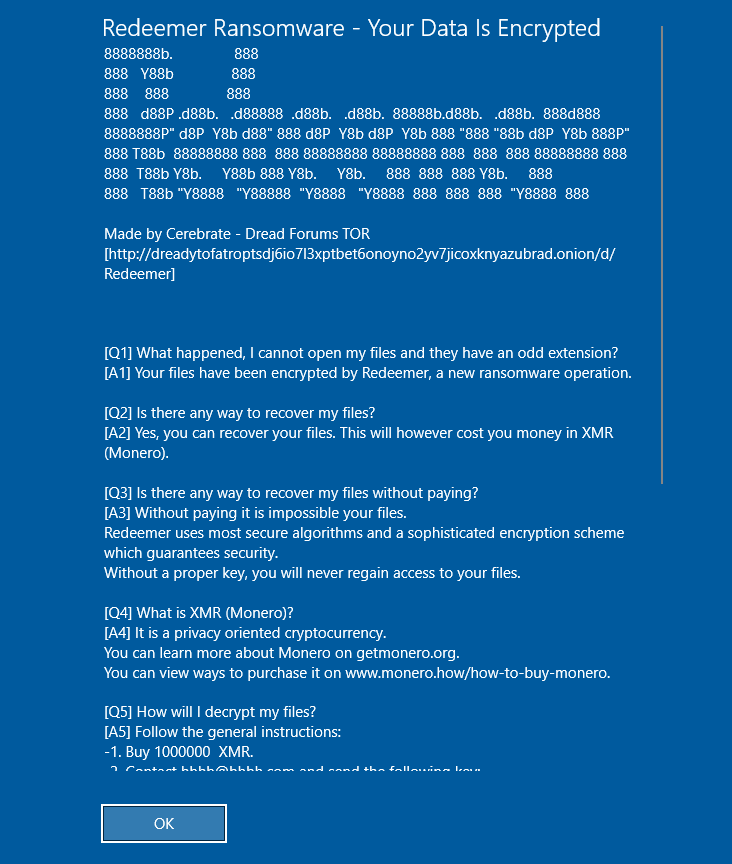
Redeemer is a ransomware virus created to restrict access to important user files through encryption. The ultimate goal of Redeemer is to extort money from its victims by blackmailing them to pay a ransom for a file decryption key.
Being infected with a ransomware like Redeemer could be one of the most horrific experiences. You may not only be prevented from access to the information stored on your computer, but there is no guarantee that you will ever be able to recover it again. This alone can be quite stressful and discouraging but, in this post, we’ve decided to provide the victims of Redeemer with some alternatives that could help them remove the infection and potentially recover some of their files. Below is a thorough removal guide with all the instructions and a removal tool for professional assistance.
The Redeemer virus
The Redeemer virus is a file-encrypting ransomware infection that prevents users from accessing a rather large portion of their data on the compromised device. In this way, the Redeemer virus attempts to get them to pay the hackers behind the virus a ransom for a decryption key.

To extort money from the victims, the criminals use a variety of tactics like setting a short deadline to transfer the required money, doubling the ransom amount or threatening to permanently delete the decryption key which can recover the encrypted information.
Sadly, ransomware infections such as Redeemer, Dapo, Craa represent a terrible threat to any computer with data stored on it. There are several reasons for that and one of them is the way these viruses operate. Typically, those threats can automatically search your entire system and compile a list of specific file types as soon as they reach your device. The target files may include digital documents, images, video or audio files, presentations or executables which get encrypted with a complex code one by one and become inaccessible without a decryption key.
The .Redeem file encryption
The Redeemer file encryption is a process that the Redeemer ransomware carries out in the background of the infected system. The purpose of the Redeemer file encryption is to render a list of specific file types inaccessible so that the hackers behind the ransomware can place their ransom demands.
In this context, it is obviously not the best idea to send money to the blackmailers. Not only does it give them just what they want and allow them to harass people, but also it may not ensure the recovery of the encrypted files. In fact, the hackers may simply choose not to give the decryption key they had originally promised and vanish with the money or keep blackmailing the victims for another payment. And, sadly, you won’t be able to do anything about it. Therefore, our suggestion is to take the initiative in your hands and try to handle the Redeemer infection on your own. For this, we have created a special removal guide below which contains steps on how to remove the ransomware and restore some of your data from system backups. We suggest that you carefully read the instructions and give a try to the free file-recovery steps to see if they can help you minimize the data loss to some extent. We also strongly recommend that you regularly back up your most important files and keep copies of them on a separate drive in order to be fully protected from ransomware attacks in the future.
SUMMARY:
| Name | Redeemer |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Data Recovery Tool | Not Available |
| Detection Tool |
*Source of claim SH can remove it.
Remove Redeemer Ransomware Virus

Some of the steps will likely require you to exit the page. Bookmark it for later reference.
Reboot in Safe Mode (use this guide if you don’t know how to do it).

WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Source of claim SH can remove it.
Press CTRL + SHIFT + ESC at the same time and go to the Processes Tab. Try to determine which processes are dangerous.

Right click on each of them and select Open File Location. Then scan the files with our free online virus scanner:

After you open their folder, end the processes that are infected, then delete their folders.
Note: If you are sure something is part of the infection – delete it, even if the scanner doesn’t flag it. No anti-virus program can detect all infections.

Hold the Start Key and R – copy + paste the following and click OK:
notepad %windir%/system32/Drivers/etc/hosts
A new file will open. If you are hacked, there will be a bunch of other IPs connected to you at the bottom. Look at the image below:

If there are suspicious IPs below “Localhost” – write to us in the comments.
Type msconfig in the search field and hit enter. A window will pop-up:

Go in Startup —> Uncheck entries that have “Unknown” as Manufacturer.
- Please note that ransomware may even include a fake Manufacturer name to its process. Make sure you check out every process here is legitimate.

Type Regedit in the windows search field and press Enter. Once inside, press CTRL and F together and type the virus’s Name.
Search for the ransomware in your registries and delete the entries. Be extremely careful – you can damage your system if you delete entries not related to the ransomware.
Type each of the following in the Windows Search Field:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Delete everything in Temp. The rest just check out for anything recently added. Remember to leave us a comment if you run into any trouble!

How to Decrypt Redeemer files
We have a comprehensive (and daily updated) guide on how to decrypt your files. Check it out here.
If the guide doesn’t help, download the anti-virus program we recommended or try our free online virus scanner. Also, you can always ask us in the comments for help!

Leave a Comment