Remor.xyz
The digital realm is rife with cyber threats, and among the most troublesome are browser hijackers. Remor.xyz is a representative example of this category, seamlessly altering a user’s Internet browser settings without their knowledge. This typically manifests as changes to the homepage or default search mechanisms. However, what makes Remor.xyz more insidious is its ability to inject unwanted advertisements into one’s browsing experience. These intrusive ads don’t just clutter one’s screen; they can also redirect the unsuspecting user to potentially malicious web destinations, heightening the danger of encountering harmful content or malware. Some hijackers like this one might come equipped with keyloggers, designed to stealthily record a user’s keystrokes. Such covert operations can lead to the extraction of valuable information, such as personal account details, making it paramount to stay alert and informed.
Is Remor.xyz safe?
Remor.xyz Virus
This malware is often mistakenly referred to as “the Remor.xyz virus,” but it’s essential to understand the distinction between browser hijackers and computer viruses. Both are categories of malware, but they operate differently. A computer virus is a type of malware that self-replicates, inserting its malicious code into other files or programs. Its primary intent is to spread and potentially damage a computer’s operations. On the other hand, a browser hijacker like the Remor.xyz virus specifically targets web browsers to redirect users to unintended websites, often for financial gain through ads or phishing attempts. The term “browser redirect virus” is a misnomer; it’s more accurate to describe it as a browser hijacker, emphasizing its focus on manipulating browser activity rather than self-replicating and spreading like traditional viruses.
What is Remor.xyz?
A browser hijacker, like Remor.xyz, is a specific type of malicious software (malware) that alters a web browser’s settings without the user’s consent. Often disguised as harmless browser add-ons or extensions, they can lead users to undesired or even harmful websites. But, what exactly is a browser hijacker? Essentially, it’s sometimes referred to as a browser redirect virus. There are two core motives behind these hijackers: First, they aim to generate ad revenue by redirecting users to pages filled with ads. This redirection boosts the ad views and, consequently, the ad income for the entities managing these sites. Second, they might harbor more nefarious intentions, like collecting sensitive data. By deploying spyware, hijackers like Remor.xyz, Secuweb.co.in and Chromstera can monitor your online activities, paving the way for potential cyberattacks or the sale of your data to malicious third parties.
Remor.xyz Pop up
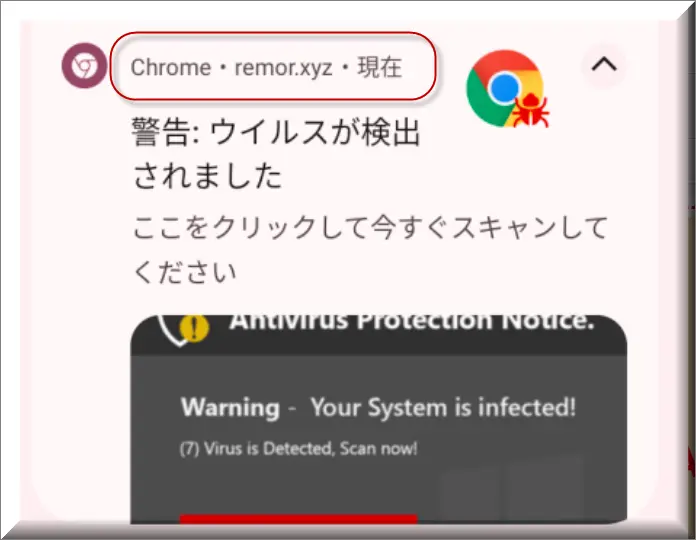
Remor.xyz is an infamous browser hijacker, frequently invading systems in a way similar to annoying pop-ups. The fascinating aspect is the close relationship between the operations of browser hijackers like this one and those of pop-ups. Their chief similarity lies in their subtle infiltration techniques. A considerable number of browser hijackers, embed themselves as toolbars, typically bundled with free software from third-party websites. Furthermore, both these digital irritants can worm their way into systems via embedded code found in the websites users frequent. The Remor.xyz pop up is a classic illustration, popping up unexpectedly as unsolicited ad windows or discreetly as part of hidden malware payloads. In rare instances, the Remor.xyz pop up might even disguise itself as a seemingly legitimate program. It’s vital for users to understand these overlaps between hijackers and pop-ups to protect their online activities and maintain optimal cybersecurity.
Remor.xyz on Chrome
One of the primary signs that Remor.xyz on Chrome has compromised your system is an evident change in your default search engine. This alteration often redirects you to sites filled with ads or even potentially malicious webpages. Another concerning symptom of Remor.xyz on Chrome is the notable slowdown in load times and a surprising decrease in storage space. This is due to the hijacker consuming device resources and storage. It’s not just about inconvenience; these redirects can spiral users into hazardous domains, exposing them to adware, spyware, and other browser hijacking entities. To restore browser speed and safety, it’s essential to remove such hijackers and consider opting for more secure web browsers.
Remor
Remor.xyz is a prominent example of a browser hijacker that disrupts the user experience on internet browsers. As the primary gateway to the internet, browsers are essential tools we use to access and interact with information online. The intrusion of Remor.xyz into this space is reminiscent of the increasing number of companies and entities that embed small programs into browsers without user consent. These entities behind such hijacking can vary, spanning from established software manufacturers to individual hackers or even a combination. As a result, unwary users find their browsing activities modified or redirected, often leading to a compromised user experience. It’s crucial for users to be vigilant and safeguard their browsers from threats like this one.
SUMMARY:
| Name | Remor.xyz |
| Type | Browser Hijacker |
| Detection Tool |
Some threats reinstall themselves if you don’t delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don’t harm your system by deleting the wrong files. |
Remove Remor.xyz
To try and remove Remor.xyz quickly you can try this:
- Go to your browser’s settings and select More Tools (or Add-ons, depending on your browser).
- Then click on the Extensions tab.
- Look for the Remor.xyz extension (as well as any other unfamiliar ones).
- Remove Remor.xyz by clicking on the Trash Bin icon next to its name.
- Confirm and get rid of Remor.xyz and any other suspicious items.
If this does not work as described please follow our more detailed Remor.xyz removal guide below.
If you have a Windows virus, continue with the guide below.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Some of the steps may require you to exit the page. Bookmark it for later reference.
Next, Reboot in Safe Mode (use this guide if you don’t know how to do it).
 Uninstall the Remor.xyz app and kill its processes
Uninstall the Remor.xyz app and kill its processes
The first thing you must try to do is look for any sketchy installs on your computer and uninstall anything you think may come from Remor.xyz. After that, you’ll also need to get rid of any processes that may be related to the unwanted app by searching for them in the Task Manager.
Note that sometimes an app, especially a rogue one, may ask you to install something else or keep some of its data (such as settings files) on your PC – never agree to that when trying to delete a potentially rogue software. You need to make sure that everything is removed from your PC to get rid of the malware. Also, if you aren’t allowed to go through with the uninstallation, proceed with the guide, and try again after you’ve completed everything else.
- Uninstalling the rogue app
- Killing any rogue processes
Type Apps & Features in the Start Menu, open the first result, sort the list of apps by date, and look for suspicious recently installed entries.
Click on anything you think could be linked to Remor.xyz, then select uninstall, and follow the prompts to delete the app.

Press Ctrl + Shift + Esc, click More Details (if it’s not already clicked), and look for suspicious entries that may be linked to Remor.xyz.
If you come across a questionable process, right-click it, click Open File Location, scan the files with the free online malware scanner shown below, and then delete anything that gets flagged as a threat.


After that, if the rogue process is still visible in the Task Manager, right-click it again and select End Process.
 Undo Remor.xyz changes made to different system settings
Undo Remor.xyz changes made to different system settings
It’s possible that Remor.xyz has affected various parts of your system, making changes to their settings. This can enable the malware to stay on the computer or automatically reinstall itself after you’ve seemingly deleted it. Therefore, you need to check the following elements by going to the Start Menu, searching for them, and pressing Enter to open them and to see if anything has been changed there without your approval. Then you must undo any unwanted changes made to these settings in the way shown below:
- DNS
- Hosts
- Startup
- Task
Scheduler - Services
- Registry
Type in Start Menu: View network connections
Right-click on your primary network, go to Properties, and do this:

Type in Start Menu: C:\Windows\System32\drivers\etc\hosts

Type in the Start Menu: Startup apps

Type in the Start Menu: Task Scheduler

Type in the Start Menu: Services

Type in the Start Menu: Registry Editor
Press Ctrl + F to open the search window

 Remove Remor.xyz from your browsers
Remove Remor.xyz from your browsers
- Delete Remor.xyz from Chrome
- Delete Remor.xyz from Firefox
- Delete Remor.xyz from Edge
- Go to the Chrome menu > More tools > Extensions, and toggle off and Remove any unwanted extensions.
- Next, in the Chrome Menu, go to Settings > Privacy and security > Clear browsing data > Advanced. Tick everything except Passwords and click OK.
- Go to Privacy & Security > Site Settings > Notifications and delete any suspicious sites that are allowed to send you notifications. Do the same in Site Settings > Pop-ups and redirects.
- Go to Appearance and if there’s a suspicious URL in the Custom web address field, delete it.
- Firefox menu, go to Add-ons and themes > Extensions, toggle off any questionable extensions, click their three-dots menu, and click Remove.
- Open Settings from the Firefox menu, go to Privacy & Security > Clear Data, and click Clear.
- Scroll down to Permissions, click Settings on each permission, and delete from it any questionable sites.
- Go to the Home tab, see if there’s a suspicious URL in the Homepage and new windows field, and delete it.
- Open the browser menu, go to Extensions, click Manage Extensions, and Disable and Remove any rogue items.
- From the browser menu, click Settings > Privacy, searches, and services > Choose what to clear, check all boxes except Passwords, and click Clear now.
- Go to the Cookies and site permissions tab, check each type of permission for permitted rogue sites, and delete them.
- Open the Start, home, and new tabs section, and if there’s a rogue URL under Home button, delete it.

Leave a Reply