*Source of claim SH can remove it.
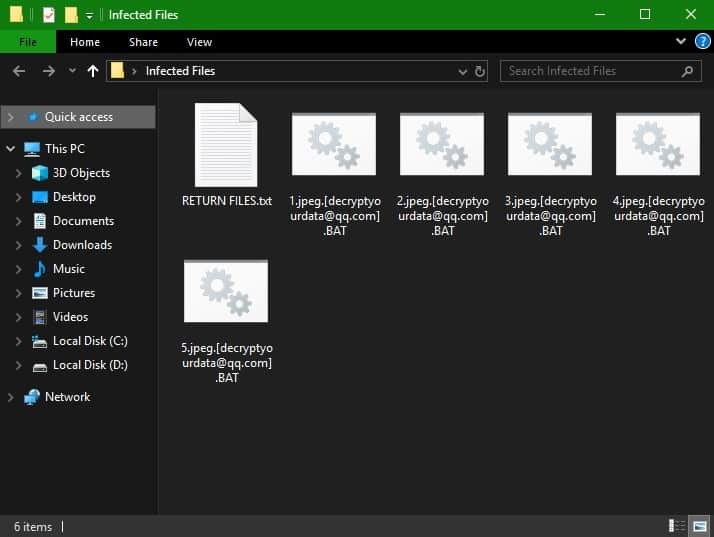
.Bat
This page aims to help you remove .BAT Ransomware Virus for free. Our instructions also cover how any .BAT file can be recovered.
After the virus is done infecting your system, it leaves a Pop up window with the following ransom message:
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL [email protected]
IN THE LETTER WRITE YOUR ID, YOUR ID ****
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL:[email protected]
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
A few seconds after the encryption, it drops a RETURN FILES.txt file with instructions:
All your data is encrypted!
for return write to mail:
[email protected]
Ransomware is a well-known and infamous form of computer infections and many security experts have been trying to find more effective ways of dealing with these threats for years on end. Unfortunately, there are still no universal techniques, tools or methods that could help one deal with all the consequences of each Ransomware representative. This is especially true when talking about the cryptovirus subcategory of Ransomware – those are probably the nastiest forms of Ransomware as the file-encryption they use is oftentimes unbreakable meaning that you have very limited options of counteraction once such a virus invades your computer. The reason why dealing with a Ransomware cryptovirus representative could be such a challenge lies in the file-encryption that it uses. Most different cryptovirus versions use different encryption algorithms meaning that even if there’s a tool to decrypt the files locked by one specific cryptovirus, this tool will likely not work against another such infection. And, needless to say, this is what the hackers are counting on, as their main goal is to blackmail their victims for the access to the encrypted data files and documents. If you are a victim of a cryptovirus and have no important or valuable files in your machine or if you have extensive backups, such a malware attack wouldn’t be such an issue as all you’d need to do is remove the virus (which is the easier part). However, practice shows that most users aren’t like that – most people do indeed have valuable data stored in their computer without having a proper backup location for their important files. This is precisely what makes the Ransomware threats so devastating and one of their most recent representatives is the insidious .BAT.
.BAT is, in fact, likely the malware that led you to seek our help. If you are one of its many victims and currently have no way of opening any of your files, you should know that there is a guide below that may help you minimize the harm that this infection has caused. Of course, you can always opt for the payment of the ransom instead, but you should first ask yourself whether it is actually a good idea to trust the hackers behind .BAT and hope that they will release your files once you send them the money.
Why paying the ransom may lead to more trouble
There is literally nothing stopping the hackers from retaining the unique decryption key for your data even after you release the payment they require. Needless to say, should this happen, it would only make the matters worse. This is exactly why we advise against going directly for the payment before at least exploring the other potential options you may have. And though we can’t promise that the guide offered below will allow you to unlock all (or any) of your files, it should still be enough to, at the very least, remove .BAT and in this way make your system safe for use in the future.
SUMMARY:
| Name | .BAT |
| Type | Ransomware |
| Detection Tool |
*Source of claim SH can remove it.
Remove .BAT Ransomware Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

How do you recover files affected by berost?
Como se recupera luego los archivos afectados por berost??