This page aims to help you remove .Berost Virus Ransomware for free. Our instructions also cover how any .Berost file can be recovered.
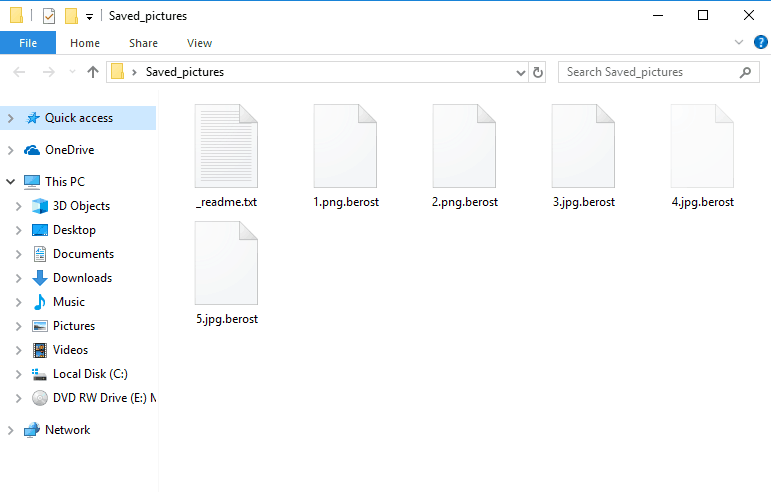
These are the infected files by a new strain of the STOP Ransomware, modifying the extension with .Berost
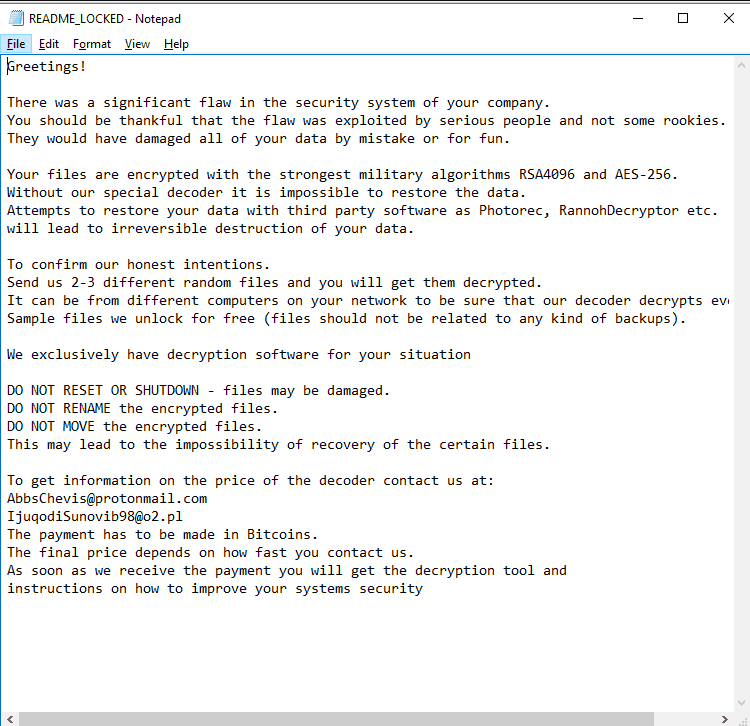
Digital data is one of the most valuable resources nowadays and, naturally, it is also one of the most common targets for computer hackers. One of the most infamous examples of a mass threat that targets the files inside the users’ computers are the representatives of the Ransomware cryptovirus category, with one of their latest representatives being the malicious .Berost. Unlike other malicious types of software, a typical cryptovirus wouldn’t really try to damage the computer’s system itself, nor would it seek to spy on the user or acquire some sensitive personal information and then threaten to make it public. Instead, what a Ransomware cryptovirus does is it locks up all user files found on the computer using a complex data encryption process for the purpose. The infections .Berost, .Sarut, .Dutan, .Roldat, sneaks silently into the machine that it has targeted and the next thing the user knows is that their files can no longer be opened through any regular means. In fact, the thing that’s supposed to be the only way of accessing encrypted data is a corresponding decryption key. Such a key, of course, wouldn’t initially be available to the victims of a Ransomware cryptovirus and would actually be offered to them at a certain price in the form of a ransom payment. The money that the hackers request are typically demanded in the BitCoin currency or in some other similar cryptocurrency. The idea is that this would make the transaction more difficult to trace and would, in turn, allow the blackmailers to remain anonymous and avoid being brought to justice. In other words, this means that once you pay them the money, that money is gone and could never be refunded even in case you don’t’ actually get the key for your locked-up files. Speaking of getting the key, the fact that you’ve paid doesn’t guarantee anything with regards to the recovery of your files. This isn’t a legitimate purchase and regardless of whether you pay or not, there’s still a chance that you may not get to decrypt your files. That’s why, we believe that other options need to be explored in such situations – options that do not involve your risking sizeable amounts of money by offering them to a group of anonymous hackers.
Our suggestion for dealing with .Berost and other similar infections
One of the first things you need to consider after finding out that .Berost or some other cryptovirus has entered your computer is finding a way to eliminate the infection so as to make your computer safe once more. We can assist you with this – the guide that you will see below has instructions and a suggested anti-malware software tool that can help you eliminate .Berost.
However, in order to recover your files, you will need to take extra steps. If you have any backup copies, great – now’s the time to use them. For any files that aren’t backed-up, we suggest you try the alternative recovery options added to the guide file-restoration section of the guide. We can’t promise that they’ll work but we encourage you to try them as they are still preferable compared to the ransom payment.
SUMMARY:
| Name | .Berost |
| Type | Ransomware |
| Detection Tool |
Remove .Berost File Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.




There is this file in AppData named “ZSDLVoc”.
And I can not delete it. I think its a malware. How can I get rid of it?
What happens when you try to delete it?