This page aims to help you remove .Dutan Virus Ransomware for free. Our instructions also cover how any .Dutan file can be recovered.
Hopefully, by now the majority of PC users have learned about just how important it is to make backups of their important files, especially considering how easy it is to do it and how many free and easily accessible backup options there are. However, the truth is that most computer users still widely disregard the importance of doing this simple activity and that is the main reason why malware threats like .Dutan are currently thriving.
.Dutan is a Ransomware cryptovirus and the latest successor of the strain that includes .Hofos, .Todarius and .Roldat. For those of you unaware of what this means, we must tell you that this is a particularly nasty form of malware that targets the files stored inside the attacked computer with the goal of encrypting them. The encryption that this malicious program places on the targeted data doesn’t actually cause damage to the files. Instead, it simply renders them inaccessible so that nobody who uses the infected computer could do anything with them. Opening, using or modifying any of the encrypted files becomes impossible if you do not have the unique decryption key that corresponds to the encryption used on the them. Needless to say, this key is initially only available to the dishonest people who are responsible for the creation and the distribution of the nefarious cryptovirus. This decryption key is, in fact, the central object of the blackmailing which is to follow soon after the files targeted by the Ransomware have gotten encrypted. That’s right, once .Dutan makes it impossible for you to access any of your personal data on the infected computer, it tells you that you can pay for the decryption key, which would be sent to you as soon as you transfer the money the hackers demand of you.
The .Dutan ransomware could also infect your computer by having the infection files uploaded on suspicious sites. The infection files could pretend to be cracks, patches and other forms of activators.
Once such ransomware has infected your computer, the virus may immediately drop the malicious files in the following directories:
%AppData%
%Local%
%LocalLow%
%Roaming%
%Temp%
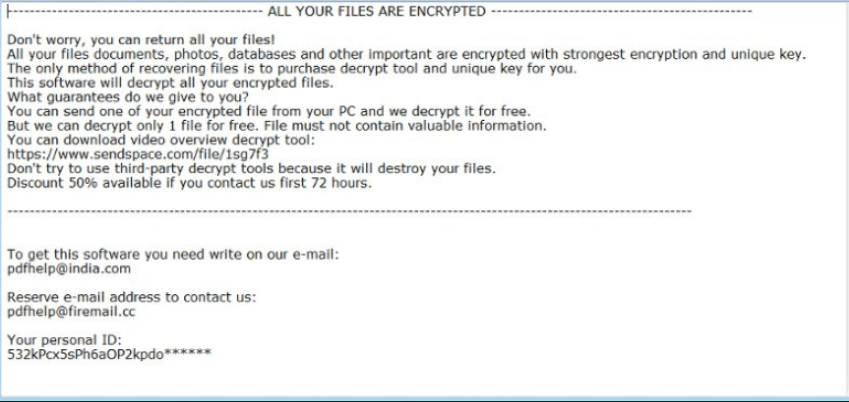
The ransomware drops a RESTORE_DUTAN_DATA.txt ransom note file, whose main goal is to notify the sufferer and get him or her to visit the ransom payment page.
It should go without saying that there are a number of reasons why it is much better if you could find an alternative way of retrieving your files, instead of paying the ransom. First and foremost, the sum that is required by the hackers may be quite sizeable and you may not be able to pay it immediately. Also, even if you do make the payment, things may still not turn out the way you hoped they would as the hackers may still refuse to give you the access key for the sealed data. In this case, not only would you still be unable to open the locked files, but also you would have lost a substantial amount of money in the process. The third reason paying is not ideal has to do with the fact that this would surely further encourage the hackers behind .Dutan to keep on blackmailing more and more people in the future.
The alternative approach
Regardless of whether you have any backups of your files or not, you should still make sure the nasty cryptovirus gets removed from your computer and we can help you with that in our .Dutan removal guide below. As far as the recovery of your files is concerned, there are sadly no guarantees about whether or not it would be successful. However, there may still be some viable alternative data recovery options that do not involve the paying of a ransom. Some of them, you can find in the file restoration section of the guide.
SUMMARY:
| Name | .Dutan |
| Type | Ransomware |
| Detection Tool |
Remove .Dutan
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

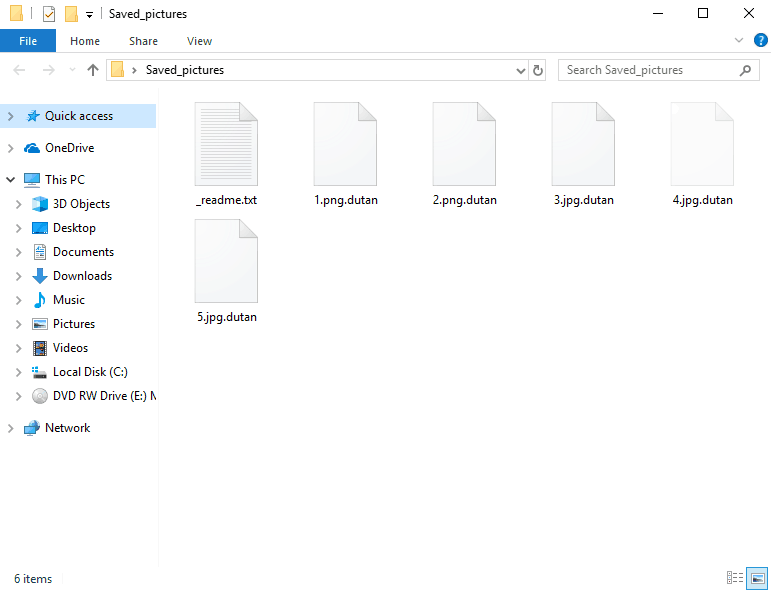
My system is infected by .Dutan malware and i am not able use any of the files , please help me i a college student and i have my project going please please help me, iam not getting to know how to get my files. All my files are having their extention changed to .Dutan.
please provide me help and guide me in correct way…
There is a guide on this page that you are advised to complete.
i have done 3rd step and got this hosts please check
www. sblinfo. pw
127.0.0.1 www .sjjscenter. pw
127.0.0.1 www. eodeysua. com
127.0.0.1 eodeysua. com
127.0.0.1 sjjscenter. pw
127.0.0.1 sblinfo. pw
127.0.0.1 www. redaceivete. pw
127.0.0.1 redaceivete. pw
Those IPs must definitely be removed from your Hosts file.
Hi John. I sow that your system was also infected with Dutan virus and you did method of this page. Was it helpful? Were you able to get your files back and delete virus? I want to do it on my previous PC so I ask you about it.