Chainthorn.com
The Chainthorn.com virus typically seeks to modify the options of your browser without your direct permission with the idea to display different sponsored ads, banners, pop-up messages and commercials and to redirect you to some third-party websites that promote some products and services. The changes that the Chainthorn.com virus may apply may vary, but one of the results is always the same: you get exposed to more advertising materials than normal every time you start a new browsing session.
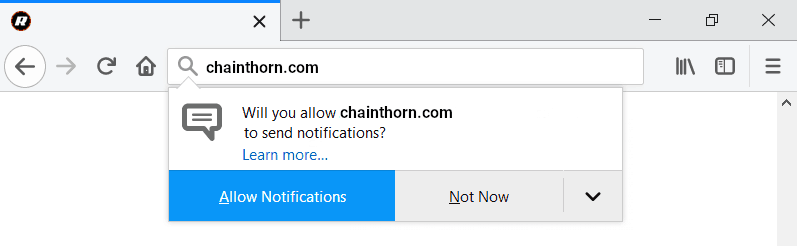
The Chainthorn.com “Virus” will display Pop-up windows asking for permission for its Push notifications.
Have you ever experienced the following situation: you download a program that you need from some supposedly reliable website, you download the installer and click on “Accept” without further exploring the installation options? But when you finish the installation process and you return to the browser (be it Chrome, Firefox, Explorer, or another one), you realize that one or several third-party toolbars have appeared there or that the default homepage or the search engine have been changed and are now pate-redirecting you to some unknown sites. If the answer is yes, then the chances are you have accidentally installed a Browser Hijacker such as Chainthorn.com, Go.mail.ru or Cloudnet on your Chrome, Safari, Firefox, etc. What has happened to you is something very common and a lot of web users seem to face the same issue when they carelessly install some new software on their machine via the automatic setup. They get their browser’s settings changed and in addition to that, some of them experience an aggressive stream of different ads, banners, pop-ups and sponsored redirects on their screen. But why those changes take place and how to remove them? Are they caused by some malicious program (such as a Trojans, a Ransomware, or a Spyware), and can they expose your system to viruses? This is exactly what we are going to talk about here. If you have Chainthorn.com on your system, in the next lines, we will explain to you how to uninstall all of its changes and potentially unwanted components as well as how to permanently remove the nagging ads, associated with it.
Fortunately, Chainthorn.com is not a serious computer threat but a rather harmless representative of the Browser Hijacker family. Therefore, you have a great chance of successfully dealing with it effectively if you carefully follow the instructions at the end of the article or use the suggested Chainthorn.com “Virus” removal tool below.
How can you remove the changes and uninstall the Browser Hijacker?
If your web browser has been taken over by ads generated by Chainthorn.com “Virus”, it is a good idea to get rid of the cause of those ads before the sponsored pop-ups become a major browsing issue. Another good reason to uninstall it is that you can never be sure where the browser hijacker redirect may you to – there are pages with unreliable content where viruses and nasty malware, including Ransomware and Trojans can be found and the best way to avoid them is to avoid automatic page-redirects to unfamiliar web locations. In order to do that, simply follow the steps that you will find in the removal guide below and restore the default settings of your browser.
SUMMARY:
| Name | Chainthorn.com |
| Type | Browser Hijacker |
| Detection Tool |
Remove Chainthorn.com “Virus”
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment