This page aims to help you remove the ChaosCC Hacker Group Email. Our removal instructions work for every version of Windows.
The ChaosCC Hacker
The ChaosCC hacker group is a bogus scam taking advantage of recent leaks to scare users into believing they are infected by malware. The ChaosCC hacker actually doesn’t exist – it is simply a name devised to make you think you are dealing with something far more sophisticated than the truth.
Email from ChaosCC Hacker Group
Damage to your system and data is only one of the many issues you may come to face if a Trojan like ChaosCC Hacker Group attacks your computer, and it is also one of the lesser issues related to such an infection. The Trojans are sneaky tools used in various forms of online crime, and since they typically seek to gain full Administrative privileges in the machines that they attack, there is very little that they cannot do if they successfully infiltrate a given computer. One other unpleasant thing about these threats is how secretive and covert they could at times be. Sure, in many cases, BSOD crashes and errors in the system would likely give away the attack, but in other instances, the malware may operate in absolute silence, showing no symptoms or signs that may warn you about its presence.
Chaoscc Hacker Group Email
The ChaosCC Hacker Group is an email scam. The main reason behind it is to extort money from the affected users in the form of Bitcoin payments. The scammers behind the ChaosCC Hacker Group Email threaten to release a compromising video of the targeted users unless a bitcoin payment’s not completed within 60 hours. This is just an email scam though and not to be believed.
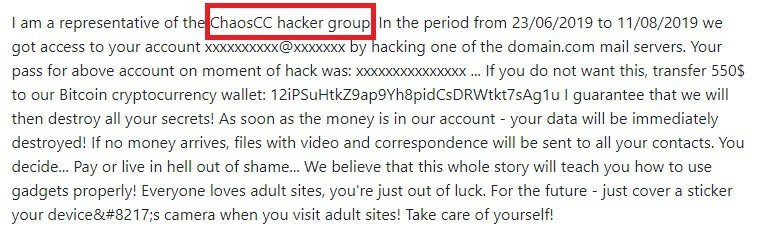
An example of such an email reads the following:
Hello! I am a representative of the ChaosCC hacker group. In the period from …../2019 to …../2019 we got access to your account [email protected] by hacking one of the domain.com mail servers. You decide… Pay or live in hell out of shame… We believe that this whole story will teach you how to use gadgets properly! Everyone loves adult sites, you’re just out of luck. For the future – just cover a sticker your device;s camera when you visit adult sites! Take care of yourself! … 550$.
If you have recently had your machine infected by the ChaosCC Hacker Group Email, and you know it, then you may consider yourself lucky – at least you’ve been able to spot the threat and can now begin the process of removing it. It is essential that you do everything in your power to rid your system of this Trojan because, if the infection is allowed to stay in the machine for a longer period of time, it may carry out all sorts of sketchy activities that may not only damage your computer, but put your privacy and in jeopardy.
Some of the things you can expect from a Trojan Horse attack
If a the Trojan gains Admin rights in your computer, this means that it can then allow the criminal controlling it to do nearly everything in the system that you, yourself, can do. In many cases, some more aggressive Trojans may even fully take over the system and revoke your access to many settings and options you have previously had in your computer. What happens next depends on what the goal of the people behind the Trojan is. They may be after your banking details, in which case the virus is likely to operate without showing symptoms so that it can covertly acquire those details through keylogging and/or screen-capture. In other cases, the hackers may simply want to use your machine as yet another addition to the Trojan’s botnet, and force it to mine cryptocurrency for them or to participate in Denial of Service attacks or in mass spam message campaigns. In those cases, the malware may not be so secretive as you would inevitably notice the decrease in your computer’s speed and productivity, and you may even experience crashes, errors, and full or partial unresponsiveness. In such cases, it may be particularly difficult to do anything in the computer if it is connected to the Internet, which is why you may want to disconnect it if any of those symptoms are present and then come back to this page via another device in order to use the guide we are about to give you. Speaking of the guide, it is right below and if you follow its steps and/or use the professional removal tool added in it, you should be able to save your computer and rid it of the insidious ChaosCC Hacker Group infection.
SUMMARY:
| Name | ChaosCC Hacker Group |
| Type | Trojan |
| Detection Tool |
Remove ChaosCC Hacker Group Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment