*Source of claim SH can remove it.
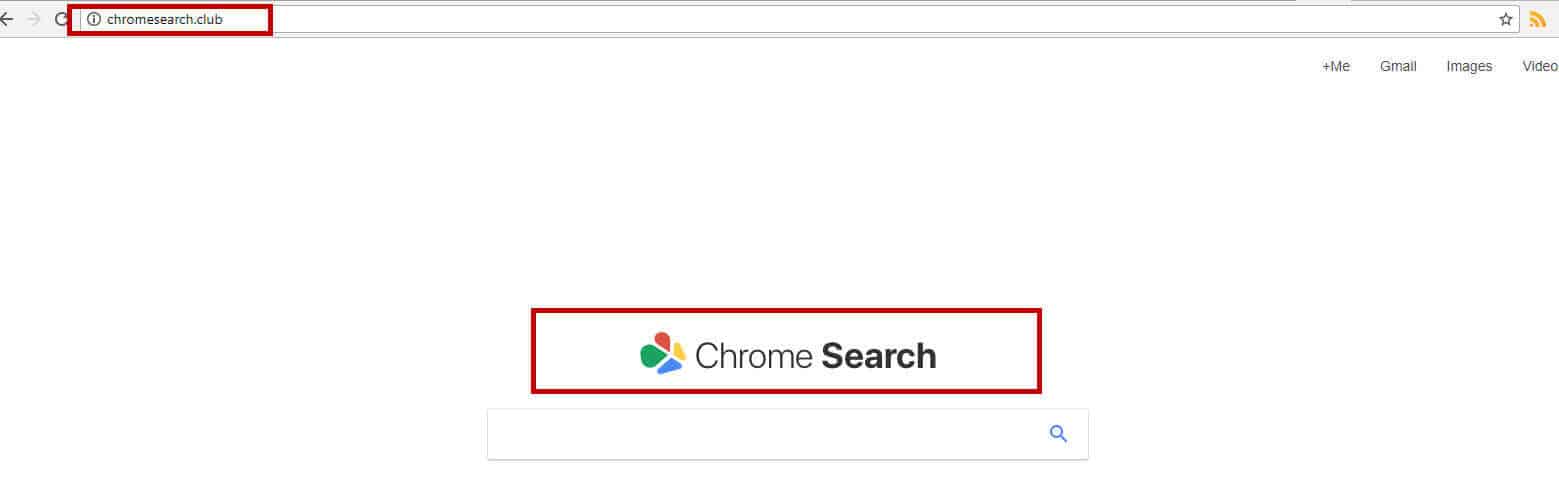
Chromesearch.club
This page aims to help you remove Chromesearch.club “Virus”. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
In case your Chrome, Firefox or Explorer browser has been greeting you recently with a new startpage named Chromesearch.club, then you probably have installed a browser hijacker called Chromesearch.club “Virus” on your computer. Browser hijackers are programs with a rather negative reputation and despite that they are not as dangerous as a Trojan horse or Ransomware infection, many users want to remove them from their computers. The reason is, such programs tend to take over one’s browser and install some new homepage or search engine on it. The newly installed component usually starts to redirect the search queries and prompt people to click on various nagging ads, banners, and pop-ups. The purpose of the hijacker is to advertise and generate traffic and clicks, which benefit certain marketers and software developers. You as a user, however, may not really benefit from the intrusive ads generation and redirects. In the next lines, we are going to tell you more information about the typical activities a program like Chromesearch.club can be related to, as well as the reasons you should consider uninstalling such software. If you decide to remove the hijacker, the free Removal Guide below will guide you through the process while the professional removal tool can scan your PC throughout.
What is Chromesearch.club doing on your computer?
Typically, a browser hijacker like this may install some elements inside the users’ browsers (such as toolbars, search engines, homepages, and shortcut buttons) and try to manipulate their search queries by redirecting them to some sponsored content. Different websites, blinking boxes, new tabs, ads, sales offers and intrusive pop-ups messages may constantly interrupt the normal browsing activity without the users’ approval. Obviously, such activity can be very frustrating, especially for people, who use their browser on a daily basis for work or leisure. That’s why it is not surprising that lots of users desperately seek for ways to remove programs like Chromesearch.club and get their browser settings back to normal.
What dangers might occur from a Browser Hijacker?
It is rare for Browser hijackers like Chromesearch.club to cause serious issues or direct harm to the users’ computers. As we already said, the aim of this software is to advertise, not to corrupt your system. In regard to this, the hijacker may try to collect some valuable information from your browser (such as your history of searches, bookmarks, location, language, frequently visited pages, etc.) and transmit it to third-party marketers and advertisers. This is not malicious activity, but it may be seen as a form of a privacy invasion for some users. Another indirect danger, related to this software is the fact that you may eventually get exposed to some other security hazards if you let the hijacker automatically redirect you to random sites and ads. Since you have no way to check the legitimacy and safety of every pop-up or new page that gets displayed on your screen, you have all the right to question it. In some rare cases, you may unknowingly bump into fake ads, misleading links or already infected web pages, which could be transmitters or all sorts of viruses, including Trojan horses and Ransomware. We know that you definitely don’t want this to happen to you, so in order to eliminate such a possibility, we suggest you permanently uninstall the hijacker from your system and remove all of its components and ads.
Are there some tips to prevent browser hijacking?
As with any other potentially unwanted software, it is much easier to avoid the installation of a browser hijacker rather than to deal with it later. That’s why here we will share some useful tips with you. Typically, programs like Chromesearch.club may be found everywhere on the web because they are distributed as free software. Oftentimes, the software developers include them inside some free software setups and distribute them as “suggested programs” in order to earn some Pay-Per-Click revenue form the displayed ads. Knowing this, you have to be very careful when installing new software on your system, as this is the most common way to end up with a browser hijacker or some other ad-generating software. Always read the EULA and select the Advanced/ Custom installation options over the Automatic/ Quick ones, because this way you can have full control of the entire software package. If you have skipped these instructions and now you have to deal with Chromesearch.club, we have covered the removal of this program in the guide below. Feel free to use the instructions or, if you need a quick and automatic uninstallation, scan your PC with the professional Chromesearch.club removal tool.
SUMMARY:
| Name | Chromesearch.club |
| Type | Browser Hijacker |
| Detection Tool |
*Source of claim SH can remove it.
Chromesearch.club “Virus” Removal
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.
Keep in mind, SpyHunter’s malware detection tool is free. To remove the infection, you’ll need to purchase the full version. More information about SpyHunter and steps to uninstall.

Are there any suspicious-looking IPs in your hosts file or shady Registry entries in the Registry Editor?
Both entries are okay and shouldn’t be removed.
All sorted. Changed / Updated the Group Policy as recommended and viola! – all sorted.
We are happy to hear that!