This page aims to help you remove .Codnat Virus Ransomware for free. Our instructions also cover how any .Codnat file can be recovered.

Malware threats that can infect your System are all over the Web. Today, one of the nastiest and most harmful sorts of malware is what is referred to as Ransomware. Virus programs which fall under this PC virus category are very tough to deal with due to the fact the way they function is different from that of other virus forms. What we are attempting to achieve with this post is give you info about one specific Ransomware version that’s called .Codnat.
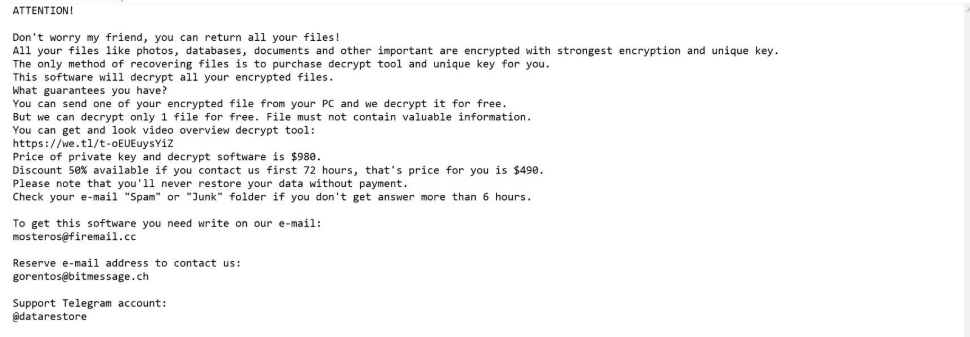
What’s special about cryptoviruses like this one and others like .Fordan .Sarut, .Dutan is the fact they utilize an advanced encryption code to block the access to the private user data stored onto the infected device. Should the virus’ victim want to regain the access to the sealed files, they’d be required to pay a ransom for the file-decryption key. Soon after the end of the data encryption process, the user gets informed about what has just happened on their PC through a message that pops-up on their desktop. For anybody that have already stumbled upon this nasty malware virus, we’ve created a guide which you could use to potentially cope with the virus infection.
How .Codnat File Virus Works
There are several things which make Ransomware computer viruses as perilous as they are. The first aspect that makes Ransomware such a serious inconvenience is its potential to remain hidden and unseen right until it has already completed its agenda and the data has been blocked by its encryption. This questionable and sneaky strategy of functioning is precisely why nearly all people never ever notice what is happening regarding their files until finally it’s too late.
One other nasty thing this type of infections are often characterised by is the degree of intricacy with which they have been made. For sincerity’s sake, we should tell you that due to the high-level of the file encryption applied by some Ransomware viruses, oftentimes, the software documents stay locked and the victim users are left unable to reach them.
You might be wondering precisely why malware versions such as .Codnat normally avoid being noticed by any anti-virus piece of software. Though Ransomware viruses seem to be pretty dangerous, they usually do not harm the Computer or its system which explains why an antimalware program will more often than not dismiss a Ransomware infection as something that’s not dangerous. Such a virus doesn’t harm anything that you keep in the system – the encryption that is used, in and of itself, is not harmful.
The cryptovirus will begin by creating encoded copies of your data and after that it would delete the original copies. As the process of file encryption is actually a data-security method, the security program you have installed would likely not detect it. As soon as this process is done, the targeted user, in most cases, gets a notification telling them about the completed encoding procedure. What’s more, such alarming messages normally include some more warnings, ransom requirements and their corresponding deadlines and the currency preferred by the online hackers. Paying the money, however, is really not what your first choice should be. Instead, it’s better to try out some other potential courses of action and see how effective they may be. One such option is our guide which we have prepared for anyone who may have landed .Codnat in their machines and who may have had their files locked by the cryptovirus.
SUMMARY:
Remove .Codnat File Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.




Leave a Reply