Hey I Know Your Password Is
Once in the machine “Hey I Know Your Password Is” is capable of various criminal actions, including (but not restricted to) spying, information stealing, introduction of other threats like Ransomware or Rootkits into the system, data collection and data transmission, and even corruption of the system. All in all, nothing good can be expected from “Hey I Know Your Password Is” malware.
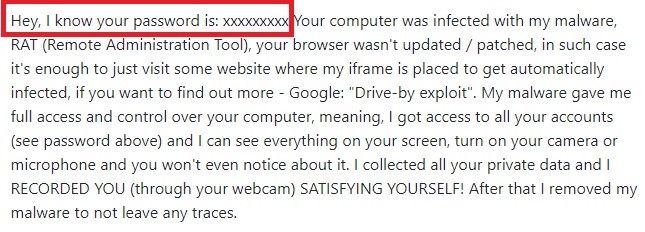
The “Hey, i know your password is” Email Scam will try to trick you into giving money to the hacker
If your PC has been attacked by a strange program called “Hey I Know Your Password Is”, and you have lost control of the system, you should learn how to handle Trojan horse viruses, because that’s precisely what has sneaked into your machine. There’s no need for panic, though, because, in the next lines, we’ll offer you a brief explanation of the characteristics of this threat, and we will provide you with a step-by-step removal guide, with an attached professional removal tool inside of it. All you need to do is simply follow the directions written in there, and remove the infection properly.
The “Hey I Know Your Password Is” Email
Unfortunately, the “Hey I Know Your Password Is” Email can be very sneaky. The “Hey I Know Your Password Is” Email can be disguised as all kinds of web content, and in this way make it harder for the web users to avoid them. The hackers who create the “Hey I Know Your Password Is” Email usually mask it as seemingly harmless documents, such as email attachments, images, PDF files, Zip files, or promotional links.
Probably, there are no Internet users who haven’t heard of the Trojan Horse malware family, and there’s a good reason for that. Trojans such as “Hey I Know Your Password Is”, Drive by Exploit, Recorded you have some important characteristics that distinguish them from all other kinds of online threats. For example, they cannot be self-replicated on other machines or networks like typical computer viruses. Also, most of them cannot infect you if you don’t interact with a malicious transmitter that carries them.
However, the Trojans may also be concealed in a song or a video file, in an application installer, a torrent, or even an advertisement. Therefore, detecting the hidden danger is in many cases nearly impossible without the help of reliable security software. You can easily get infected just by clicking on some of the transmitters, and, sadly, there may be no visible symptoms that can give the malware away. ⠀
What is “Hey I Know Your Password Is” capable of?
It can get your files seriously messed up, and can trigger enormous amounts of chaos in your computer. For instance, “Hey I Know Your Password Is” could allow the hackers to access your machine remotely, and exploit its system resources by turning it into a bot, and using it for spreading other malware infections. With full access to the OS, the crooks can view your private data, change your files, or even delete them all. That’s why it’s highly recommended that you remove “Hey I Know Your Password Is” as soon as you detect it, and thus prevent the hackers from messing with your computer.
How can you remove “Hey I Know Your Password Is” effectively?
To remove “Hey I Know Your Password Is”, we suggest you pay close attention to the steps in the removal guide below. Note that if you chose the manual removal method, you will have to interact with some important system settings in order to locate and delete the malware. Therefore, if you think you may not be able to correctly follow the manual instructions, we suggest you use the professional “Hey I Know Your Password Is” removal tool that will automatically get the job done for you.
SUMMARY:
| Name | “Hey I Know Your Password Is” |
| Type | Trojan |
| Detection Tool |
Remove “Hey I Know Your Password Is” Email
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment