This page aims to help you remove .Hofos Virus Ransomware for free. Our instructions also cover how any .Hofos file can be recovered.
If you have come to our page because you have been infected with a terrible file-encrypting virus named .Hofos, then you have come to the right place. Here, we will tell you the most important things you need to know about this type of malware, which, in turn, will give you the opportunity to make an informed choice on how to deal with it in the most effective way. In relation to this, below, you will find instructions compiled by our “How to remove” team that will show you how to find and remove .Hofos from your system as well as suggestions on how to recover the files that this malware has encrypted. Please, keep in mind though that this is a Ransomware-based infection and the programs of this type are the hardest type of malware to fight. The consequences of their attacks can sometimes be irreversible and that’s why you should carefully consider the risks and use only trusted methods to deal with them.
How does .Hofos File Virus operate?
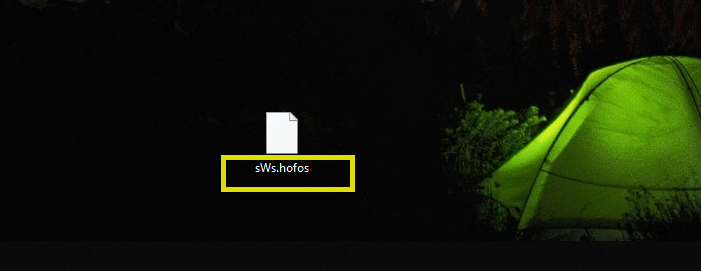
.Hofos is a continuation of a recent ransomware family including .Roldat , .Todarius. Typically, these are files that the victim uses the most, such as documents and all sorts of pictures or videos. Then the Ransomware creates a list of targeted files that it secretly starts copying one by one. The copies of the listed files are encrypted with a complex code while the originals get deleted as soon as all copies have been made. This means that the victims are left with a bunch of encoded pieces of data that cannot be used or opened since none of the programs in the computer are able to access the encrypted files. When the file-encryption process completes, the malware generates a special decryption key which it stores on the servers of its criminal creators. The purpose of this whole process is simple – to demand a ransom from the unsuspecting web users in exchange for the decryption of the locked data with the special key. The hackers behind .Hofos typically display a notification on the screen of the infected computer where they place their ransom demands and deadlines. Similar to this one:
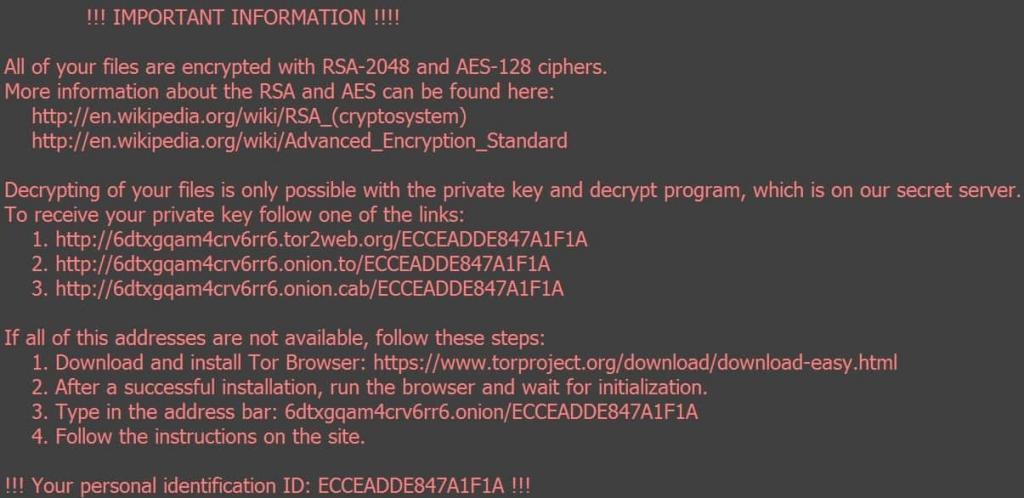
The amount they require for the decryption key may vary from several hundreds to several thousands of dollars, depending on whether the victim is a single individual or a representative of a large organization or institution. Most often, the ransom is required to be paid in bitcoins or in some other cryptocurrency as such transactions are quite difficult for the authorities to trace. It is largely due to this that the extortionists so successfully get huge sums of money from their victims and are not afraid of persecution.
Unfortunately, even if you pay, you may be left with nothing that could help you. This is because the hackers simply do not care if you can ever use your precious files again or not. Therefore, it can be expected that they will not send you the promised key. Besides, there is no guarantee that if you, by any chance, obtain that key, it will effectively reverse the applied encryption. In the programming world, things are quite subtle, so any mistake in the code can significantly affect the final result. If, however, you focus on the removal of the infection, you may at least have a clean and safe computer that you can use for storing new data. Moreover, below there are some alternative file-recovery options that you can try.
SUMMARY:
Remove .Hofos File Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply