This page aims to help you remove .Jack File Virus Ransomware for free. Our instructions also cover how any .Jack file can be recovered.
Introduction to Ransomware
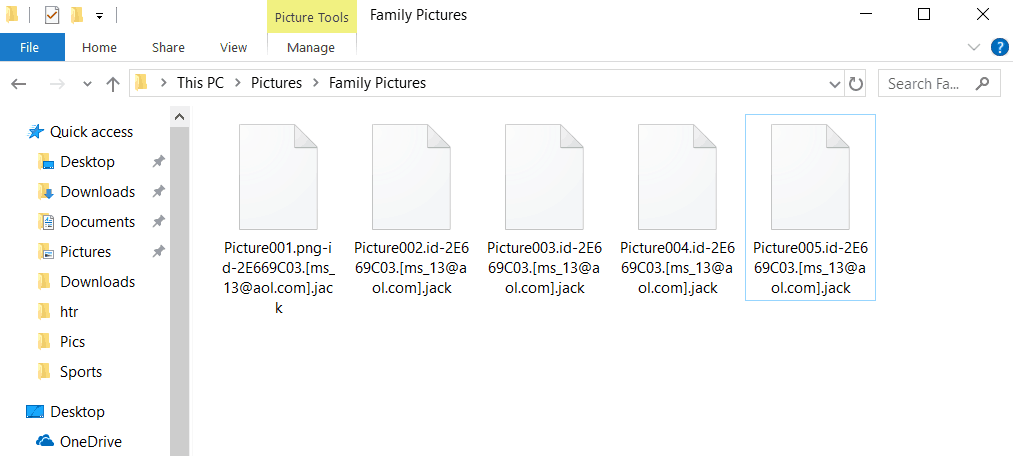
The following article discusses one very common and very dangerous malware menace known under the name of .Jack File Virus. According to the computer virus categorization, this virus program is what experts would refer to as Ransomware. In fact .Jack File Ransomware is the newest member of the Dharma Ransomware family. Such type of dangerous software is usually capable of encrypting the infected user’s personal data the moment their machine gets attacked by the virus program. After the virus program’s task has been accomplished, the user is ‘greeted’ by a pop-up notification within which the hacker notifies their victim that in case they want to have their computer data decrypted, they would need to send a set amount of money in exchange for the decryption code. The pop-up normally involves instructions concerning the required ransom transfer that need to be strictly followed. Additionally, threats may be included in the notification – they may declare that in the event the targeted user chooses not to make the money payment, they would never get the decryption code.
To all the victims of the malicious .Jack that are currently reading this – we have worked hard so as to come up with the current article and the removal Guide that is added to it with the single intention of aiding you. It is recommended that you read the paragraphs down below and make use of the instructions provided within the removal guide.
How .Jack Ransomware Works
An important aspect about computer viruses of this form is that Ransomware is not like other, more usual sorts of malicious software. Typically, no real damage gets inflicted in the case of a Ransomware infection neither to the PC’s system nor to the personal files that have been on its HDD. The procedure of encrypting your personal files is highly complex, but, in most cases, harmless to the targeted computer files. It is just that Ransomware viruses use it for harassing their victims. Those elements of the way Ransomware functions are important to understanding this type of malware and why detecting it and handling it is a rather tricky task.
As a result of the ‘harmless’ behavior of the majority of Ransomware virus programs, they are generally capable of staying invisible and unnoticed even if the targeted victim has an anti-malware software on their PC.
It isn’t the most nice thing to hear but you ought to be informed that, typically, Ransomware doesn’t usually get noticed before it has already sealed the software documents on the infiltrated computer. What is more, there are virtually no signs of the file encryption procedure and the targeted customer may not be capable of realizing what’s happening to their data before the generation of a ransom-demanding pop-up note after all targeted software documents have already been locked-up. Nevertheless, we still advise you to keep an eye out for possible RAM and CPU spikes within the Task Manager in addition to other unusual Computer behavior as this might be a possible warning sign of an Ransomware invasion. The ransomware note reads:
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL [email protected]
IN THE LETTER WRITE YOUR ID, YOUR ID 1E857D00
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: [email protected]
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
Also it seems the new email used by the culprits behind this ransomware is [email protected].
The removal of .Jack Virus
If any of this has happened to your files and they are no longer accessible, our removal steps below should enable you to safely remove the noxious infection and maybe even recover some portion of the currently encrypted files.
SUMMARY:
| Name | .Jack |
| Type | Ransomware |
| Detection Tool |
Remove .Jack File Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Comment