This page aims to help you remove the Bigdater.me Virus. Our removal instructions work for Chrome, Firefox and Internet Explorer, as well as every version of Windows.
Bigdater.me
Most such applications ,like Bigdater.me,are actually seen as potentially unwanted and if you currently have one such software component inside your browsing program, you are likely to want to have it uninstalled. The usual reason for this are the added changes to the browser’s homepage address and/or to the default search engine service that Bigdater.me uses.
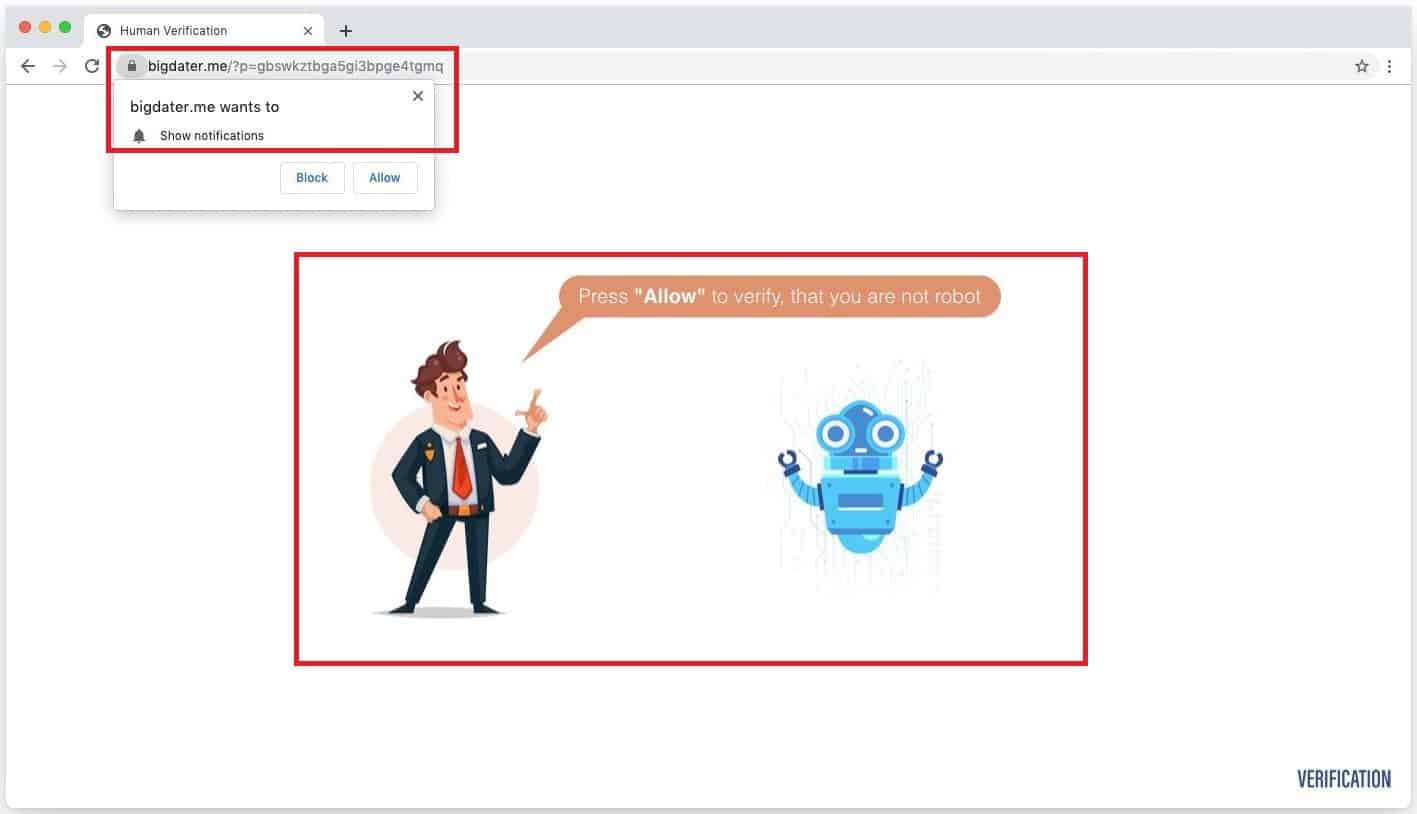
The Bigdater.me Virus will try to trick you into allowing Push notifications.
One other symptom associated with this sort of apps is the page-redirecting and ad-generating activities that some hijackers are known to initiate. Normally, none of this should be harmful to the computer in which the hijacker has gotten installed. However, the functionality of the browser may get severely worsened by the unwanted and oftentimes unhelpful changes imposed on it. The random ads and page-redirects which are likely to start popping-up every now and then during the user’s browsing sessions won’t make things better either. So, in conclusion, there really is no point in keeping such apps inside your browsers – the hijackers, while not damaging, are also typically not helpful and may actually make it difficult for you to browse and explore the online world in piece.
Below, you will find a useful guide with the help of which you should be able to easily take care of one recently reported app that can be regarded as a browser hijacker. The name of this app is Bigdater.me and if you have it in your machine but do not know how to properly remove it, allow us to show you the uninstallation steps that will enable you to dispose of the invasive software.
The Bigdater.me Virus
Bigdater.me may seem like a dangerous virus and your antivirus software may even flag it as malware but it may actually turn out to be a rather harmless app that may not really represent an actual threat to your system. This is oftentimes the case with the browser hijacker apps – they are additions to Firefox, Chrome and other browsers and usually look and operate similarly to normal extensions for such browsers
Typically, as soon as Bigdater.me gets removed, all of its annoying activities should cease and there should be no harm done to your system. Bigdater.me is different from a Ransomware and it won’t mess with your computer like a Trojan. However, it is important to remember to keep your distance from the different advertising and marketing materials that this annoying app may expose you to in your browser. Do not click on the ads, do not interact with the pages that Bigdater.me may redirect you to. The reason for this precaution is the fact you cannot be sure about the origins of the commercial content that you are getting shown. Some ads may be legit while others may be redirects to less-than-reliable sites and pages. Due to this, if you don’t want to risk getting your data attacked by a Ransomware cryptovirus or your system corrupted by a Trojan Horse, be sure to avoid the obscure ads that may get shown on your screen by the Bigdater.me hijacker.
SUMMARY:
| Name | Bigdater.me |
| Type | Browser Hijacker |
| Detection Tool |
Bigdater.me Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Leave a Comment