Since you have found yourself infected with qqovd.com, the removal guide below should serve your purposes fully. However, if you cannot remove qqovd.com using it, then it means our information is out of date, an a new “version” of the virus has been released. If this happens, please let us know in the comments, and we will manually resolve your situation.
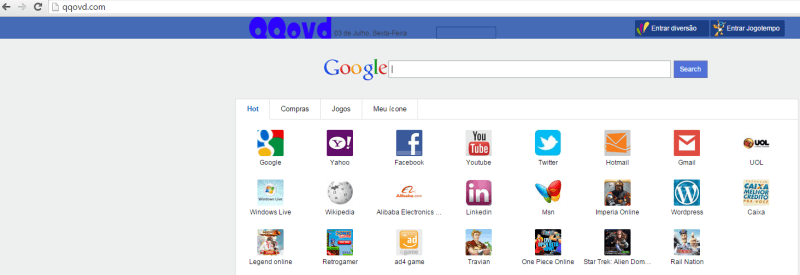
Today’s article concerns itself with the removal of the browser hijacker virus known as qqovd.com. What is characteristic of this kind of viruses is that they will keep generating loads and loads of Ads every time you start your internet browser. These Ads are annoying to deal with, but they will not not harm your computer directly – that is as long as you do not interact with them or install anything they offer you. Removing the virus can take some effort, because you have to delete every file associated with it. Otherwise there is a good chance that qqovd.com will greet you once again the next time you start your browser. Our removal guide covers all information necessary to remove it, so just keep reading.
![]()
The Ads are really a back door for other, more dangerous viruses
We’ve already underlined the importance of not clicking on the Ads, but it’s important. Nothing coming out of qqovd.com is real anyway. Any site the hyperlink take you will be fake, maybe even an exact copy if a real site selling things. If you make the mistake of paying anything to these frauds you will soon discover that you got nothing for your money, or worse – a cracked copy that won’t work until you pay even more for an “update”.
You might also get offers for free downloads for different software. Remember that any file related to qqovd.com will be a virus. That’s why these thing are considered back doors/entry point for other viruses.
Ads don’t necessarily always offer you things directly
There is a good chance that you see a number of different messages while you have qqovd.com on your computer. They will generally inform you of some “problem” you have a new computer and then they will offer you a free solution. This is just another form of scam that plants to install a virus in your computer. Usually once you install the “free” scanner it will require payment before cleaning the non-existing problem.
One possible way that qqovd.com might have entered your computer through
The so-called program bundles. These are actually installers for programs that install a number of addition programs in addition to the main thing – usually demos or trial versions from the same maker or from partners. Unfortunately sometimes, especially if we are talking about free program, the extra bundled programs are actually some sort of browser hijacker – possibly qqovd.com. If you’ve recently installed such a program and have ran the default installation option then that’s one way qqovd.com got it. For this reason it’s generally recommended to go with the advanced installation option at all times. If all is good then it’s just a couple of clicks on the next button to get the same result as with the default installation. Otherwise you get to see exactly what added software is getting installed and you have the option to block it from doing so. We recommend you do it for every program you don’t really need.
Remove qqovd.com
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.
Optimization
And that’s it. Well done for removing qqovd.com. We’ve prepared a short and sweet optimization guide, specifically designed for users who just removed a virus. It is completely free, you do not need to download anything, and it’s not very time consuming. If you are interested, you can check it out here.

Leave a Comment