This page aims to help you remove the Registry Reviver Virus. Our removal instructions work for every version of Windows.
Registry Reviver
The “purpose” of Registry Reviver is to optimize your Windows registry, but in fact it will display false results
Malware comes in various forms and shapes ( “Drive by exploit”, Bitcoin Blackmail Email Scam) , but there is nothing that could match a Trojan horse infection’s cunning nature. Registry Reviver is such a danger, and you’ve likely become a victim of its malicious actions if you’re reading this. Therefore, it is highly recommended that this Trojan gets removed from your system immediately, because it can do a lot of harmful stuff while on the computer. This involves introducing various viruses, including a Ransomware or Rootkits into the machine. The good news is that our team has prepared a detailed removal guide in order to assist you with cleaning your system from the infection, and removing all the Registry Reviver malicious files that are on it. But do not jump right to the instructions before you learn more about this particular threat and its specifics, as this will help you remove it effectively. In the next lines, you will find some helpful information on the distribution and infection techniques of this Trojan, as well as some tips on prevention.
The Registry Reviver Virus
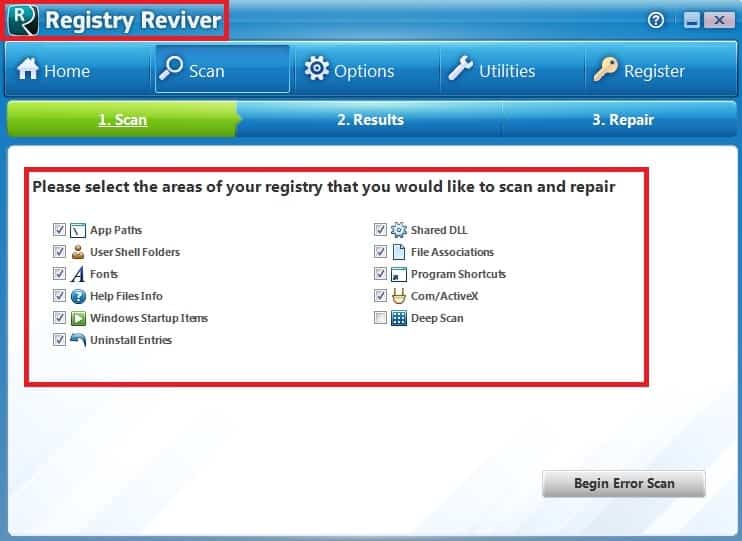
The Registry Reviver Virus will display fake results and insist to “repair” your system
Trojans are extremely versatile, and harmful pieces of software. They are commonly used by people with malicious intentions for different criminal activities, including the distribution of malware such as Ransomware, viruses, Spyware, etc. If such a threat sneaks inside your computer, they can silently initiate specific harmful actions, which can provide unauthorized remote access to your system, or create system vulnerabilities. With their help, the cyber criminals can establish full control over the infected device, and mess with the settings and the data, stored there. An infection like Registry Reviver, for instance, can be used to steal your bank account details or credit cards information, as well as to keep track of everything you do by hacking into your webcam or mic.
All these activities generally take place in the background, as the Trojan tries to remain unnoticed, and execute the damaging actions it has been created for without showing visible symptoms. This is why it is important to have a good antivirus program in your system, as such a program can assist you with the detection of any unauthorized activity, and notify you about it so you can take actions. Of course, there are a few more things you could do to avoid threats like Registry Reviver and keep them at bay.
Prevention tips
Trojans are the favorite instrument of hackers who try to invade the privacy of the web users, and perform malicious activities. Unfortunately, these threats continue to grow in popularity, and every day more sophisticated variants appear. This is why the best way to keep such malware away from your PC is to take preventive measures. As we said above, one of the best things you can do is to invest in reliable antivirus software, since, without it, it is often almost impossible to identify the hidden infection. For maximum system security, make sure that you frequently update your malware definitions, and run regular scans with the antivirus.
However, you should not solely depend on such software. You can also prevent the contamination with those threats by staying away from suspicious content. We would recommend that you always remain cautious when installing new software or when coming across websites with unrealistic offers, and awards. For instance, do not become too curious to open all the spam messages, ads, and attractive-looking pop-ups you may receive, and you will be able minimize the chances of landing a hidden malware.
SUMMARY:
| Name | Registry Reviver |
| Type | Trojan |
| Detection Tool |
Remove Registry Reviver Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Comment