This page aims to help you remove the The Virus Developer Email Virus. Our The Virus Developer Email Virus removal instructions work for every version of Windows.
The Virus Developer
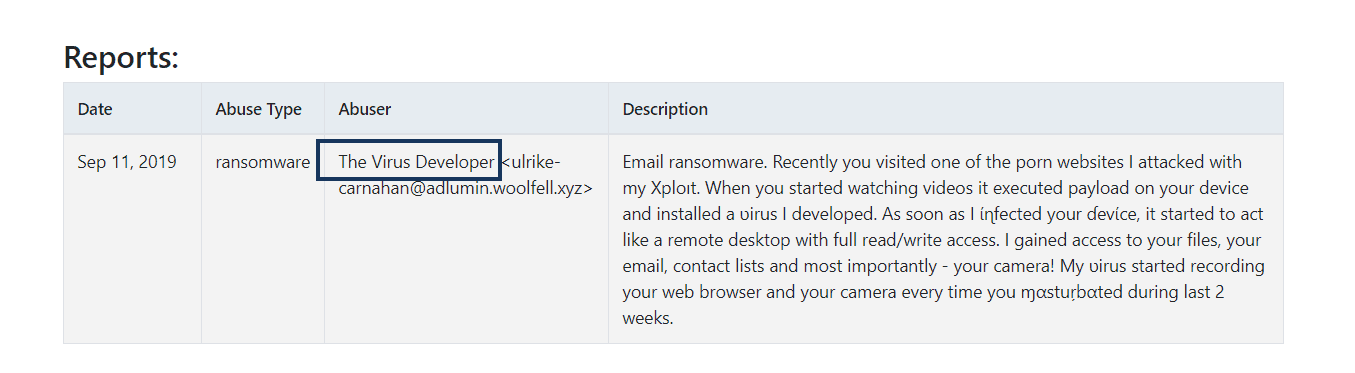
The Virus Developer is a series of slightly differing email virus scams. The main purpose behind the Virus Developer emails is to extort money from the targeted users. However there are reasons to believe that in some instances real virus threats might be behind the Virus Developer emails. In those cases the affected users should be wary of dealing with potential malware infections.
The The Virus Developer Email Virus will try to trick you into sending money to the hacker.
Trojan Horse infections like The Virus Developer, Drive by Exploit, Recorded you are some of the most widespread malicious computer programs, and being able to protect your computer and data against them is crucial. The representatives of the Trojan Horse family are infamous for their versatility, and it is oftentimes difficult to determine what the exact goal of such an infection might be. A Trojan can be used to sneak other threats in the infected computer, or it may spy on the activities of its victims. Such infections may also force the machine to execute certain tasks irrespective of the user’s permission or knowledge, and they may also restrict the user’s access to certain settings in the computer. A Trojan Horse attack may lead to various negative consequences for the user – loss of data, loss of money, damage to the system, emotional harassment, and more.
More about the Virus Developer emails
The key to preventing any of this from happening is detecting the Trojan early, and here lies another serious issue with regard to this type of malware threats. The Trojans are notoriously difficult to spot on time. Different types of disguise is used to keep such threats unnoticed and undetected, allowing them to complete their nefarious tasks in silence. Weeks, and even months after the infection, the attacked user may still be unaware of the Trojan’s attack. One common technique used by many Trojans, which allows them to stay hidden in the system, is when the malware’s files, processes, and system entries are disguised as legitimate system elements. Similar names of the processes and files, similar appearance of the files, and other such tricks are used to make it difficult for the user to spot the malware data in their computer.
The Virus Developer is an example of a Trojan Horse threat that can b particularly sneaky and difficult to spot, but since you are here, we assume that you suspect this infection may currently be present in your machine. If that’s indeed the case, we advise you to keep on reading, and also have a look at the removal guide for The Virus Developer down below.
Sneaky infection methods used by The Virus Developer Email
There is a reason this type of malware is named after the ancient Greek myth about the wooden Trojan Horse. The malware computer programs of the same name are usually designed to appear harmless, and maybe even helpful, and desirable to the user. Infections like The Virus Developer may represent software updates, program installers, or other types of files that the user may be tempted to open. And, upon opening the file of a hidden Trojan Horse using an Admin’s profile, the malware is allowed to gain full Administrative privileges in the computer. This, in turn, makes it quite difficult to eliminate the threat, and handle the consequences of its attack. Difficult, but hopefully not impossible. If you indeed thin The Virus Developer may be presently inside your computer system, the suggested course of action is to study the following removal guide, and make use of its steps, and of the advanced removal tool present there, in order to eliminate the malware before it gets too late for its removal to matter.
SUMMARY:
| Name | The Virus Developer |
| Type | Trojan |
| Detection tool |
Remove The Virus Developer Email Virus
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Leave a Comment