This page aims to help you remove the Wacatac Virus. Our removal instructions work for every version of Windows.
Wacatac
Trojan viruses like the nefarious Wacatac infection are and have always been a major problem for the owners of PCs and have recently become a serious threat to Mac users as well. In general, a Trojan Horse is a dangerous piece of code intended to silently infiltrate the system of the targeted computer and then carry out some kind of malicious criminal activity inside the attacked machine.
So far, there seems to be nothing unique about the way a Trojan Horse operates – most forms of malware do the same thing. However, there are several key aspects associated with Trojans that make them some of the worst malware programs you may encounter. One of those aspects is the way Trojans are used. After an infection of this category has entered the machine, it may not limit itself to a single task like a Ransomware cryptovirus or a Spyware program. Instead, a Trojan may try to do couple of things that target and damage different parts of your system. This is why when a Trojan attacks, you may start to get BSOD crashes in your computer, the data in the system may get replaced, modified, corrupted, deleted and more, some essential system elements like the Registry keys may face unauthorized alterations as well. It’s even possible that the Trojan loads more malicious programs in the computer – these viruses oftentimes double as backdoors for Ransomware, Rootkits and other insidious infections. Also, in many cases, the Trojan may not really damage anything in the machine – it may instead stay silent and simple gather sensitive information by spying on your activities online and offline or it may use your machine’s RAM, CPU and GPU for tasks such as mining of BitCoin and distribution of spam. The problem is, you cannot really be sure which one of these malicious activities may be the ones that the Trojan is being used for.
The Wacatac Trojan
The malicious program known as Wacatac is one very dangerous Trojan and it definitely is something you don’t want anywhere near your system. In many cases, if Wacatac infects a given computer, the computer’s user may not even know that there is a malware piece in the machine for weeks and maybe even months, thus allowing the infection to complete all of its insidious tasks.
Since you are here, however, it is likely that you are one of the lucky users who have spotted some sketchy activity in their machines and have realized that they have an Wacatac infection on their hands. If that’s the case with your machine, the advice that we can give you is to use the guide that we will offer you down below. It’s manual steps should be enough for you to chase away the infection. However, if this doesn’t work or if you simply prefer a quicker solution that requires less manual tinkering, you can always use the suggested removal tool as it is yet another effective solution against this sort of infections.
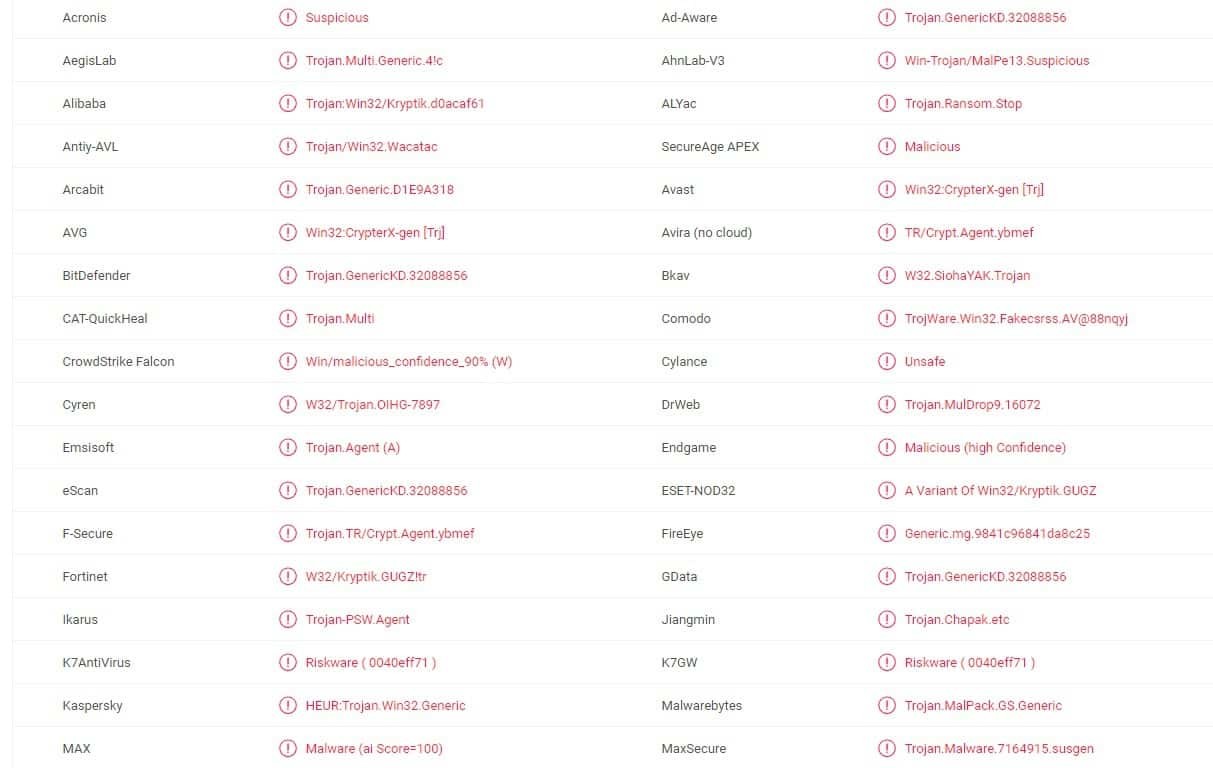
SUMMARY:
Wacatac Virus Removal
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

Leave a Reply