Y2mate
Y2mate is a browser-hijacking website that displays questionable ads on the screens of the users who visit it. If you allow notifications on Y2mate, it will also start to show you potentially unreliable ads and offers even when your browser isn’t being used.
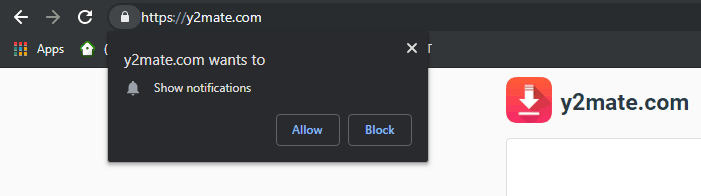
The Y2mate Virus will try to make you to subscribe to its Push notifications
If you are reading this page, the chances are that you have encountered a stream of annoying commercials on your screen and now you are seeking how to remove it. It is also quite possible that you’ve spotted some other symptoms, for instance, a modified starting page and/or default search engine, a new toolbar or some shortcut buttons that constantly redirect you to different sponsored sites. In this case, you should know that the most probable source of all these modifications and ads is a Browser Hijacker program called Y2mate. In the next lines, we will provide you with some basic info regarding this type of software, as well as a guide on how to uninstall it from your PC in a fast and risk-free manner.
Is Y2mate safe ?
Y2mate is a website that converts YouTube videos but is also known for operating as adware. Users primarily visit Y2mate to convert and download videos from YouTube but the site’s domain is considered unsafe and the ads you may see there could be hazardous.
When faced with an intrusive stream of web Ads most web users first think that their PC has probably been infected with a virus. This is quite understandable because the word “virus” has become a synonym for everything that can go wrong with the computer’s system. Yet, we need to say that computer viruses and Browser Hijackers are two different categories of software with very different purposes. Most viruses do not use web Ads to annoy and spam the users. They have much more malicious ways to mess with the computer. For instance, the victims of a real computer virus may have their files corrupted or stolen, they may have their system damaged or spied on, while the people contaminated with a Browser Hijacker such as Y2mate, Www1.ecleneue.com or Ytmp3.cc will most probably be showered with annoying pop-ups, blinking boxes and redirect messages. The effects from the presence of those two types of software in the system in the first case will be fatal, while in the second case will be easily ignored and even removed without any negative consequences. That’s why one should not mistake programs like Y2mate for a software virus because they are definitely not the same thing.
The Y2mate Virus
Y2mate is a site that is used for converting and downloading videos from YouTube but it also has some adware qualities. The Y2mate virus is how some users refer to this site because it can show questionable and potentially hazardous ads on the screen.
PC viruses are typically destructive – to begin with. Just as an example we can mention the Ransomware cryptoviruses, which can encrypt personal data and blackmail their victims for ransom payments in exchange for its liberation. As a contrast, the scariest thing that Y2mate “Virus” can do to a computer system is to make it experience a slow-down due to excessive ads generation. Don’t forget that despite the fact that Browser Hijackers are normally considered as non-threatening, they might still contribute to the exposure to security dangers that you should be aware of. For instance, one of the main issues with programs like Y2mate is the fact that some of the ads it may display might not be real advertisements at all. Apparently, clicking on any of those adverts could redirect you to potentially dangerous webpages where real infections and viruses may lurk. That’s why getting rid of such software is actually recommended and is a good way to prevent an accidental encounter with threats like Ransomware or Trojan Horses. Last but not least, a program such as Y2mate could make your computer slow and unresponsive due to excessive usage of CPU and RAM resources.
SUMMARY:
| Name | Y2mate |
| Type | Browser Hijacker |
| Detection Tool |
Remove Y2mate Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android, iPhone.

To remove the y2mate virus we need to detect and scan malicious processes in Task Manager. Finds in the control panel. Programs must be installed with malware
Hi alma,
i couldn’t understand what exactly do you mean. Can you be a little bit more specific so i can respond to you more accurately?