Repp
Repp is a ransomware-based infection intended to encode user data and blackmail the owners to pay ransom to decode it. Repp typically uses complex cryptography to render a specific list of digital files inaccessible and displays a ransom-demanding message on the victim’s screen.
UPDATE:
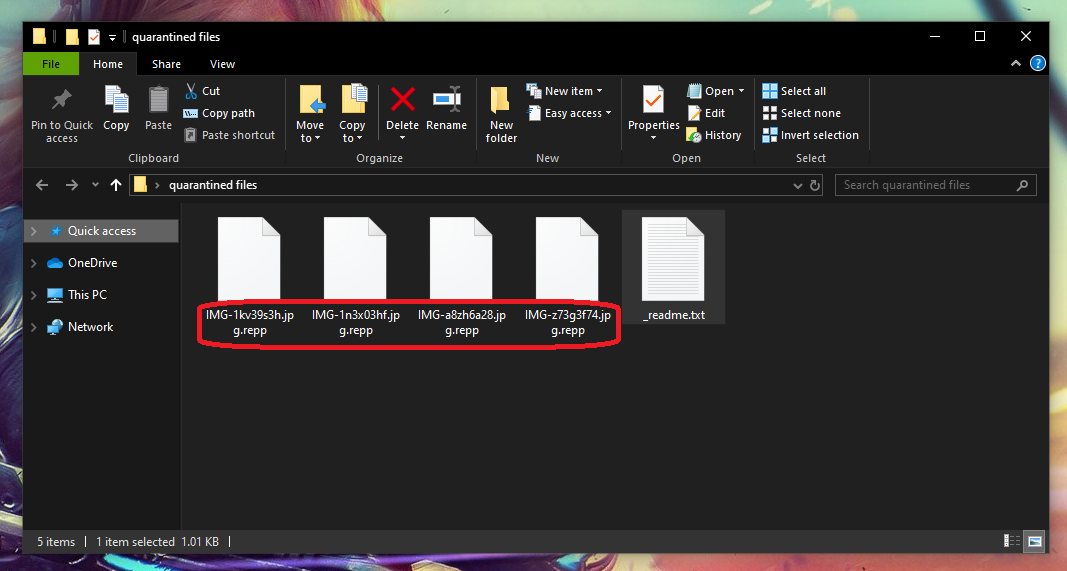
The Repp virus appends the .repp extension to the filenames of the files it encrypts. Once the Repp Ransomware completes the encryption, it creates a notepad file named _readme.txt and places it inside every folder that contains encrypted data.
Once the Repp Virus has infected you it will start encrypting your files.
Ransomware viruses such as Repp, Btos and Npsg are probably some of the toughest pieces of malware to deal with. Their file encryption code is usually almost impossible to crack without a decryption key, and the criminals who hold that key are typically very ruthless when they ask for a ransom payment. However, there is still some hope to recover your encrypted files and remove Repp without paying any money to anyone. And this is what we are going to cover in the following removal guide. Below, you will find a set of ransomware-removal instructions, some file-recovery suggestions and a professional removal tool that you can use to deal with this infection.
The Repp Virus
The Repp virus is money-extorting software from the ransomware category that can ask its victims for ransom in order to restore access to their personal files. The Repp virus typically encrypts files that are considered of great value and keeps them hostage until the ransom demands are satisfied.
Viruses such as Repp can work right under the nose of most anti-virus programs and this gives them an enormous advantage and the ability to surprise their victims when they least expect it. Therefore, there is very little possibility that you will intercept a ransomware virus before it completes its mission. Ironically, the majority of anti-virus programs do not view the file encryption process as malicious and that is because it essentially is nothing more than a data protection method. The encryption does not corrupt or destroy the target files but simply makes them unavailable without the application of a decryption key. However, in cases where a threat like Repp is behind the attack, the files are secured and the decryption key is stored away from the actual owners of the information on some remote servers where only the hackers can access it. In order for the victims to receive it, the crooks demand money as ransom.
The Repp file decryption
The Repp file decryption is a complex process that, in theory, should make the encrypted files available again. In reality, however, the Repp file decryption is a risky process that may not always have a successful outcome. If you go down that road and decide to pay the ransom that the hackers want, you’d basically have to be ready to lose your money no matter the outcome. This is because the criminals who robbed you of access to your files may never send you the decryption key they have promised and decide to simply vanish with the money. Or they may send a decryption key that does work and ask you for more money for a new key. That’s why paying the ransom is the least advisable option.
The other possibilities to deal with Repp and its file encryption are also not many and cannot guarantee full recovery of anything, but we do encourage you to give them a try as they at least will save you the money you’d waste on the ransom payment. Of course, before you try any file-recovery method, make sure you first remove the ransomware from your system with the help of the steps below. Then you can go to the instructions in the file-recovery section to try to get your data back from device backups or use your personal backups to minimize the data loss.
SUMMARY:
| Name | Repp |
| Type | Ransomware |
| Detection Tool |
Remove Repp Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Hi,
I really need your help. My Laptop fully infected by .repp virus. I have no idea how to recovery my files and folders. Please help me and explain the full in detail. I will be wait your reply as soon as possible.
Thank you so much.
Hi Maninder Singh,
first follow the removal guide. After that, at the end of the guide, you will find link on how to recover your files and other decryption methods.