Rigd
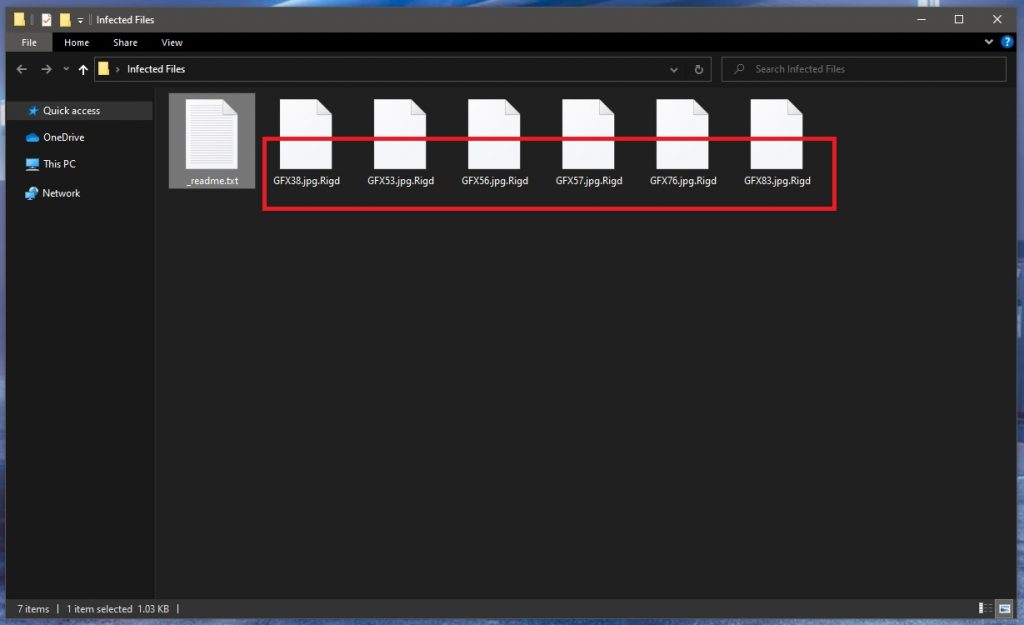
Rigd is a devastating computer threat that harasses users by locking up their data and blackmailing them for ransom. Rigd secretly encrypts all the important user data on the infected machine without triggering visible symptoms and then reveals its presence through a ransom note.
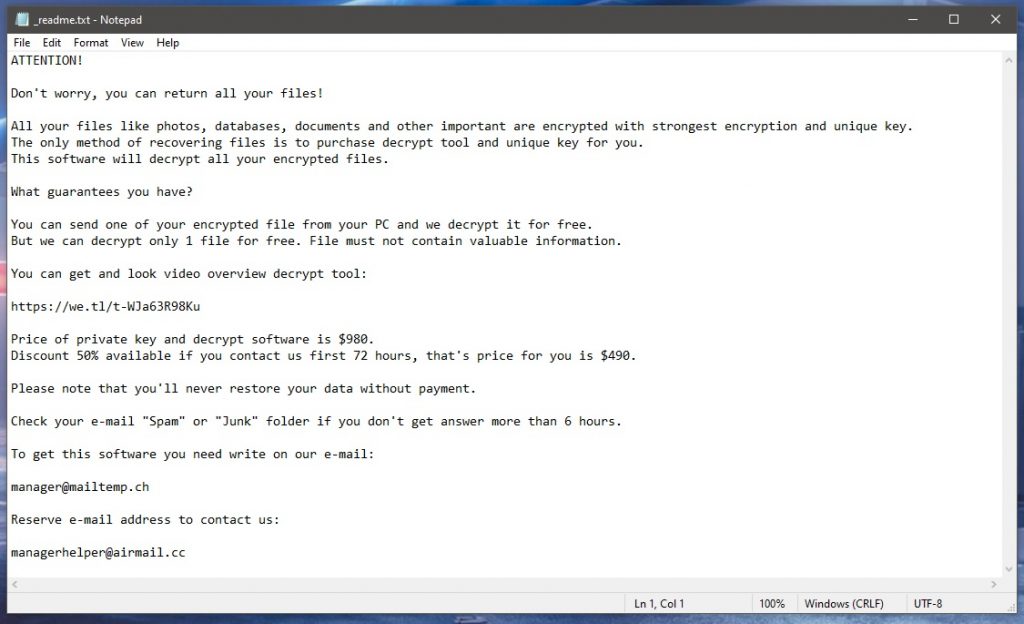
The ransom note usually comes in the form of a pop-up banner that appears on the screen automatically once the encryption is complete and/or whenever the user tries to open an encrypted file. Another option is for the ransom note to be within a notepad file created on the Desktop or inside the folders containing locked files. In all of those cases, the goal of the note is the same – to inform the victim about what is required of them in order for the decryption key for their files to be sent to them. The requirement is also pretty much always the same – the user is told to pay a certain amount of money by following the instructions provided in the ransom note. Usually, this entails the purchase of Bitcoins and their transfer to the virtual wallet of the hacker/s behind the Ransomware like Koom, Efdc . If the money isn’t paid in the exact way described in the note, the key wouldn’t get sent to the victim. However, what many users that have been attacked by Ransomware fail to consider is the fact that this key they so desperately need may not get sent to them even after they do everything according to the instructions in the ransom note and pay the ransom. The cybercriminals on the other side are, well, just that, criminals – you have no reason to trust them and sending them your money only guarantees you won’t see this money again. As far as the recovery of your files is concerned, there’s no guarantee you’d ever acquire the key needed to release the locked data.
The Rigd virus
The Rigd virus is a sneaky computer threat that will silently put encryption on your files to keep them inaccessible. Once the Rigd virus has finished locking up your files, it will blackmail you for a ransom payment in exchange for the files’ release key.
If you aren’t ready to risk your money by paying the ransom or if you simply cannot afford such a payment, our advice is to look through the instructions provided in our guide down below. There, you will find out how you can remove this infection from your system and then try some alternative methods that may help you with the restoration of some of your files.
The .Rigd file decryption
The .Rigd file decryption is a procedure you must complete in order to set your encrypted files free. The .Rigd file decryption cannot be completed unless you have a working decryption key that matches the exact encryption code used on your computer.
However, the decryption process may sometimes be bypassed altogether if the victim is lucky. As we mentioned, in the removal guide down below, you will see some suggestions regarding the potential recovery of your files without the need to pay the ransom so we advise you to have a careful look at them (after you remove the virus).
SUMMARY:
| Name | Rigd |
| Type | Ransomware |
| Detection Tool |
Remove Rigd Ransomware

In this first instruction, a system restart in Safe Mode will be required. This will limit the number of processes and apps that are running only to the most essential ones and will hopefully make it easier for you to spot the malicious processes linked to Rigd.
Before you Reboot in Safe Mode (click the link for more instructions), however, we recommend that you Bookmark this removal guide in your browser for easy and quick reference.

WARNING! READ CAREFULLY BEFORE PROCEEDING!
As soon as the computer successfully restarts in Safe Mode, your first task is to check what programs start with it. In many cases, components of the ransomware infection may be found in the Startup tab of the System Configuration window. That’s why you need to click the Start menu button, type msconfig in the search bar and hit enter:

Then, click on the Startup tab and remove the checkmark from the Startup Items that look suspicious, have odd names, or “Unknown” Manufacturer and simply cannot be connected to any legitimate program that normally starts with the start of your computer.
- Attention! To evade detection, the ransomware may use a fake Manufacturer name to its process. Therefore, it is a good idea to check out online every process in the startup to ensure that it is legitimate.
When you are done with this, click the OK button and close the window.

Speaking about malicious processes, your next job is to check what processes are running in the Task Manager. So, for that, press CTRL, SHIFT and ESC keyboard keys in a combination and click on the Processes Tab.
In it, carefully try to figure out if there are processes that are dangerous. A possible red flag could be the usage of too much CPU and Memory power from a particular process without you doing any actual activity on the computer. Another red flag could be the name of the process, which could contain random characters, or could resemble the name of a legitimate process but with missing or twisted letters in its name.
Anything that look suspicious should be checked for malicious code, and the best way to do that is to right-click the dubious process and select Open File Location:

Once you do that, you should scan the files of that process with a powerful virus scanner, like the one that you will find below:

You will know that the process needs to be ended if its files get flagged as dangerous. After you end the processes by right-clicking on it, don’t forget to delete the infected files and their folders from the File Location.
The next thing that you need to do is check if Rigd has made any unauthorized changes in the Hosts file of your system. Sometimes, a sign of hacking is the presence of suspicious-looking IP addresses under Localhost in the text. To see if any such changes have been made in your Hosts file, copy the line below, then paste it in the Start menu search bar and press Enter:
notepad %windir%/system32/Drivers/etc/hosts
Next, in the Notepad file that opens, scroll down until you find Localhost and pay close attention to the IPs that are listed below:

In suspicious IPs like those on the example image above are found below “Localhost” in your file, it is advisable that you write to us in the comments with a copy of the IPs, so we can take a look at them and suggest your best action.
![]()
Ransomware threats like Rigd are well known for their sophistication and persistence. In many cases, these threats tend to secretly add malicious components in the system’s registry with the idea to make it harder for non-professionals to remove the infection. If you want to deal with Rigd once and for all, however, you need to find and delete any files and folders that could potentially be linked to the ransomware from the registry.
Generally, there are two ways for that.
The first way is to manually search the registry for malicious files by starting the Registry Editor (Type Regedit in the Start menu search bar and press Enter) and then with CTRL and F, type the name of the ransomware infection in the Find box and search for entries that need to be deleted.
If you decide to do that manually, you need to be extremely careful not to delete entries unrelated to Rigd because doing so can damage your system in a serious way.
The other method, which is much safer for non-professionals, is to use the powerful virus removal tool linked on this page and safely delete the entries that it flags as malicious.
Once you clean the registry, make sure that you manually check the content of the folders below by typing each of them exactly as it is shown in the Start menu search bar and pressing Enter:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Basically, in each of the listed folders, you need to search for entries that have been added around the time the ransomware infection occurred. Pay attention to any files and folders with random names. When you open Temp, select everything there and delete it. In this way, you will delete any temporary files that could be linked to Rigd.
![]()
How to Decrypt Rigd files
As a victim of a ransomware attack, your biggest concern is probably how to recover your encrypted files. Fortunately, we have a specially created and very detailed guide on that you can check out here.
Before you do that, however, you need to make sure that any traces of Rigd have been successfully removed from the infected computer. Otherwise, any attempt for file recovery may fail and even your backup sources may be encrypted if you connect them to a computer that has not been fully cleaned.
To check your computer for any hidden ransomware-related files, we recommend you download the anti-virus program on this page or scan any files that look suspicious with our free online virus scanner. Also, feel free to ask us for help in the comments, in case you run into any trouble.
Rigd is a malicious file-targeting program that will use a secret encryption algorithm to block access to the most important files stored on your PC. To regain access to files encrypted by Rigd, you are required to pay a ransom for the decryption key.
The main danger that comes from Rigd is the possibility of losing highly important data such as work or university projects or other valuable data. However, if you have copies of whatever files got encrypted by the Ransomware that is stored on another device or in a cloud, then the attack by this virus shouldn’t be such a serious issue. The same applies if you don’t have any highly valuable files on the computer, and it wouldn’t be a big problem for you if the files that did get encrypted remain in their inaccessible state for good.
It must be said, however, that Ransomware viruses often get paired together with Trojans, Rootkits, and other threats, so if Rigd is in your system, there may be another virus there as well.
Rigd is a virus used as a blackmailing tool, capable of making your files inaccessible through the use of a military-grade encryption algorithm. To infect a system, the Rigd virus can be helped by a Trojan Horse that automatically downloads it on the computer.
When trying to deal with this malware attack and minimize the damage it may cause, it’s important to rationally assess the situation and not give in to the hacker’s attempts to manipulate you. After it completes the encryption, the virus would spawn a ransom note on your computer that will be written in such a way so as to get you to pay the demanded ransom as soon as possible. Even if the files that got locked are really important to you, you shouldn’t act out of panic and straight away pay the ransom. Instead, you should first check your other devices and any cloud services you may use for safe copies of the locked files. Also, another thing you can do is try some alternative file-restoration solutions that may be available in your situation.
To decrypt Rigd files, it’s recommended to seek and use alternative data-recovery techniques rather than pay the ransom. One possible alternative way to decrypt Rigd files is with the help of a free decryptor tool specifically designed to unlock data encrypted by Rigd.
There are many Ransomware-decrypting tools on the Internet and most of them are free, but they are all specialized for a specific Ransomware threat (or several Ransomware variants that are similar to one another). To decrypt Rigd files with such a tool, you’d need one created specifically for this virus.
Extracting older versions of your locked files from shadow copy system backups is another valid method that you can try as an alternative to the ransom payment.
Whatever you decide to do, however, we strongly recommend that you only consider the payment variant as a last resort and even then only go for it if the files that got encrypted are worth the risk.

Leave a Comment