Rote
Rote is a form of Ransomware that will attempt to encrypt the files stored on a victim’s machine and demand a ransom for sending a decryption key. Rote can target large corporations, institutions, and regular web users.
The Rote virus will encrypt your files
Not all Ransomsware versions encrypt your data. Only the cryptoviruses, which Rote is a representative of, can do that. Certain versions of Ransomware can be programmed to lock your device’s display. These are the so-called screen-lockers and they too are designed to blackmail you. What we can tell you about them is that they will simply make the screen of your device inaccessible by displaying a huge ransom-demanding banner that will not go away unless a ransom is paid. However, the largest subcategory of Ransomware is the one that consists of file-encryption programs such as Rote. This is also the most aggressive and most troublesome Ransomware subcategory. Below, you will read about the different characteristics of these infections. You will also find some removal instructions attached to this article so you can try to remove Rote by yourself.
The Rote virus
The Rote virus is a Ransomware variant that encodes personal files and blackmails the victims for a ransom payment. The Rote virus can restrict access to your digital documents and place a ransom-demanding message on your screen.
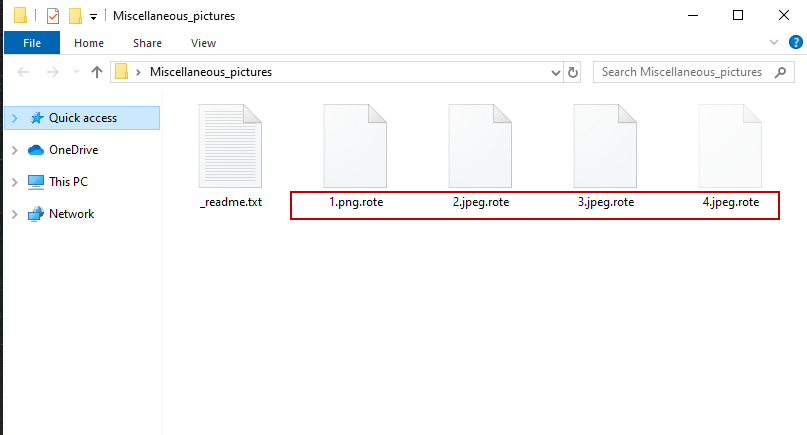
After successfully entering your system, Rote will target specific file formats and attempt to encrypt them all. The encryption method typically goes like this: The Ransomware will create copies of the detected files and will remove the originals. The special thing about these copies is that they are protected with an advanced encryption code that makes them inaccessible. If you want to access them again, you will be asked to pay for a decryption key. The blackmailing is done through a big notification that appears on your screen and provides you with clear instructions on how to pay the demanded sum.
The Rote file encryption
The Rote file encryption is an advanced code that keeps digital data inaccessible until a ransom is paid. The role of the Rote file encryption is to prevent any program from opening or using the encrypted files.
What you should note is that it is extremely difficult to deal with a Ransomware such as Rote. Even security experts may find it hard to handle such a virus and to retrieve the information that has been encrypted by its complex algorithm. Our team, however, has come up with a removal guide that might help you locate and remove Rote from your computer. We have also included a section with file-recovery instructions that are definitely worth your attention if you are looking for alternatives to avoid the ransom payment. Of course, we can’t promise that they will work for certain but they will surely do no harm to your machine. Of course, it is best if you have file backups as this is the only guaranteed way to get back all your information.
Once you remove Rote, it is very important to ensure that your computer never gets infected with Ransomware again. For that, first invest in reliable security software and then try to stay away from illegal web pages, any type of spam (especially spam emails with shady attachments), as well as from random adverts and fake system requests, as these could also sometimes lead to an infection.
SUMMARY:
| Name | Rote |
| Type | Ransomware |
| Detection Tool |
Remove Rote Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.
You can find the removal guide here.

Now please help me to decrypt my files which are now TORE
hello, do you have any update for .rote ransomware deceyptor?
Rote my file