Sabsik may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
Sabsik
Sabsik is a malware tool that can silently infiltrate your system and take over some of its settings. The Sabsik virus is classified as a Trojan Horse – a type of harmful software commonly used for sneaking Ransomware inside the computers they infect.

The Trojan Horse malware family is an infamous category of computer infections that are known for being used for the completion of many different cyber crimes. The Trojans are quite versatile threats and they can be used differently depending on the situation. Here, we will be talking about their newest representative – a piece of malware labeled Sabsik. The information currently available about it isn’t very detailed and we won’t be able to tell you everything about this threat. For instance, we cannot tell you with certainty what its goal might be if it enters your system. As we said, those are quite versatile pieces of malware and more data and research is needed in order to determine the exact end-goal of this specific infection. Still, we can give you some examples of what these problematic computer threats might be capable of so that you get an idea about what you are faced with at the moment. We can also offer you a removal guide for Sabsik which will teach you the steps you will need to follow so as to eliminate the virus. Note, however, that this is a very stealthy infection and removing it manually may be rather challenging, especially for a user who isn’t very experienced. That is why we have also included an anti-malware tool that is tested against similar threats and should be able to make quick work of the Sabsik Trojan. The most advisable course of action if you have Sabsik in your system is to combine the manual steps with the automatic removal tool as that would ensure the highest chances of removing the virus.
The abilities of Sabsik
The Sabsik virus is a type of malware that is used as advanced espionage tool capable of learning your passwords, credit and debit card numbers, and other sensitive info about you. The methods used by the Sabsik Scam are keylogging, presenting the user with phishing forms, and screen-monitoring.
There are quite a few things that a virus of the Trojan Horse type can be used for, but we cannot list them all here. Therefore, we will only tell you about the most common and problematic of all the Trojan Horse uses:
The Trojan Horse viruses are oftentimes capable of inserting other malware inside the machines of their victims. Usually, the Trojan is presented to the user as something that wouldn’t raise suspicion. For example, a computer game installer, or some application that the user may find useful. After the disguised Trojan Horse file is downloaded and executed in the machine, the user may not even realize that their system has been infected. The Trojan is likely to show no symptoms and silently start the process of downloading a second threat on the infected machine. This second threat could be a Worm, a Spyware program, or, in many cases, a Ransomware encryption-virus.
Certain Trojans are also able to obtain elevated privileges inside the user’s machine, which basically means that they’d have nearly unlimited control over the computer. They would be able to stop or modify running processes, or start new ones, to delete and corrupt your data, and even use your computer for activities that would benefit the hacker. A common example of that is when a given Trojan infects thousands of computers and forces all of them to mine cryptocurrency money in order to fill the hacker’s virtual purse.
Now, that you have some idea about what Trojans like Sabsik, Wup.exe may be capable of, it’s time to eliminate the virus in your computer so that it cannot do any of this to you.
SUMMARY:
*Source of claim SH can remove it.
Remove Sabsik Trojan
To remove the Sabsik virus, one must first find and delete any malicious programs from their computer, then quit the processes of the virus, and restore their system settings.
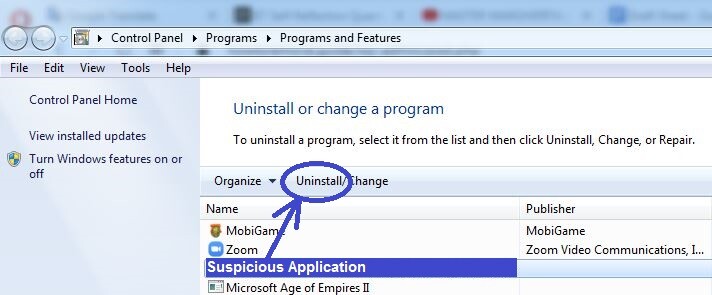
- Go to Programs and Features and from there find and delete any suspicious and potentially harmful programs that may be related to Sabsik.
- Next, open the Task Manager and check it for potentially rogue processes. If you find such processes there, quit them.
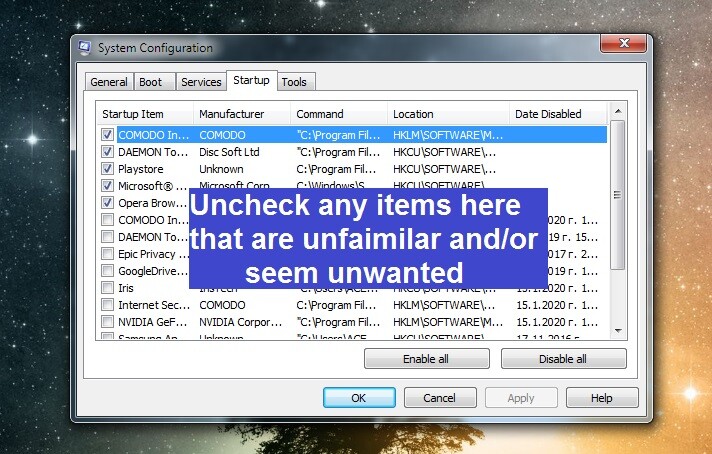
- Thirdly, go to your Hosts file, DNS settings, and Startup Items, see if any changes have been made to them by the virus, and revoke any such changes.
- Lastly, open the Registry Editor, search it for Trojan Horse items, and delete what you find to remove the Sabsik virus.
If you think you may need further help with any of the steps shown above, refer to the more detailed instructions we’ve provided in the extended guide posted below.
Extended Guide
We suggest that you bookmark the current page in your browser to be able to quickly find it later since some of the steps below will require a system restart.
Step 1
Begin by clicking the Start Menu and typing in it Programs and Features. Select the icon of the first result of the search and then look at the items shown in the list that opens. Look for programs installed around the time you started noticing that something was wrong with your system. If you notice any suspicious-looking programs, especially if you aren’t familiar with them and don’t remember installing them yourself, click them, and then select the button labelled Uninstall from the top.
Next, proceed with following the on-screen uninstallation steps, making sure that the uninstaller gets rid of everything related to the potentially unwanted program (including custom user settings and other temporary data).
Step 2
WARNING! READ CAREFULLY BEFORE PROCEEDING!
*Read more details in the first ad on this page, EULA, Privacy Policy, and full terms for Free Remover.
For this step, search for Task Manager in the Start Menu, open the first shown icon, and click the section labelled Processes.
In there, look for items with high RAM memory and CPU consumption that have unusual names and look questionable. If you spot any such items, use Google, Bing, or another trusted search engine to find more information about the suspected process/processes. If you find posts in reliable sites that say that the process may be linked to a malware threat such as Sabsik, go back to the process in the Task Manager, right-click it, open its File Location, and scan the files there using the following online malware scanner.


If malware is detected within any of the scanned files, this means that the process they are related to is malicious and should be stopped. In such cases, right-click the process again, select the End Process option, and then return to the file location folder and delete all files stored there (even the ones that didn’t get flagged as malicious by the scanner). After that, delete the actual file location folder.
If you weren’t able to eliminate any of the files, leave them be for now and complete the remaining steps. Later, come back to the location folder and make one final attempt to delete it.
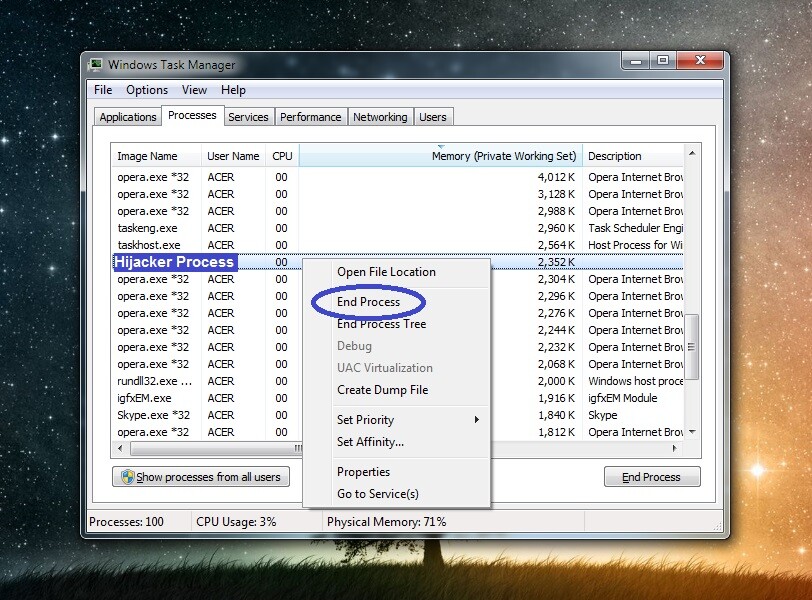
Important!: If no malware was found in any of the scanned files but the information you saw online about the processes gave you a strong reason to believe that the latter is malicious, then you should still quit the harmful process and delete its files.
Step 3
It is possible that you may have missed some of the malicious Sabsik processes during the previous step, so we suggest that you boot your PC into Safe Mode so that such processes wouldn’t be allowed to run in the computer while you are completing the remaining steps from this guide. Instructions on entering Safe Mode are available on the linked page.
Step 4
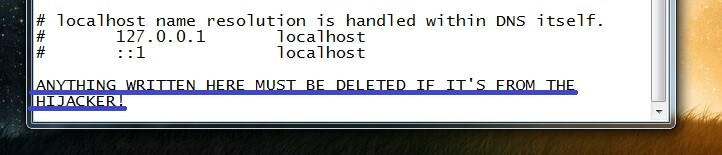
Type (copy-paste) this line %windir%/system32/Drivers/etc/hosts in the Start Menu and select the file that shows up (should be named Hosts). If you are asked about what program to use to open it, select Notepad.
When the file opens, take a look towards the bottom of the text that’s in it – if there’s any text below “localhost”, it means that a third-party program (likely Sabsik) has manipulated the file. In order to be able to tell you if the changes are indeed from the virus, we must first have a look at what’s written at the bottom of the text, so you must copy everything that’s after “localhost” and send it to us in the comments. After we determine if it is from the malware, we will reply to you, telling you if further action is required.
Again in the Start Menu, type System Configuration, press Enter or select the first result, and go to Startup.
In there, look at what items are shown in the list and if among them, you see anything suspicious, unknown, or potentially unwanted, uncheck it and then click OK.
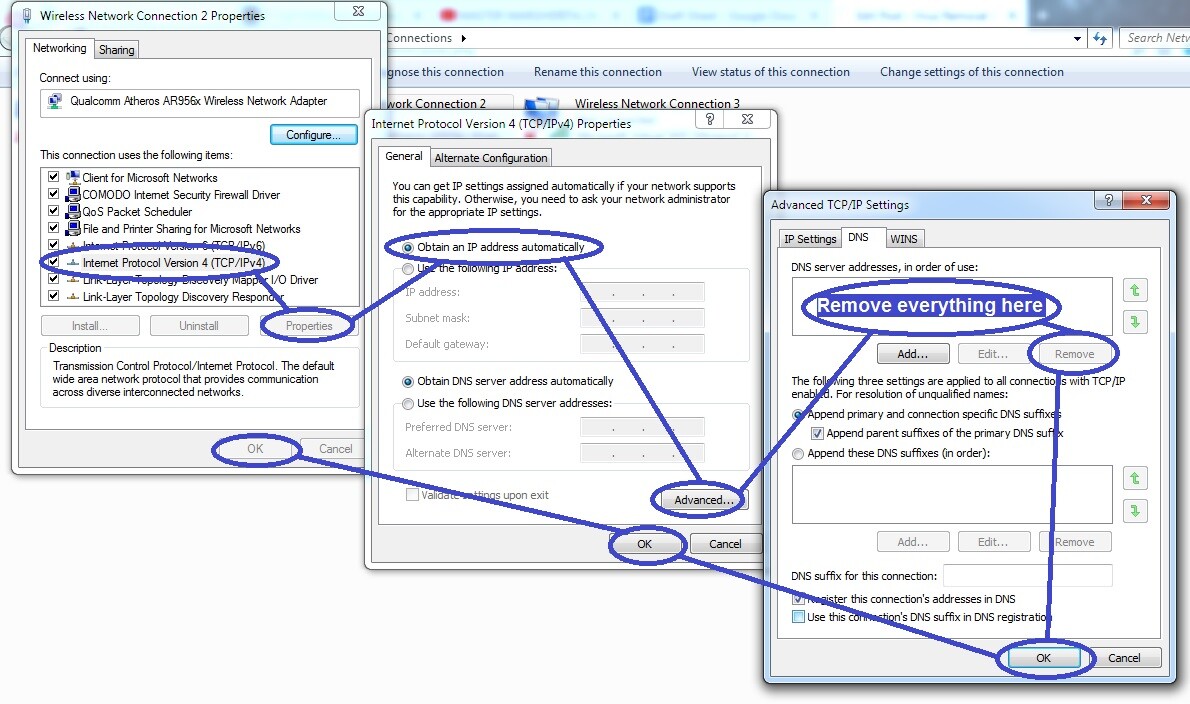
Go to the Start Menu for a third time, type Network Connections, press the Enter key, and then right-click the network you are currently using. Select its Properties and then find and click on the Internet Protocol Version 4 item. Then select Properties again and enable the Obtain an IP address automatically option in the next window. Next, proceed to the Advanced settings and there click on DNS from the top. If any IPs are shown in the list there, delete them.
Lastly, save all changes you’ve made to the DNS settings by clicking OK on each of the open windows.
Step 5
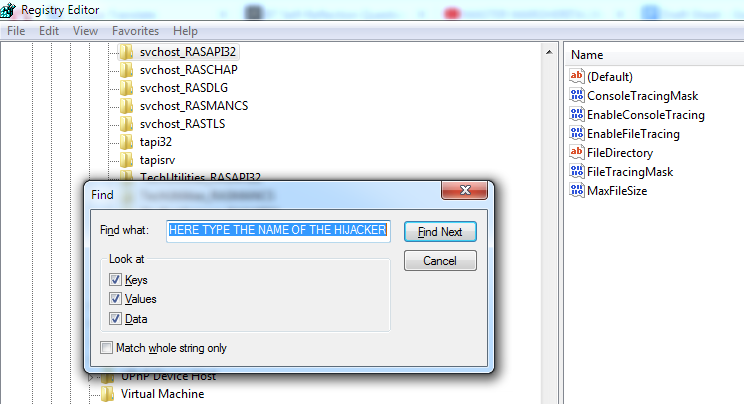
Warning!: To avoid causing harm to your system, only delete items from the Registry while completing this step if you are certain that those items are unwanted. If you cannot be sure about anything, it’s best to ask us by writing us a comment below this guide.
The first thing to do in this step is to press Winkey and R from the keyboard, type regedit, and click on OK. When a dialogue window appears asking for your Admin permission, click on Yes and this will start the Registry Editor. Once in it, select Edit from the top, go to Find, type the name of the virus (Sabsik) and click on Find Next. Whatever item gets found, delete it, then repeat the search for Sabsik, delete the next shown item, and do this until all items in the Registry that are related to the Trojan have been deleted.
After that, navigate to these directories in the left sidebar of the Registry Editor:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main
In them, look for items with seemingly random names or names that are especially long and stand out from the rest. Any such items must be deleted from those directories, but it is important to be certain that what you are deleting is not a legitimate item related to important system settings. For that reason, we once more remind you to ask us about our opinion in case of doubt.
Step 6
In some cases, these manual steps may not be enough to fully eliminate Sabsik from your computer. Therefore, if you still think that the threat is active in your system, we suggest resorting to the use of a specialized tool to get rid of the Trojan. Our recommendation for such a tool can be found on this page – the suggested anti-malware program is capable of cleaning your computer from everything related to Sabsik as well as providing it with powerful protection against other threats that may target you in the future.


Leave a Reply