Simage4.pubmatic.com
Simage4.pubmatic.com is a type of browser hijacker that is specifically aimed at Mac computers. Namely, Simage4.pubmatic.com targets the browser installed on your Mac and introduces certain changes to it.
For instance, it typically sets a new search engine as the default one and it is, thus, the one to display all your search results from then on. And users also tend to discover that their browser homepage has also been substituted with a different one by the hijacker.
Programs like Simage4.pubmatic.com, Search Marquis, Search Baron also tend to fill your browser with numerous popups, banners, box messages and various other forms of online ads. This happens regardless of the websites you visit. And speaking of visiting websites, you may be forced to visit certain sponsored ones whether you like it or not thanks to sudden page redirects that your browser undertakes without even asking you. This is the activity that usually drives users crazy and pushes them to try and remove the intrusive browser hijacker from their Macs. And thankfully, this is something that you can do in a matter of a few relatively easy steps described in the removal guide below.
Simage4.pubmatic.com for Mac
Simage4.pubmatic.com for Mac acts as an advertising tool. Simage4.pubmatic.com for Mac generates revenue for its developers thanks to all the ads it generates on your screen.
Namely, programs like this typically operate on the basis of remuneration systems such as Pay Per Click or Pay Per View, which speak for themselves. And that is why the process of promoting this product or that service is always so aggressive.
Furthermore, browser hijackers like this one tend to go the extra mile in order to ensure that they are most effective. What you don’t see is that a program like this can actually be recording your browsing activity and using it to tailor the flow of ads to your individual preferences. What’s unsettling is that this information is stored and can be distributed to various third parties for an extra profit.
What is Simage4.pubmatic.com?
Contrary to what many think, Simage4.pubmatic.com is not a virus. Simage4.pubmatic.com is a fairly harmless program that specializes in promoting various web locations, products and services. As described earlier, that is how the developers behind this type of software gain revenue.
However, the above doesn’t mean that software like Simage4.pubmatic.com is entirely safe to have on your computer either. In fact, in the long run it may actually prove to be more of a vulnerability to your system exactly because of the numerous ads and page redirects that it forces you to put up with. It may happen that you end up being exposed to certain threats such as viruses and malware. For example, you could be redirected to a page that’s been compromised by Trojan horse viruses or ransomware.
The Simage4.pubmatic App
The Simage4.pubmatic.com app most probably came bundled with some other program that you downloaded. Hence, you installed the Simage4.pubmatic.com app without realizing it. This could have been avoided if you were to opt for the more detailed advanced settings of the installer and paid close attention to every step of the process.
SUMMARY:
| Name | Simage4.pubmatic.com |
| Type | Adware |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Detection Tool |
Remove Simage4.pubmatic.com from Mac
To remove Simage4.pubmatic.com from Mac, the user must first quit the hijacker process, delete its files, and uninstall any unwanted apps and browser extensions from the computer.
- First, search in the Activity Monitor for suspicious processes related to Simage4.pubmatic.com and quit them.
- Next, visit the /Library/LaunchAgents, ~/Library/LaunchAgents, /Library/LaunchDaemons, and ~/Library/Application Support folders and delete any hijacker files located in them.
- Thirdly, go into your Applications folder and uninstall any rogue apps that may be in there.
- Lastly, to remove Simage4.pubmatic.com from Mac, clean your browsers from unwanted extensions.
Those steps are an overview of what must be done in order to delete Simage4.pubmatic.com. If you need more details on how to complete the steps, you should read the rest of the guide.
Detailed Simage4.pubmatic.com Removal
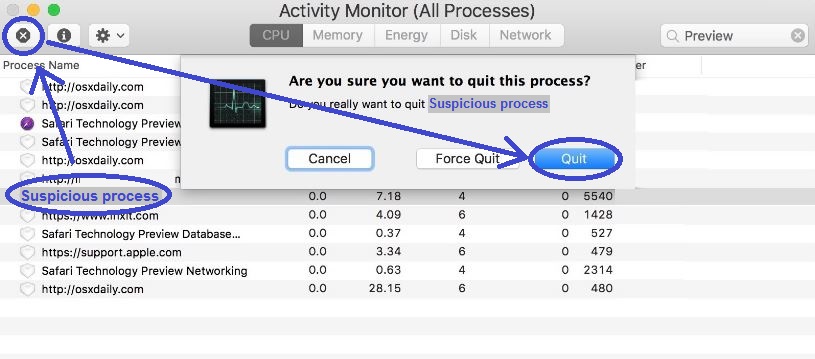
Step 1: Quitting the Simage4.pubmatic.com process(es)
Open the Activity Monitor – you can find it in Finder > Applications > Utilities. Look at what processes are shown to e using the largest amounts of CPU, RAM memory, and battery power. If you see among them ones that have odd names that don’t seem connected to any legitimate apps that you have on your Mac, then Google (look up) the name of the suspiciously-named process (or processes) and see if there are any information on the Internet that suggests the suspected process could be linked to the hijacker. If you find such information coming from a reliable source, go back to the process in the Activity Monitor, click on it,and quit it by clicking the X button in the upper-left corner.
Step 2: Delete rogue hijacker files
WARNING! READ CAREFULLY BEFORE PROCEEDING!
Next, to delete the hijacker files that may be in your system, press the Command, Shift, and G keys together to invoke the Go to Folder window. Then type /Library/LaunchAgents in the search box and select GO to open that folder.
In the folder, look for recent files (files created after Simage4.pubmatic.com got added to the system) and scan those files with our powerful online scanner that you can find below and use for free:

If one or more of the files are flagged as containing malware, delete those files.
After that, use the same method to go to the ~/Library/LaunchAgents and /Library/LaunchDaemons folders, scan their recent files, and delete the ones that get flagged as threats.
Finally, go to ~/Library/Application Support and there check for sub-folders that may be linked to Simage4.pubmatic.com. If you suspect a given sub-folder, use the scanner on the files that are inside it to figure out if it contains malware. If any folder is detected to contain malicious files, delete it.
Step 3: Check the Applications Folder
Open Finder > Applications again and look what apps are present there – anything that has been downloaded without your permission should be deleted. Also, look for and delete apps that you have downloaded from questionable sources and that you think may be the reason for the Simage4.pubmatic.com appearance on your Mac. To delete an app, simply drag it to the Trash utility and then right-click the Trash icon and Empty it.
Uninstall Simage4.pubmatic.com from Safari
To uninstall Simage4.pubmatic.com from Safari, you must delete any suspicious and unknown add-ons from the browser.
- Once you open the browser, click the Safari button/menu from the top and then go to Preferences.
- Go to the Extensions tab and look through the browser extensions listed there – try to find ones that you are unfamiliar with and/or that seem undesirable.
- If you think any of the entries may be from Simage4.pubmatic.com, delete it to uninstall Simage4.pubmatic.com from Safari.
- To make everything is back to normal, reboot the computer, go to Safari again, and surf the Internet, monitoring the browser’s behavior for some time.
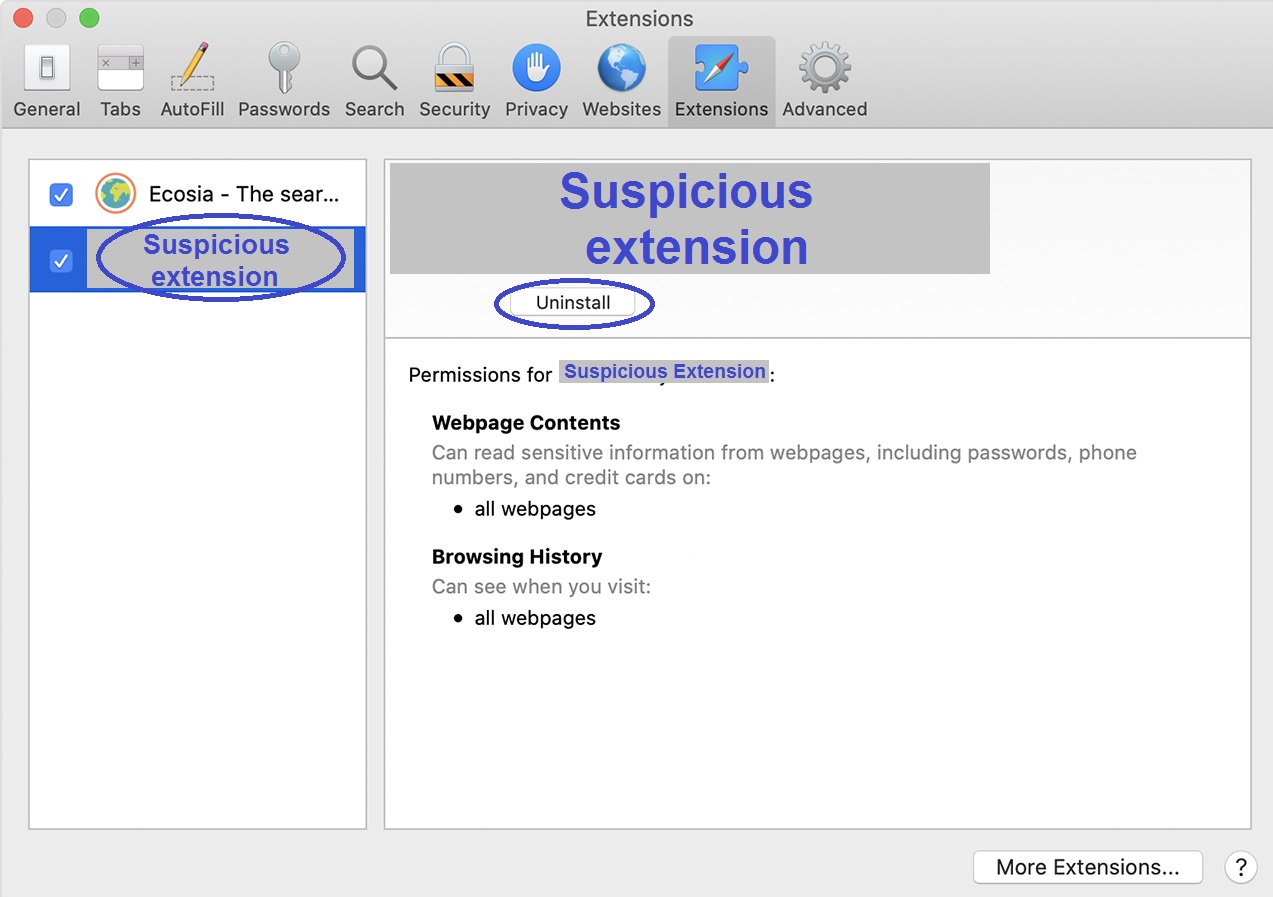
If there no longer seem to be hijacker symptoms, there’s probably no need for further actions in Safari. Still, we strongly recommend that you do a couple more things just to make sure Simage4.pubmatic.com won’t return to the browser.
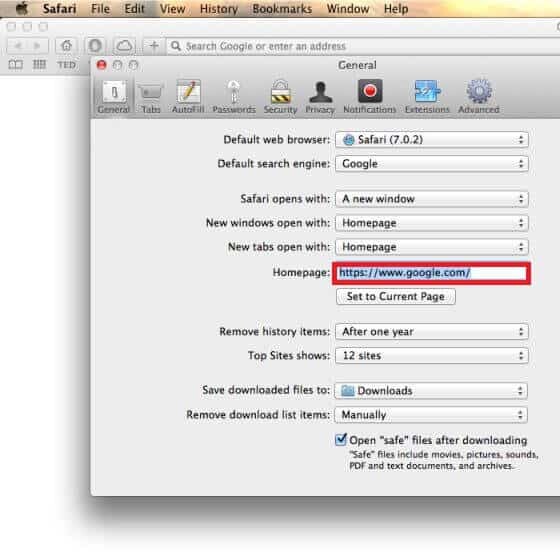
For starters, click General from Preferences and then examine the address that’s currently set as the homepage of the browser. If that address isn’t the one that the bowser used to have as its homepage before the hijacker appeared on the computer, then replace it with your previous homepage address or with another one of a site that you can trust.
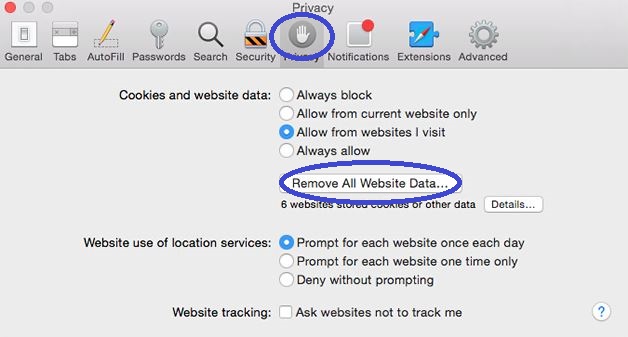
You must also go to Privacy and there select Remove All Website Data and execute the action. This will help clean any last remnants of the hijacker that may still be lying around.
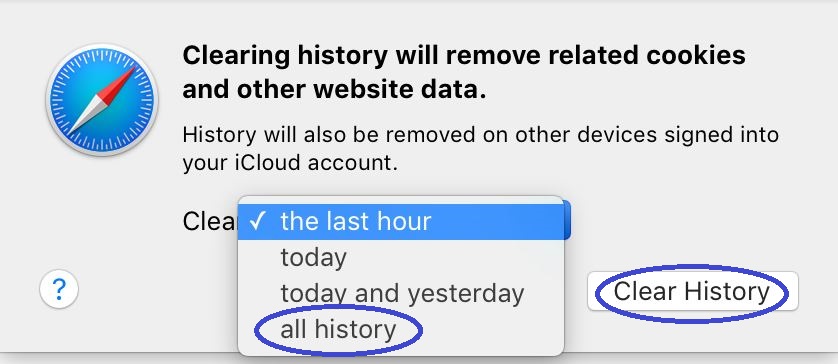
Lastly, it may be a good idea to also clean the history of Safari. For that, click History in the menu bar, then click the Clear History option, select All History, and launch the command.
If you have other browsers, check them too
If there are other browsers in the computer and not only Safari, those browsers could have been affected by Simage4.pubmatic.com too, so you have to check them as well and make sure that anything unwanted in them gets removed.
How to clean Firefox
Firstly, and most importantly, go to the Firefox menu after you start the browser, select Add-ons, and uninstall any questionable add-ons listed on the next page. After that, you may also want to check the browser plug-ins and disable the ones that seem suspicious to you.

If the hijacker has made any other changes in the browser’s settings, there’s an easy way to revoke them – follow the steps in this guide on how to refresh the settings of Firefox to make sure that there is nothing related to Simage4.pubmatic.com left in the browser.
How to clean Chrome
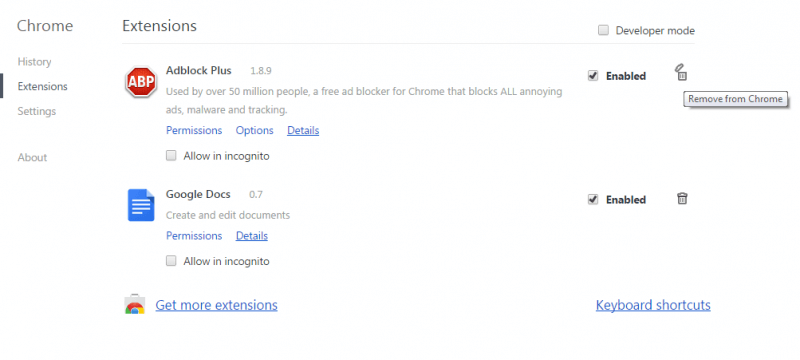
Go to the Chrome Extensions page by clicking the browser menu, hovering your mouse over More Tools, and then selecting Extensions. If you see unwanted/suspicious extensions there, first click the toggle button below them to disable them and then select Remove to uninstall the extension(s)
Following that, select Settings from the menu, go to the Search Engine settingsand then click Manage Search Engines. All search engines listed on the next page that you don’t recognize need to be blocked. To do that, select the icon with three dots next to the unknown search engines and then click the Remove from the List option.
To make sure Chrome is fully cleaned, go to this article and complete the steps for Chrome that you will find there to refresh the settings of the browser.
What if Simage4.pubmatic.com didn’t get removed?
If none of the steps thus far have helped, then it may be time to try with a professional anti-malware tool that will take care of Simage4.pubmatic.com for you. On the current page, you will find a powerful and reliable malware-removal app that we recommend for cleaning hijackers such as Simage4.pubmatic.com. In addition to finding and deleting unwanted hijackers, this software can also protect you against much more hazardous threats, including Trojans and Spyware so that your system stays protected when you are on the Internet.

Leave a Comment