Snake may expose your browser to redirects, ads, and persistent unwanted components. Install SpyHunter Pro to scan for risks, remove related threats, and enable real-time protection.
*Source of claim SH can remove it. Trial w/Credit card; image is for illustration; full terms.
*Source of claim SH can remove it.
Snake Ransomware
Snake is malicious software of the ransomware type that aims at encrypting user files and demanding a ransom for their decryption. The victims infected by Snake are typically faced with a threatening notification that prompts them to transfer a fixed amount of money to a given cryptowallet.
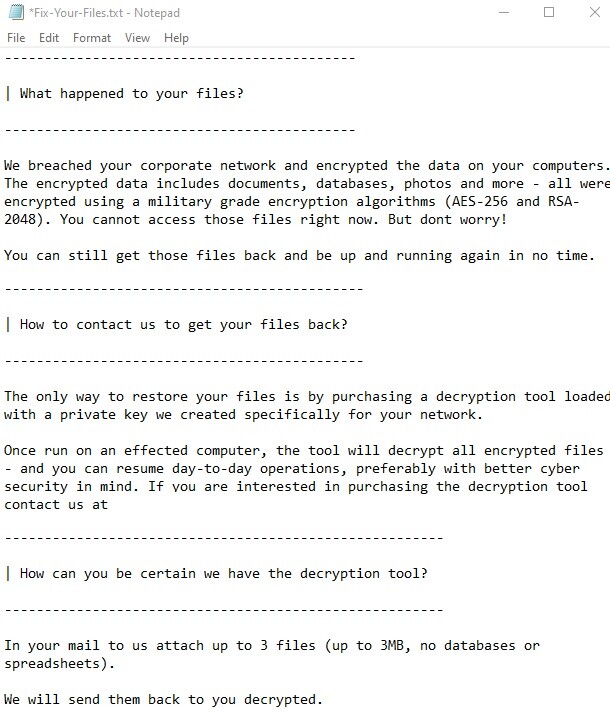
Infections of the Ransomware type are on the rise right now and they pose a serious danger to any web user and their digital information. Snake is also a Ransomware representative, which demonstrates the typical negative effects of the viruses of this category: secret file encryption, unannounced entry into your PC, use of a certain vulnerability of the system and a blackmail message that demands payment of a ransom. The following article discusses all these features in general and suggests alternative methods to remove Snake and avoid the ransom payment that the criminals demand.
The Snake Malware
The Snake malware is a ransom-demanding infection that encrypts a number of valuable user files and then requires a ransom payment to reverse it. Typically, the Snake malware informs its victims about the applied file encryption through a ransom-demanding message on their screen.
Ransomware is a type of software that initially emerged as a malicious threat in Russia at the end of the 20th century. Ever since then, millions of Ransomware-based programs have been continuously emerging. Today we can even distinguish different Ransomware subtypes. Among them is the most common form – the file-encrypting Ransomware. The representatives of this virus subtype are designed to encrypt the files on your computer. This means that these applications search the entire content of your device and pick files that are very valuable to you. Then, they proceed to secure these files with a special encryption code. Usually, after the file-encryption process is complete, Snake surprises you with a ransom-demanding notification on your screen. The role of this notification is to blackmail you to pay a certain amount of money for the decryption of the sealed information. The notification usually contains payment information such as a preferred currency and a deadline.
The Snake Virus
The Snake virus is a regular user file the file extension of which has been changed after the Snake file encryption has taken place. The Snake file cannot be opened by any software and typically returns an error message when users try to click on it.
Unfortunately, no matter what you do, whether you pay the ransom to the hackers or you use some other file-recovery alternatives, there is no guarantee about the future of your encrypted information. This is what makes Ransomware infections so bad and Snake is not an exception – no intervention against this virus can ensure that you will decrypt the data it has encoded. What we should say here is that it’s up to you to decide how exactly to deal with the infection. Our best advice will be to try to remove this hazard from your device using professional software, a removal guide or the assistance of an expert. Keep the ransom payment as your very last resort because by paying it, you can only encourage the hackers to try the harassment technique on more people.
SUMMARY:
*Source of claim SH can remove it.
Remove Snake Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.


Leave a Reply