.Spade
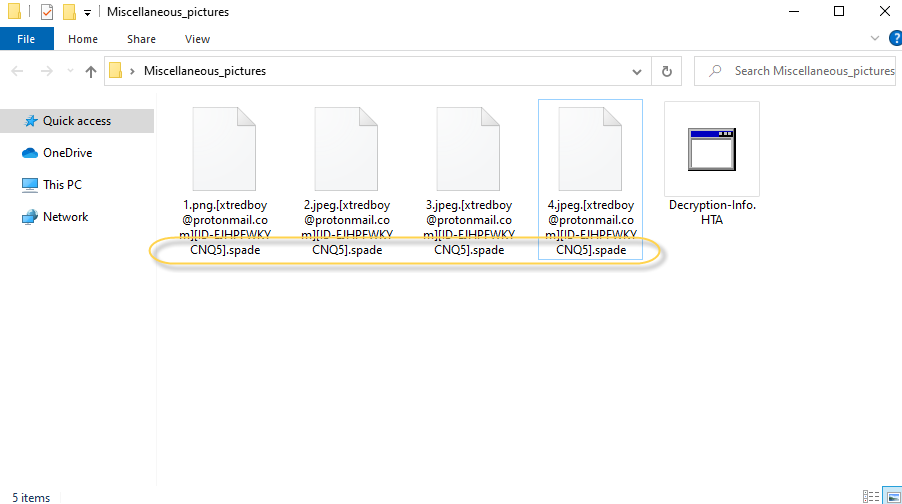
.Spade is a computer virus that is programmed to find potentially valuable files in its victims’ computers and lock them. Once the targeted files are locked, .Spade proceeds to ask the victim to pay a ransom for the recovery of their files.
The .Spade File complex encryption
This method of cyber blackmailing is nothing new and has been around for decades. Over the years, the hackers who use it have managed to perfect it, turning ransomware viruses such as .Spade into some of the nastiest forms of malware on the Internet. It is especially difficult to stop a new ransomware virus such as this one because the majority of antivirus programs wouldn’t have it included in their databases and so detecting the virus in time, before it has managed to lock your files, is nearly impossible even if you have an otherwise strong and reliable antivirus.
Most users learn that there is ransomware on their computer either once they try to access a given file that has already been encrypted or once a ransom message from the virus appears on their screen, informing them that their only hope for restoring their files is if they follow the strict instructions from the message to pay the demanded ransom. Of course, not everybody has the required money readily available and even if you are among the people who do, we still do not advise you to go for this course of action.
The .Spade virus
The .Spade virus is a member of the VoidCrypt ransomware file-locking type of viruses and its goal is to block the access to your files. The .Spade virus will not release your data until you send money to its creators.
The problem here is that you cannot really be sure of what happens after you send the requested sum. Maybe you do indeed get the decryption key, in which case the ransom payment would have been a necessary compromise. However, the question you should ask yourself now if .Spade is keeping your files hostage at the moment is whether there is anything stopping the hackers from keeping the decryption key and not sending it to you even after you’ve paid them. Usually, the answer would be negative and so it seems that it is better to at least first try some other possible solutions before you come back to the ransom payment as a potential option.
The .Spade file
The .Spade file is a file with a changed extension that has been encrypted by the ransomware and can’t be opened without the private decryption key. The .Spade file isn’t harmful to the computer but you won’t be able to access it while it stays encrypted.
If you desperately need to recover your data, paying is still an option but we suggest that you first give try the instructions in our guide and if nothing from there works for you, you can always try the ransom payment (although we still don’t recommend that).
SUMMARY:
| Name | .Spade |
| Type | Ransomware |
| Detection Tool |
Remove .Spade Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible). You can find the removal guide here.

Leave a Comment