VoidCrypt
VoidCrypt is malware of the ransomware type that utilizes the encryption method in order to block users from accessing valuable data stored on their machines. Due to its file encryption abilities, VoidCrypt is categorized as a dangerous cryptovirus that needs to be removed.
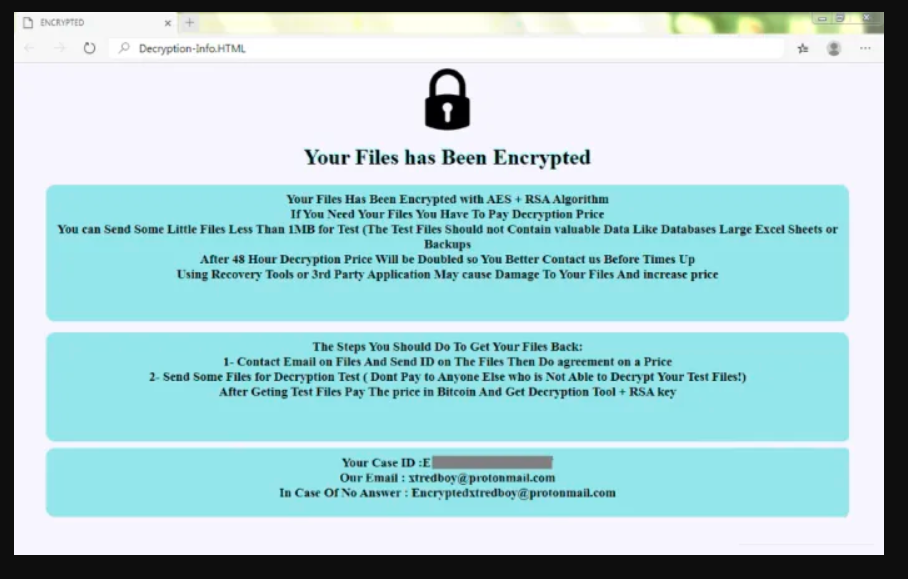
The VoidCrypt Decryption-Info.HTA ransom note
The method of data encryption is normally used to protect sensitive files by rendering them unavailable to anyone who is not allowed to access them. Only users who have a special decryption key are able to unlock, modify and use the encrypted files and without it, these files are simply encoded pieces of data.
File encryption is widely used in different sectors of the industry and finds its implementation in jobs that include the processing of confidential and critical details that need to remain secure and protected from unwanted access.
Sadly, people with malicious intentions have found a way to use this very beneficial file protection mechanism against users. You’ve undoubtedly heard of the term “ransomware” in recent years. In general, this is a type of malware primarily used to extort money and blackmail users by restricting access to their digital files or their entire computer. One of the most problematic ransomware types are the cryptoviruses, which specialize in restricting users’ access to their digital files thorough encryption. VoidCrypt is an exact representative of this cryptovirus subcategory and, in the next lines, we will show you how to remove it.
The VoidCrypt virus
The VoidCrypt virus is a malicious piece of code that, as soon as it reaches your computer and identifies your files will initiate an encoding process that will render them inaccessible. The VoidCrypt virus will then send you a ransom notice that provides guidance on how to send money to the hackers who control the infection.
The money is needed in exchange for the decryption key to your files. However, in case that VoidCrypt or any other ransomware like .Ogdo or .Kasp has breached your device, we don’t encourage you to risk your money by sending it to anonymous hackers since you may not get anything in exchange for them. Instead, we suggest that you explore alternative solutions, such as the removal guide below and remove the ransomware from your system.
The .Void file
When the .Void file has been deleted, you will be able to safely use your machine again, without thinking about the ransomware encrypting any new files you create. However, the issue is that even though the .Void file is removed, the encrypted files may still remain locked for good.
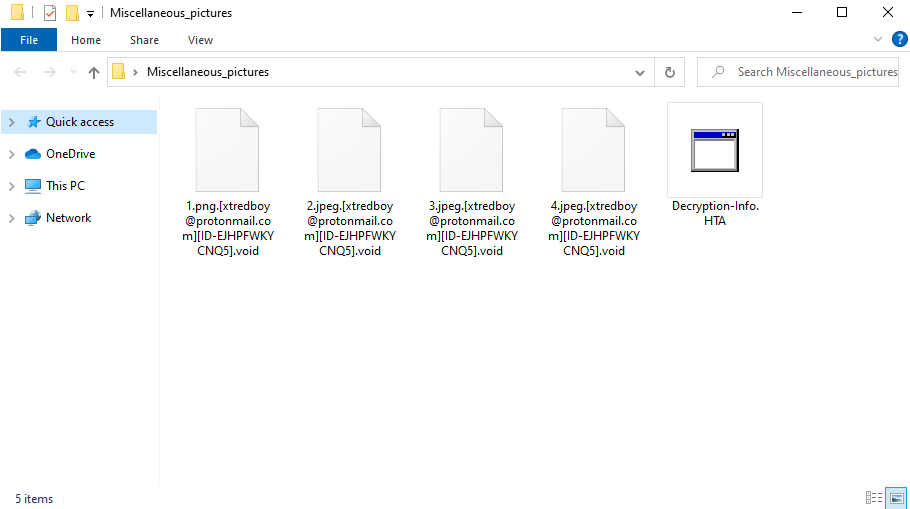
The .Void File Extension
That’s why you may need further assistance to access these files and this part will definitely be very challenging. The problem is each cryptovirus is different and requires different decryption key, so it is not possible to use what works for one ransomware virus to tackle another. We have provided general tips for data recovery on our website which you can use for free, but we cannot guarantee their effectiveness in all cases. However, we should note that exploring alternatives is preferable because this may, at least, save you a significant sum of money that you may lose by paying a ransom to unknown offenders who would probably decide not to give you the decryption key that can decrypt your records.
SUMMARY:
| Name | VoidCrypt |
| Type | Ransomware |
| Detection Tool |
Remove VoidCrypt Ransomware
You are dealing with a ransomware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to decrypt and recover your encrypted files (if it is currently possible).
You can find the removal guide here.

Leave a Comment