This page aims to help you remove .Stone File Virus for free. Our instructions also cover how any .Stone file can be recovered.
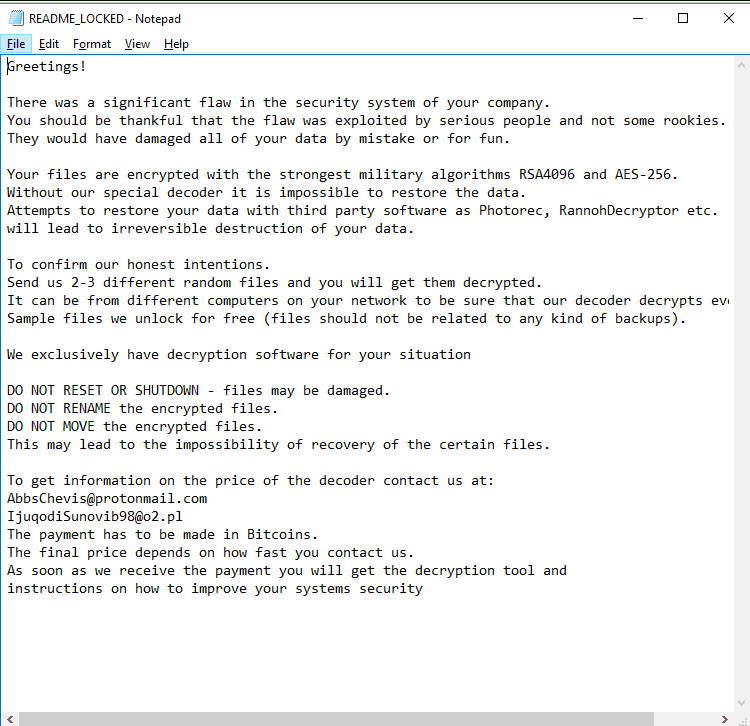
After the ransomware encrypt your files, it leaves a _readme.txt file with instructions to follow:
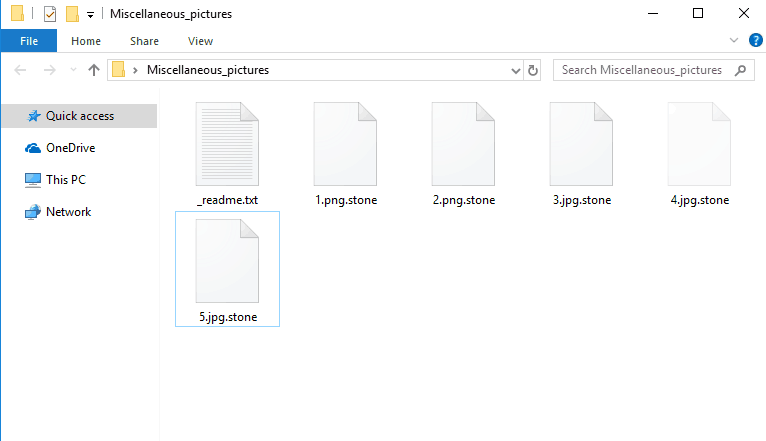
The text down below will reveal to you what you should be aware of with regards to a form of malevolent software referred to as .Stone. More specifically, the actual malware type this program is characterised as is Ransomware. This type of malware is able to encode various software documents on your PC. Right after the file encryption of all the targeted data gets carried out, the Ransomware victim in most cases receives a notification describing all that has taken place inside their PC and telling the user that they must pay a ransom if they wish to bring the inaccessible data back to its previous accessible state. Normally, this kind of intimidating message is there to provide you with the hackers’ directions on how to transact the money for the ransom. Furthermore, warnings could also be added to the message – you may be warned that unless you DO pay, your files will stay blocked permanently and the decryption key would be deleted. If you want to find out more regarding this malware type and regarding the potential solutions for the issues brought on by it, our article here and the manual guide attached to it may turn out to be rather helpful.
Tips for the future security of your computer and files
And once you have dealt with .Stone, .Mogera or .Rezuc it is vital that you make sure that you don’t have to face such malware ever again. You can do that by preparing yourself for any potential future Ransomware infections. In fact, fending off Ransomware is rather simple when compared to removing such viruses after they’ve entered your computer.
One of the first things you need in order to decrease the danger of potential future Ransomware encounters is a data backup on a different location that isn’t linked to the Computer (you can also use a cloud service for that). Undoubtedly, if you have got available copies of your valuable files, even in case the original ones get sealed by a Ransomware, the cyber criminals are going to be deprived of leverage upon which they might blackmail you.
One other really important security and safety tip to think about is your computer’s exposure to potential online risks. One important thing that you ought to be really careful with are the various spam texts and emails that you may be sent because those might sometimes carry hazardous malware infections with them. Whatever appears shady and obscure will need to be avoided even if it seems you have received it from a person that you know given that there is the possibility that their PC may have been compromised.
One other probable source of Ransomware are the many forms of malicious online adverts. Because it is sometimes hard to tell apart regular ads from harmful ones, you should always be careful. Sad to say, a number of those online ads could include malware code. Usually, going to questionable websites that may be illegitimate and coming into contact with their ads drastically increases the chances of landing upon some misleading advertisement that may compromise the security of your machine. Just stay away from dubious and sketchy content when on the Internet and you won’t ever regret it.
SUMMARY:
Remove .Stone File Virus Ransomware
Search Marquis is a high-profile hijacker – you might want to see if you’re not infected with it as well.

Leave a Reply