Feelmyfly.info
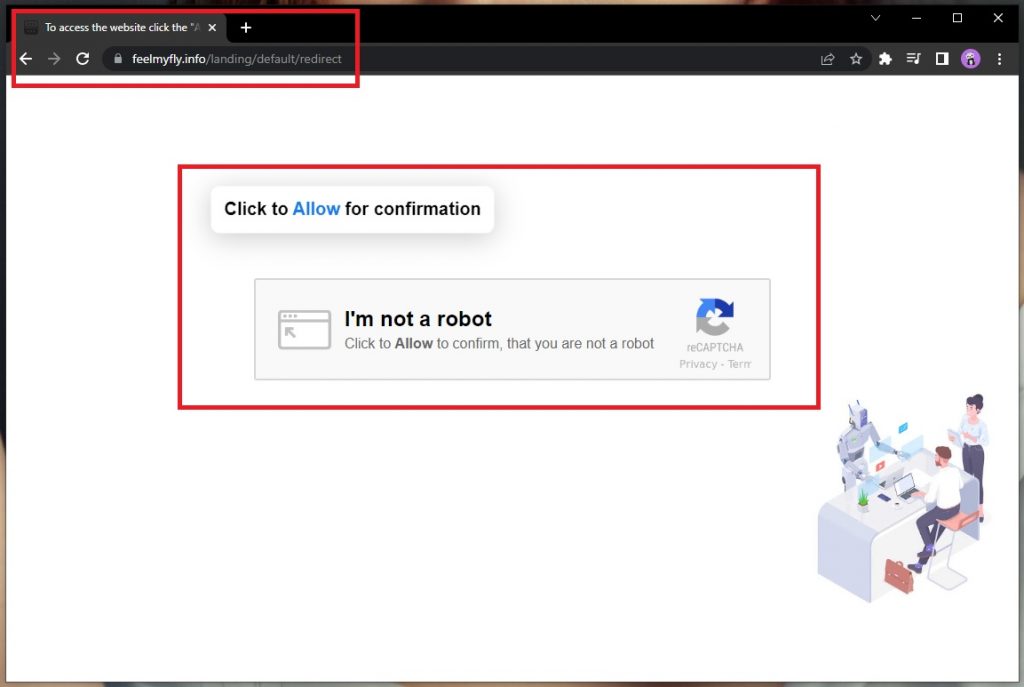
Feelmyfly.info is a type of software application that falls into the category of browser hijackers. Feelmyfly.info can embed itself in your main Chrome, Firefox, Edge or other popular web browser and change some of its settings.
For instance, in time it’s not uncommon for your computer’s performance to become compromised and you to start experiencing noticeable system slowdowns. Furthermore, browser crashes and freezes aren’t unheard of either due to the constant background activity of the browser hijacker.
Feelmyfly
Speaking of which, there are processes that software like Feelmyfly initiates that users aren’t usually aware of. Collection of browsing-related data is one thing that often causes issues. It’s typically done in the name of targeted advertising, as browser hijackers like Feelmyfly, BestSearch.ai, Mintnav mostly operate on the basis of PPC and PPV remuneration schemes. But aside from that, the data can be repackaged and sold to third parties by the developers as valuable marketing information and you won’t even know who will end up in possession of it.
But that’s not where the potential negative effects end.
All the many popups and banners that keep appearing on your screen during your online sessions may prove to be potential security hazards as well. There’s no telling whether the websites that they may link to are at all safe. And that, in turn, means that you risk landing on web locations that can have viruses and malware lurking on them. So if you’d rather avoid running into ransomware, Trojans, worms and various other harmful scripts, we would advise you to stay away from any and all advertising materials you come across online.
SUMMARY:
| Name | Feelmyfly.info |
| Type | Browser Hijacker |
| Detection Tool | Some threats reinstall themselves if you don't delete their core files. We recommend downloading SpyHunter to remove harmful programs for you. This may save you hours and ensure you don't harm your system by deleting the wrong files. |
Please follow all the steps below in order to remove Feelmyfly.info!
How to remove Feelmyfly.info
- First, click the Start Menu on your Windows PC.
- Type Programs and Settings in the Start Menu, click the first item, and find Feelmyfly.info in the programs list that would show up.
- Select Feelmyfly.info from the list and click on Uninstall.
- Follow the steps in the removal wizard.
If you have a Mac virus, please use our How to remove Ads on Mac guide.
If you have an Android virus, please use our Android Malware Removal guide.
If you have an iPhone virus, please use our iPhone Virus Removal guide.
Read more…
What we suggest you do first is, check the list of programs that are presently installed on the infected device and uninstall any rogue software that you find there:
- From the Start Menu, navigate to Control Panel ->>> Programs and Features ->>> Uninstall a Program.
- Next, carefully search for unfamiliar programs or programs that have been installed recently and could be related to Feelmyfly.info.
- If you find any of the programs suspicious then uninstall them if they turn out to be linked to Feelmyfly.info.
- If a notification appears on your screen when you try to uninstall a specific questionable program prompting you to just alter it or repair it, make sure you choose NO and complete the steps from the removal wizard.
Remove Feelmyfly.info from Chrome
- Click on the three dots in the right upper corner
- Go to more tools
- Now select extensions
- Remove the Feelmyfly.info extension
Read more…
- Once you open Chrome, click on the three-dots icon to open the browser’s menu, go to More Tools/ More Options, and then to Extensions.
- Again, find the items on that page that could be linked to the malware and/or that might be causing problems in the browser and delete them.
- Afterwards, go to this folder: Computer > C: > Users > *Your User Account* > App Data > Local > Google > Chrome > User Data. In there, you will find a folder named Default – you should change its name to Backup Default and restart the PC.
- Note that the App Data folder is normally hidden so you’d have to first make the hidden files and folders on your PC visible before you can access it.
How to get rid of Feelmyfly.info on FF/Edge/etc.
- Open the browser and select the menu icon.
- From the menu, click on the Add-ons button.
- Look for the Feelmyfly.info extension
- Get rid of Feelmyfly.info by removing it from extensions
Read more…
If using Firefox:
- Open Firefox
- Select the three parallel lines menu and go to Add-ons.
- Find the unwanted add-on and delete it from the browser – if there is more than one unwanted extension, remove all of them.
- Go to the browser menu again, select Options, and then click on Home from the sidebar to the left.
- Check the current addresses for the browser’s homepage and new-tab page and change them if they are currently set to address(es) you don’t know or trust.
If using MS Edge/IE:
- Start Edge
- Select the browser menu and go to Extensions.
- Find and uninstall any Edge extensions that look undesirable and unwanted.
- Select Settings from the browser menu and click on Appearance.
- Check the new-tab page address of the browser and if it has been modified by the malicious program or another unwanted app, change it to an address that you’d want to be the browser’s new-tab page.
How to Delete Feelmyfly.info
- Open task manager
- Look for the Feelmyfly.info process
- Select it and click on End task
- Open the file location to delete Feelmyfly.info
Read more…
- Access the Task Manager by pressing together the Ctrl + Alt + Del keys and then selecting Task Manager.
- Open Processes and there try to find a process with the name of the unwanted software. If you find it, select it with the right button of the mouse and click on the Open File Location option.
- If you don’t see a malicious process in the Task Manager, look for another suspicious process with an unusual name. It is likely that the unwanted process would be using lots of RAM and CPU so pay attention to the number of resources each process is using.
- Tip: If you think you have singled out the unwanted process but are not sure, it’s always a good idea to search for information about it on the Internet – this should give you a general idea if the process is a legitimate one from a regular program or from your OS or if it is indeed likely linked to the adware.
- If you find another suspicious process, open its File Location too.
- Once in the File Location folder for the suspicious process, start testing all of the files that are stored there by dragging them to our free online scanner available below.
- Each file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is free and will always remain free for our website's users.This file is not matched with any known malware in the database. You can either do a full real-time scan of the file or skip it to upload a new file. Doing a full scan with 64 antivirus programs can take up to 3-4 minutes per file.Drag and Drop File Here To Scan
 Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared.
Analyzing 0 sEach file will be scanned with up to 64 antivirus programs to ensure maximum accuracyThis scanner is based on VirusTotal's API. By submitting data to it, you agree to their Terms of Service and Privacy Policy, and to the sharing of your sample submission with the security community. Please do not submit files with personal information if you do not want them to be shared. - If the scanner finds malware in any of the files, return to the Processes tab in the Task Manager, select the suspected process, and then select the End Process option to quit it.
- Go back to the folder where the files of that process are located and delete all of the files that you are allowed to delete. If all files get deleted normally, exit the folder and delete that folder too. If one or more of the files showed an error message when you tried to delete them, leave them for now and return to try to delete them again once you’ve completed the rest of the guide.
How to Uninstall Feelmyfly.info
- Click on the home button
- Search for Startup Apps
- Look for Feelmyfly.info in there
- Uninstall Feelmyfly.info from Startup Apps by turning it off
Read more…
- Now you need to carefully search for and uninstall any Feelmyfly.info-related entries from the Registry. The easiest way to do this is to open the Registry Editor app (type Regedit in the windows search field and press Enter) and then open a Find dialog (CTRL+F key combination) where you have to type the name of the threat.
- Perform a search by clicking on the Find Next button and delete any detected results. Do this as many times as needed until no more results are found.
- After that, to ensure that there are no remaining entries lined to Feelmyfly.info in the Registry, go manually to the following directories and delete them:
- HKEY_CURRENT_USER/Software/Random Directory.
- HKEY_CURRENT_USER/Software/Microsoft/Windows/CurrentVersion/Run/Random
- HKEY_CURRENT_USER/Software/Microsoft/Internet Explorer/Main/Random
Browser hijackers get their name due to their ability to ‘take over’ the host browser by altering its behavior. Some of the most common symptoms of a browser hijacker infection include changes made to your default search engine and homepage, for example. Other sure signs of the presence of such software in your system are the sudden increase in the quantities of online ads that you see on your screen during browsing sessions.
Popups, banners, box messages and various other online advertising materials can be lining every site you visit and making it difficult to navigate the different pages. Furthermore, your browser may start to trigger sudden page redirects to various websites trying to sell you something. That, too, is a direct result of Feelmyfly.info’s activity on your computer.
But these are just the effects that you can see on the surface. In the long run and upon deeper inspection, you’ll find that software like Feelmyfly.info can actually have much more extensive consequences for you and your system.
How to protect from Feelmyfly.info and other browser hijackers
The easiest way to minimize the risk of such encounters is by uninstalling the source of these ads – Feelmyfly.info. There is a detailed guide with step-by-step instructions on how to entirely get rid of this browser hijacker and restore your browser’s original settings. And if you’d like to have a more thorough scan of your system for any other potentially unwanted programs, you can use our specialized removal tool – also available on this page.



Leave a Comment