*Source of claim SH can remove it.
SysWin.exe
SysWin.exe malware is something that you should make sure to keep away from your computer if you want to have a clean and a well-functioning machine. The SysWin.exe virus can be devastating and the type of damage and issues they could cause may vary greatly.
Trojans can corrupt data on your PC or mess with important OS files to cause malfunction to your PC and they could also potentially spy on you or sneak more viruses inside your PC. There are many other possibly ways in which a Trojan could cause harm your computer or your virtual identity and we will elaborate upon the potential negative effects of such a virus down below, in this article. The main reason for the writing of this post, however, is one particular Trojan Horse infection that goes under the name of SysWin.exe Virus and has been recently reported by a number of users and researchers. This Trojan version is one of the latest and, possibly, one of the more advanced ones so, if you want to keep your machine protected against it, we highly recommend you stay with us and read the rest of the current post in order to acquire some essential and helpful information and tips regarding this new malware threat. Due to the fact that a lot of you have likely come to this page in search of a method to remove SysWin.exe Virus from their machines as it has already gotten there, we have made sure to provide our readers with a guide where we have included different steps and methods for eliminating the virus and restoring the computer back to its regular state. Make sure to make use of our removal guide for SysWin.exe Virus if this insidious infection has managed to infiltrate your system.
Important advice
Trojans are notoriously difficult to detect since in most cases there aren’t any specific symptoms that they tend to trigger. Because of this, we advise you to always have a reliable and strong security program on your computer as this is one of the few relatively effective methods for intercepting attacks from this type of malware. Also, we already mentioned what the most common distribution techniques for Trojans are so make sure to avoid any online content that seems questionable and suspicious. Remember – it’s always better to simply keep the threat away from your machine as opposed to having to deal with its negative effects afterwards.
Trojan Horse infections
A major factor that plays a huge role when it comes to Trojan Horse attacks is the way such viruses manage to get inside their victims’ computers. Most typical viruses of this type rely on the user making a mistake which would allow the malware to get inside the computer and gain Administrative privileges. Such a mistake could be opening a spam e-mail and downloading its file attachment, agreeing to install a certain (fake) update request that is suggested by some shady website, executing a file that carries the malware (while thinking it is a legitimate piece of software), installing a pirated program that is actually used to distribute the Trojan as well as many other similar actions. The bottom line is that, in most cases, Trojans such as SysWin.exe come disguised as something that initially seems safe and maybe even useful or interesting to the user. Once the infected piece of content gets interacted with, provided that the customer is currently using an Administrator account, the malware would gain the same privileges and would then be able to carry out whatever malicious task it has been programmed to execute. As far as what a Trojan Horse could be programmed to do, here are couple of examples:
- Such a virus could, as mentioned above, be used to cause severe damage to the infected system by deleting important OS data, messing with the Registry editor, triggering freezes, errors and crashes (Blue Screen of Death crashes are particularly common).
- Also, a Trojan might spy on you by tracking your keystrokes, taking screenshots from your screen, gathering telemetry data or even looking inside your room through your webcam.
- Another possibility is when Trojans are used for backdoor purposes. In such a case, the malware could load other viruses inside the targeted machine, a common example here is when Trojans are used as backdoor for Ransomware.
- Additionally, it is possible that such a malware piece could force your computer to execute tasks such as distributing spam messages to other users, mining cryptocurrencies for the hackers or participating in malicious large-scale campaigns such as DDoS attacks.
Note that those are only some of the potential capabilities of such viruses and oftentimes Trojans van be reprogrammed and repurposed to do something else which is why we cannot really tell you what SysWin.exe’s Virus exact agenda would be in each specific infection instance.
SUMMARY:
| Name | SysWin.exe |
| Type | Trojan |
| Detection Tool |
*Source of claim SH can remove it.
How to Remove SysWin.exe Virus
You are dealing with a malware infection that can restore itself unless you remove its core files. We are sending you to another page with a removal guide that gets regularly updated. It covers in-depth instructions on how to:
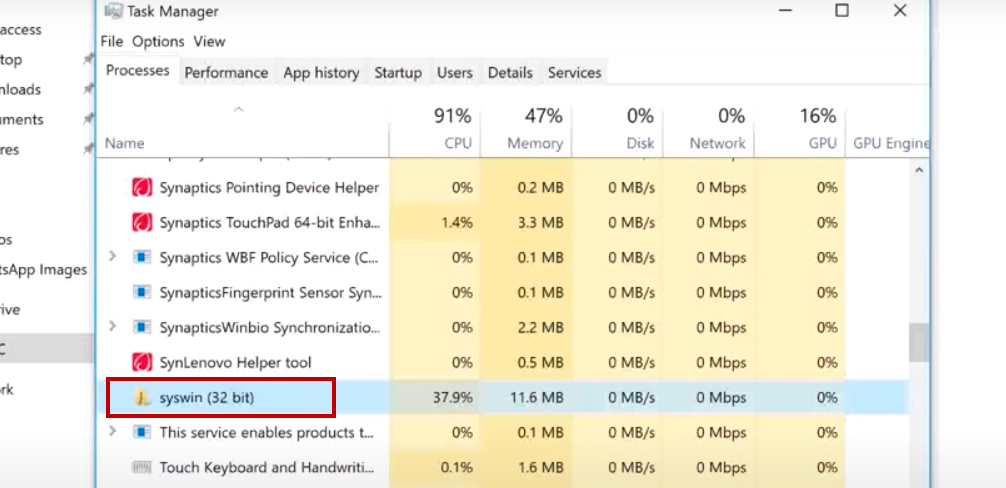
1. Locate and scan malicious processes in your task manager.
2. Identify in your Control panel any programs installed with the malware, and how to remove them. Search Marquis is a high-profile hijacker that gets installed with a lot of malware.
3. How to clean up and reset your browser to its original settings without the malware returning.
You can find the removal guide here.
For mobile devices refer to these guides instead: Android , iPhone

Hi there,
I just went through step 4 and found other IP addresses under “Localhost”.
Please instruct me.
Thank you.
Hello, we advise you to send use the IP addresses that you’ve found under Localhost so taht we can verify that they are indeed not supposed to be in your Hosts file. You will most probably have to delete them from your Hosts file, save the changes and then complete the rest of the guide.
hey, am having a problem with microsoft word and excel icons may due to the corruption by syswin .exe virus. how can recover from this?
Hi kuku kabwe,
did you follow the link provided in the guide on this page?